Letsdefend Malware Analysis Challenges Remote Working

Malware Analysis Skill Path Letsdefend Hey there! hack the box and letsdefend accounts are becoming one. if you use both platforms, please link them now to avoid any disruption to your access. This challenge is perfect for beginners and serves as a primer for using virustotal for triage, rather than focusing on static analysis of the malicious file directly. however, it offers great practice opportunities for all skill levels. sounds like fun, right? let’s get into it!.

Malware Analysis рџћ Letsdefend Letsdefend is a blue team training platform. this writeup is a challenge on letsdefend. In this challenge, we were tasked with analyzing a suspicious excel spreadsheet delivered via a zip archive. the goal was to determine whether the file was malicious, identify its behaviors, and. The remote working challenge is completed successfully. this easy level challenge allows us to use virustotal and analyze a malicious xls file to find creation time, dropped files, c2 urls and much more !. Letsdefend malware analysis challenges remote working askar | cybersec 🔐 307 subscribers subscribe.
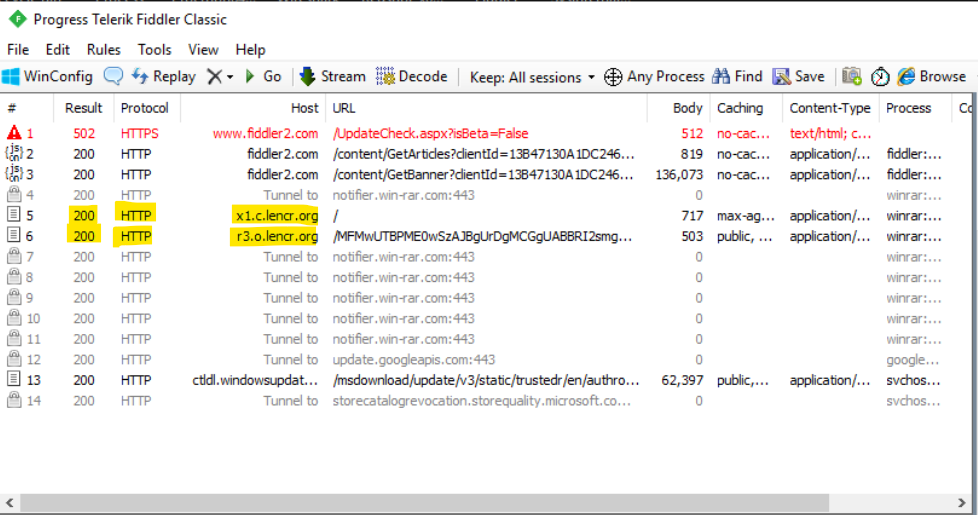
Letsdefend Dynamic Malware Analysis Example 1 Persecure My The remote working challenge is completed successfully. this easy level challenge allows us to use virustotal and analyze a malicious xls file to find creation time, dropped files, c2 urls and much more !. Letsdefend malware analysis challenges remote working askar | cybersec 🔐 307 subscribers subscribe. In this challenge, you’ll analyze a suspicious excel file to uncover its origins, behavior, and potential threats. Hands on soc analyst writeups from letsdefend labs, documenting incident investigations in english and french with iocs, analysis, and remediation steps. soc analyst writeups letsdefend remote working challenge eng.md at main · sieger05 soc analyst writeups. We can upload the file into virustotal to examine some details. question 1. what is the date the file was created? the history section of the details tab will indicate the creation time of the malware. question 2. with what name is the file detected by bitdefender antivirus?. A collection of write ups from the best hackers in the world on topics ranging from bug bounties and ctfs to vulnhub machines, hardware challenges and real life encounters.

Letsdefend Dynamic Malware Analysis Example 2 Persecure My In this challenge, you’ll analyze a suspicious excel file to uncover its origins, behavior, and potential threats. Hands on soc analyst writeups from letsdefend labs, documenting incident investigations in english and french with iocs, analysis, and remediation steps. soc analyst writeups letsdefend remote working challenge eng.md at main · sieger05 soc analyst writeups. We can upload the file into virustotal to examine some details. question 1. what is the date the file was created? the history section of the details tab will indicate the creation time of the malware. question 2. with what name is the file detected by bitdefender antivirus?. A collection of write ups from the best hackers in the world on topics ranging from bug bounties and ctfs to vulnhub machines, hardware challenges and real life encounters.
Comments are closed.