Implementing Practical Electrical Glitching Attacks

Implementing Practical Electrical Glitching Attacks Youtube In this talk, we attempt to implement and execute successful voltage and clock glitching attacks on a group of target devices. during the talk, we detail the necessary conditions required to. Nullsec flipper suite comprehensive flipper zero payload collection for rf analysis, rfid nfc cloning, badusb attacks, infrared, and wireless pentesting. pineflip professional flipper zero companion app for linux with gtk4 libadwaita ui, screen mirroring, file manager, and firmware management.

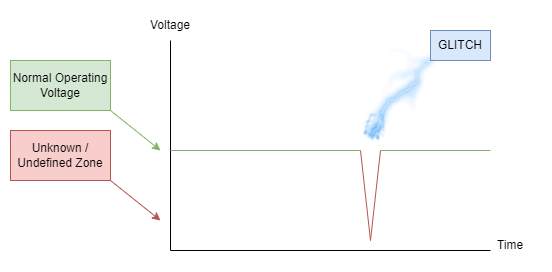
A Review On Evaluation And Configuration Of Fault Injection Attack We present systematic coverage of both clock glitching and voltage glitching methodologies, detailing their theoretical foundations, parameter configurations, and practical implementation considerations. In this talk, we attempt to implement and execute successful voltage and clock glitching attacks on a group of target devices. during the talk, we detail the necessary conditions required to create an affordable, and reliable exploit for a target device. Black hat briefings. Explore the world of electrical glitching attacks in this 43 minute black hat conference talk. delve into techniques for implementing and executing successful voltage and clock glitching attacks on various target devices.
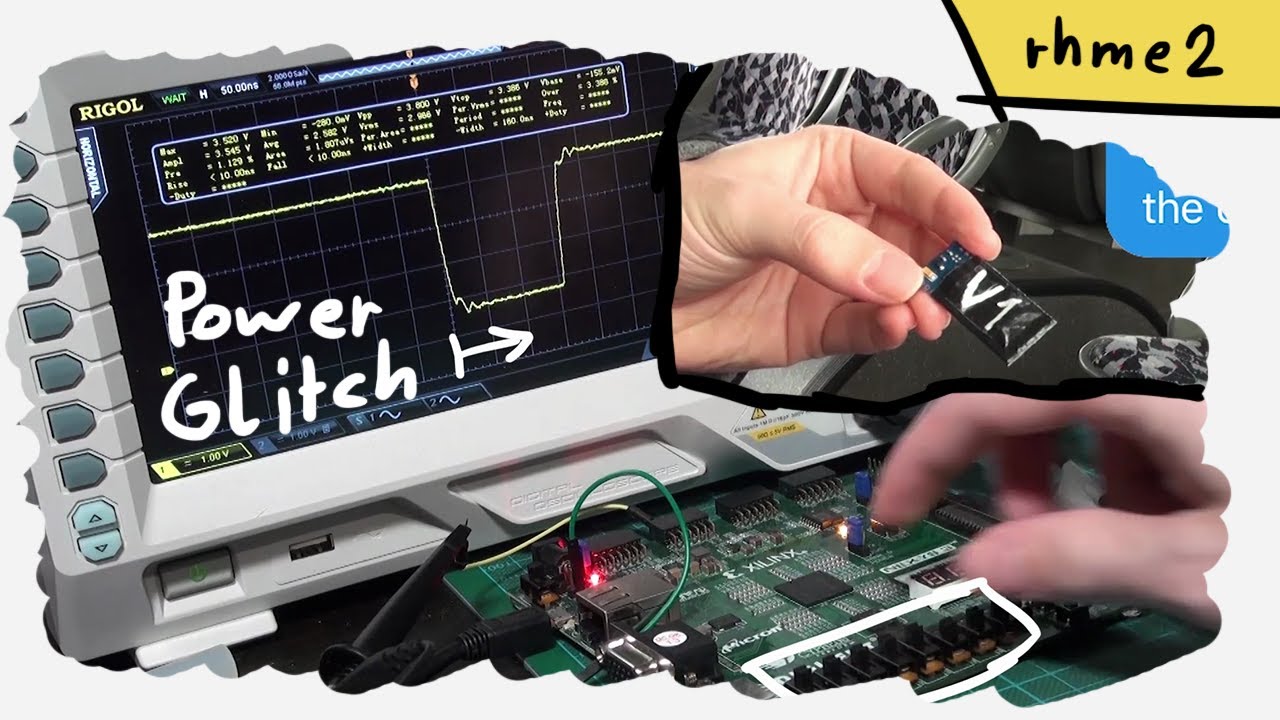
Hardware Power Glitch Attack Fault Injection Rhme2 Fiesta Fi 100 Black hat briefings. Explore the world of electrical glitching attacks in this 43 minute black hat conference talk. delve into techniques for implementing and executing successful voltage and clock glitching attacks on various target devices. We demonstrate four high speed clock glitching attacks, which successfully inject faults in systems, where detectors have been implemented to protect. the attacks remain unnoticed by the glitch detectors. Using a chipwhisperer cw305 target board, we specifically show, step by step, how to perform a voltage glitch in an aes block implemented on an fpga and show how to fail an aes execution by applying voltage glitches that cause it to produce erroneous results during the aes encryption process. This research presents an in depth analysis and practical exploitation of hardware fault injection attacks using vcc glitching on the esp32 platform to recover cryptographic keys from traces obtained during induced fault conditions. S numerous software only defenses against powerful and real world glitching attacks. our findings indicate that software only defenses can be implemented with acceptable run time and size overheads, while completely mitigating some single glitch attacks, minimizing the likelihood of a successful multi glitch attack (i.e., a success rate of 0:00030.
