Analyzing Different Soc Deployment Models Security Operations

It Security Operations Analyzing Different Soc Deployment Models Ppt This insightful deck offers a detailed outline, guiding you through integration strategies, benefits, and challenges, empowering your organization to enhance security posture and operational efficiency. We’re going to cover each of the five security operations center models currently in use in full detail, and explain the use cases for each one. these guidelines should inform your decision to choose a vendor whose offering matches the needs of your organization.
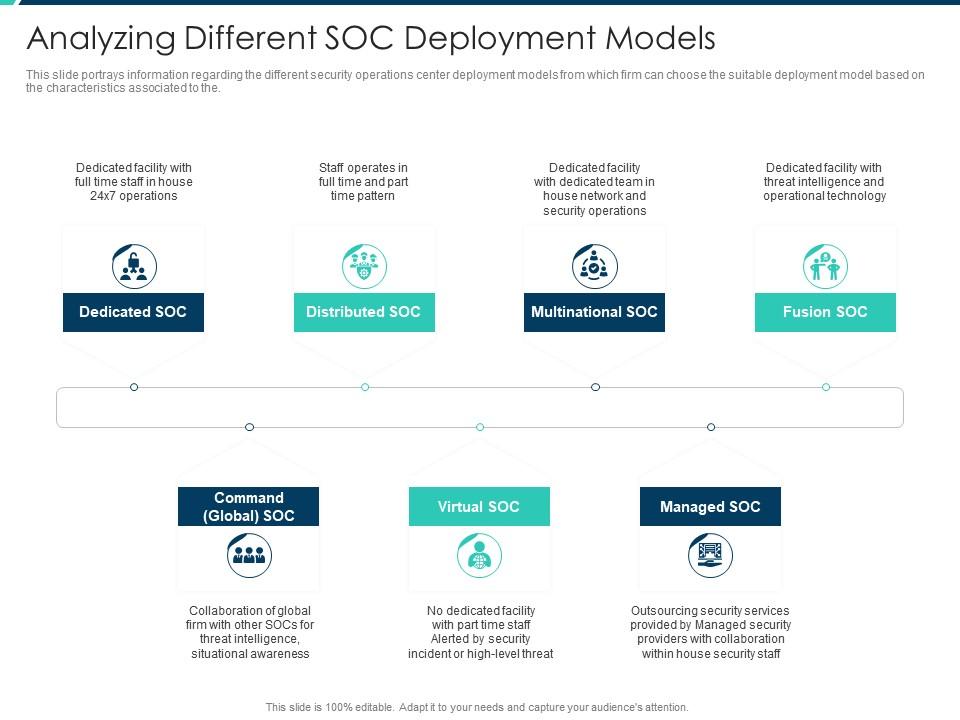
Analyzing Different Soc Deployment Models Security Operations Furthermore, this study offers actionable insights for organizations looking to enhance their soc capabilities, including a technical overview of soc use case coverage and a gap assessment of. Furthermore, this study offers actionable insights for organizations looking to enhance their soc capabilities, including a technical overview of soc use case coverage and a gap assessment of detection rules. Just like there are multiple types of security operations centers, there are also multiple ways in which a soc can be deployed. there are three main soc deployment models: internal, virtual (vsoc), and hybrid. Discover key insights into soc models in this comprehensive guide. explore staffing options, technology integrations, and operational strategies, and more.
Information And Technology Security Operations Analyzing Different Soc Just like there are multiple types of security operations centers, there are also multiple ways in which a soc can be deployed. there are three main soc deployment models: internal, virtual (vsoc), and hybrid. Discover key insights into soc models in this comprehensive guide. explore staffing options, technology integrations, and operational strategies, and more. This book, open source security operations center (soc): a complete guide to establishing, managing, and maintaining a modern soc, aims to provide a comprehensive resource for professionals seeking to build and optimize their security operations capabilities using open source tools and methodologies. Learn about the three types of security operations centers. compare models, staffing approaches, and costs to choose the right soc structure. There are several ways for an organization to acquire modern soc capabilities. discover what these models are and how to decide on a deployment model. Let’s explore the three major soc models as defined by gartner®, examine their strengths and drawbacks, and discover how to choose the right model for your organization.
Enterprise Security Operations Analyzing Different Soc Deployment This book, open source security operations center (soc): a complete guide to establishing, managing, and maintaining a modern soc, aims to provide a comprehensive resource for professionals seeking to build and optimize their security operations capabilities using open source tools and methodologies. Learn about the three types of security operations centers. compare models, staffing approaches, and costs to choose the right soc structure. There are several ways for an organization to acquire modern soc capabilities. discover what these models are and how to decide on a deployment model. Let’s explore the three major soc models as defined by gartner®, examine their strengths and drawbacks, and discover how to choose the right model for your organization.
Comments are closed.