It Security Operations Analyzing Different Soc Deployment Models Ppt

It Security Operations Analyzing Different Soc Deployment Models Ppt This insightful deck offers a detailed outline, guiding you through integration strategies, benefits, and challenges, empowering your organization to enhance security posture and operational efficiency. It security operations analyzing different soc deployment models ppt powerpoint icon sample slide01 free download as pdf file (.pdf) or view presentation slides online.
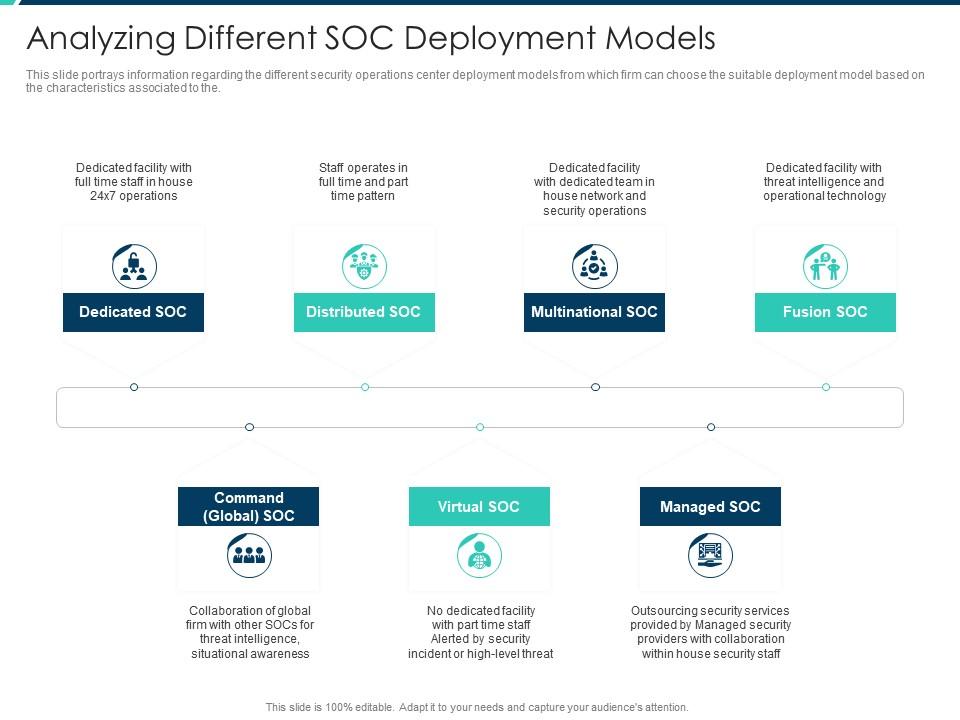
Analyzing Different Soc Deployment Models Security Operations This is a information and technology security operations analyzing different soc deployment models rules pdf template with various stages. focus and dispense information on seven stages using this creative set, that comes with editable features. This presentation by reza adineh introduces a modern, strategic, and threat informed soc model designed for today’s cloud first, hybrid, and budget constrained environments. Compare and contrast different soc deployment options – from in house and hybrid models to dedicated and outsourced soc – to determine the best fit for your organization's needs and resources. This pdf provides an in depth look into the daily operations and key roles within a modern security operations center (soc). from tier 1 analysts to threat hunters and incident response teams, it explains how each function contributes to identifying, analyzing, and neutralizing cyber threats.