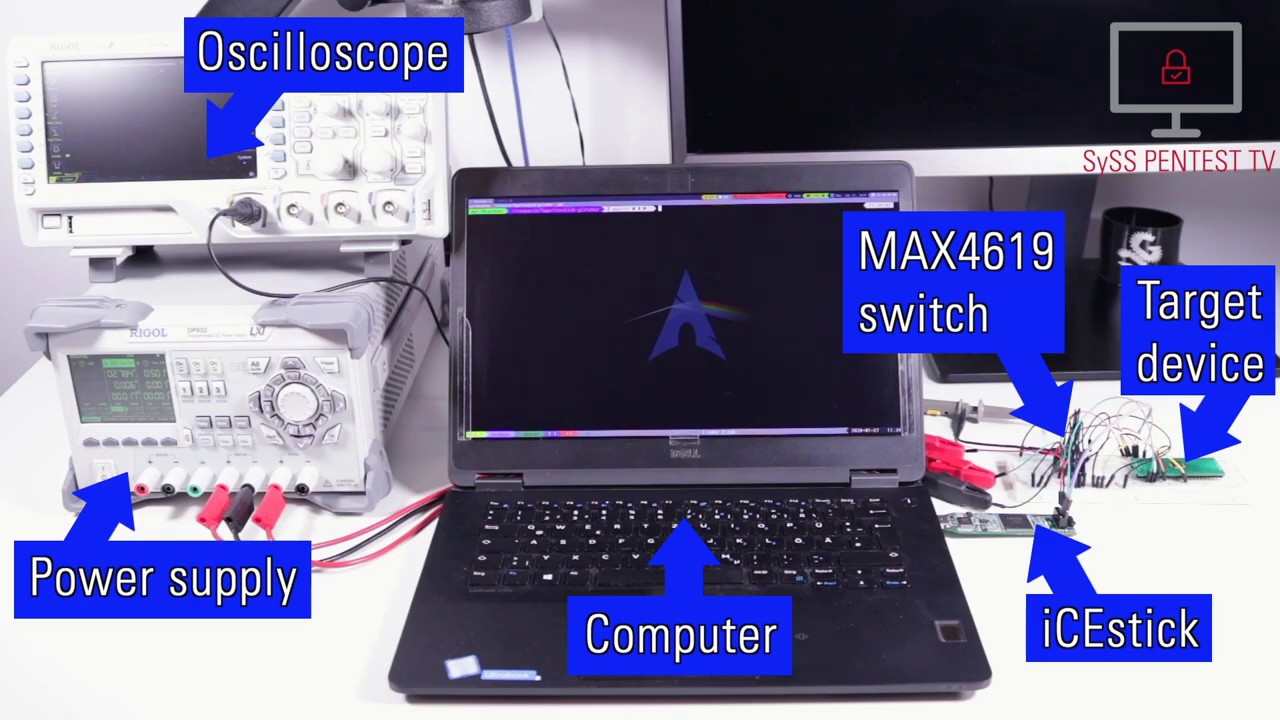
Voltage Glitching Attack Using Syss Icestick Glitcher Youtube We demonstrate four high speed clock glitching attacks, which successfully inject faults in systems, where detectors have been implemented to protect. the attacks remain unnoticed by the glitch detectors. Using a chipwhisperer cw305 target board, we specifically show, step by step, how to perform a voltage glitch in an aes block implemented on an fpga and show how to fail an aes execution by applying voltage glitches that cause it to produce erroneous results during the aes encryption process. This research presents an in depth analysis and practical exploitation of hardware fault injection attacks using vcc glitching on the esp32 platform to recover cryptographic keys from traces obtained during induced fault conditions. S numerous software only defenses against powerful and real world glitching attacks. our findings indicate that software only defenses can be implemented with acceptable run time and size overheads, while completely mitigating some single glitch attacks, minimizing the likelihood of a successful multi glitch attack (i.e., a success rate of 0:00030.
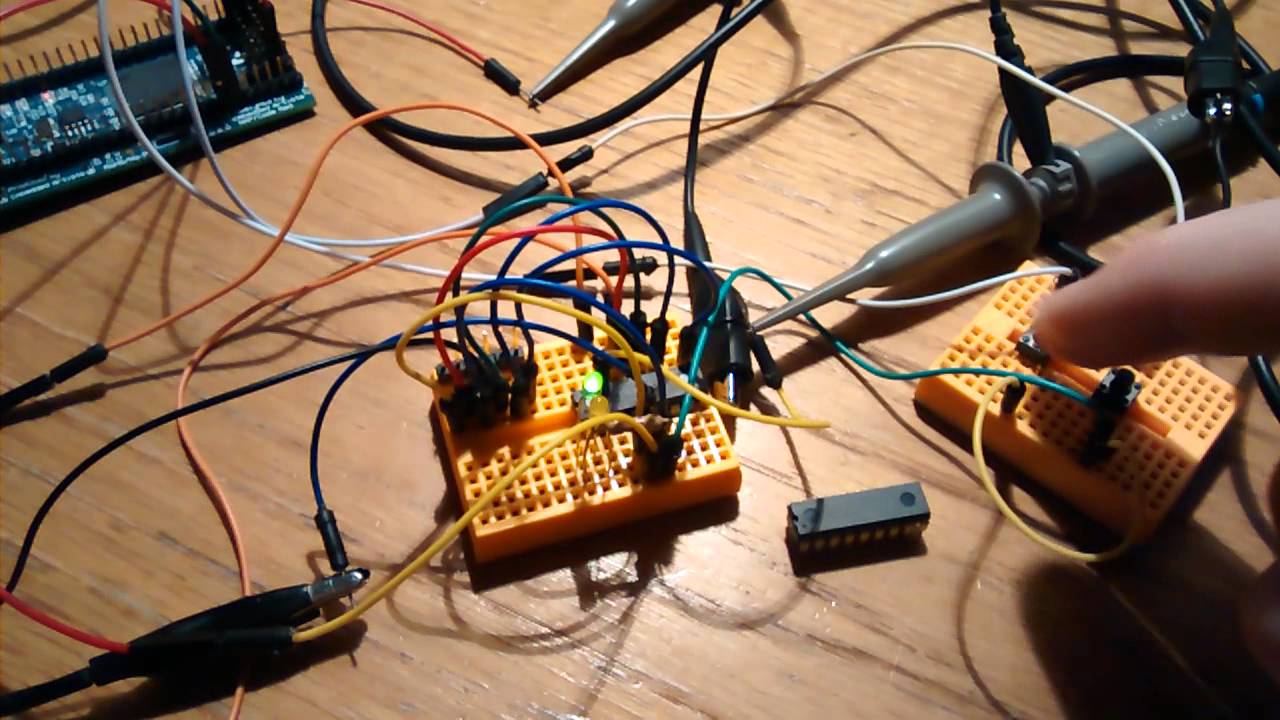
Experimenting With The Voltage During A Clock Glitch Attack Youtube This research presents an in depth analysis and practical exploitation of hardware fault injection attacks using vcc glitching on the esp32 platform to recover cryptographic keys from traces obtained during induced fault conditions. S numerous software only defenses against powerful and real world glitching attacks. our findings indicate that software only defenses can be implemented with acceptable run time and size overheads, while completely mitigating some single glitch attacks, minimizing the likelihood of a successful multi glitch attack (i.e., a success rate of 0:00030.
Replicant Reproducing A Fault Injection Attack On The Trezor One
Comments are closed.