Enterprise Security Operations Analyzing Different Soc Deployment Compare and contrast different soc deployment options – from in house and hybrid models to dedicated and outsourced soc – to determine the best fit for your organization's needs and resources. This pdf provides an in depth look into the daily operations and key roles within a modern security operations center (soc). from tier 1 analysts to threat hunters and incident response teams, it explains how each function contributes to identifying, analyzing, and neutralizing cyber threats. Enhance your cybersecurity strategy with our fully editable security operations center (soc) powerpoint presentations. tailor the content to fit your organization's needs and effectively communicate your security protocols. Boost your presentations with soc operating model powerpoint templates crafted for clarity and engagement. examples include: it security operations analyzing different soc. Impress your team and boss with beautiful analyzing different soc deployment models presentation templates and google slides. Security teams leverage advanced analytics and surveillance technologies to identify potential threats, ranging from cyber attacks to physical security breaches. the ppt templates facilitate the visualization of complex data, enabling teams to present findings and strategies clearly and concisely.
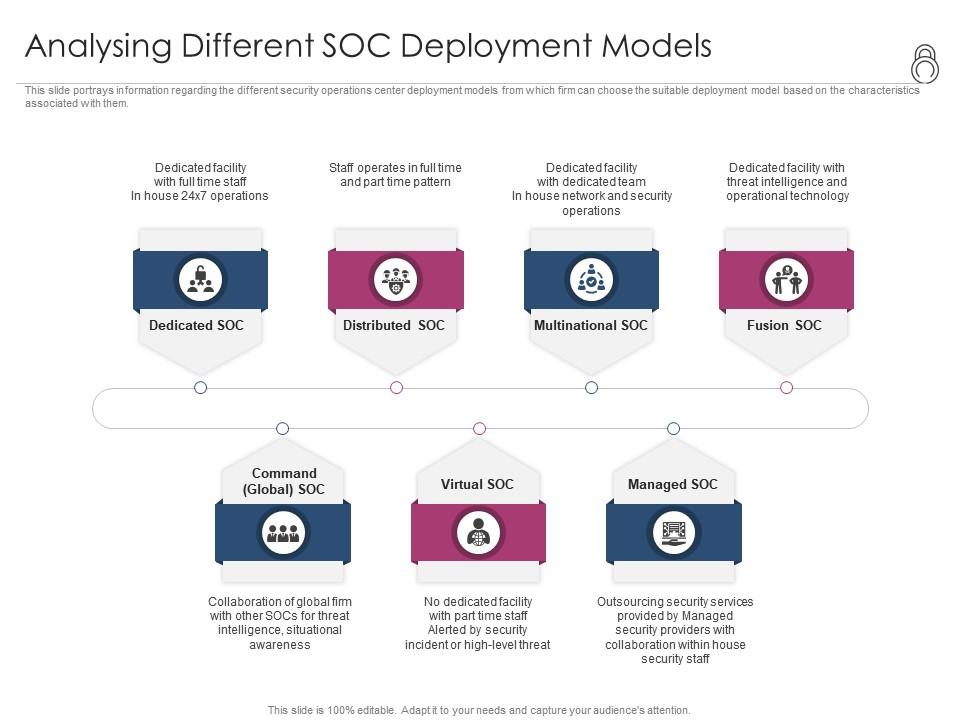
Enhanced Security Event Management Analysing Different Soc Deployment Enhance your cybersecurity strategy with our fully editable security operations center (soc) powerpoint presentations. tailor the content to fit your organization's needs and effectively communicate your security protocols. Boost your presentations with soc operating model powerpoint templates crafted for clarity and engagement. examples include: it security operations analyzing different soc. Impress your team and boss with beautiful analyzing different soc deployment models presentation templates and google slides. Security teams leverage advanced analytics and surveillance technologies to identify potential threats, ranging from cyber attacks to physical security breaches. the ppt templates facilitate the visualization of complex data, enabling teams to present findings and strategies clearly and concisely.

Analyzing Different Soc Deployment Models Clipart Pdf Impress your team and boss with beautiful analyzing different soc deployment models presentation templates and google slides. Security teams leverage advanced analytics and surveillance technologies to identify potential threats, ranging from cyber attacks to physical security breaches. the ppt templates facilitate the visualization of complex data, enabling teams to present findings and strategies clearly and concisely.
Comments are closed.