Implementing Practical Electrical Glitching Attacks Youtube

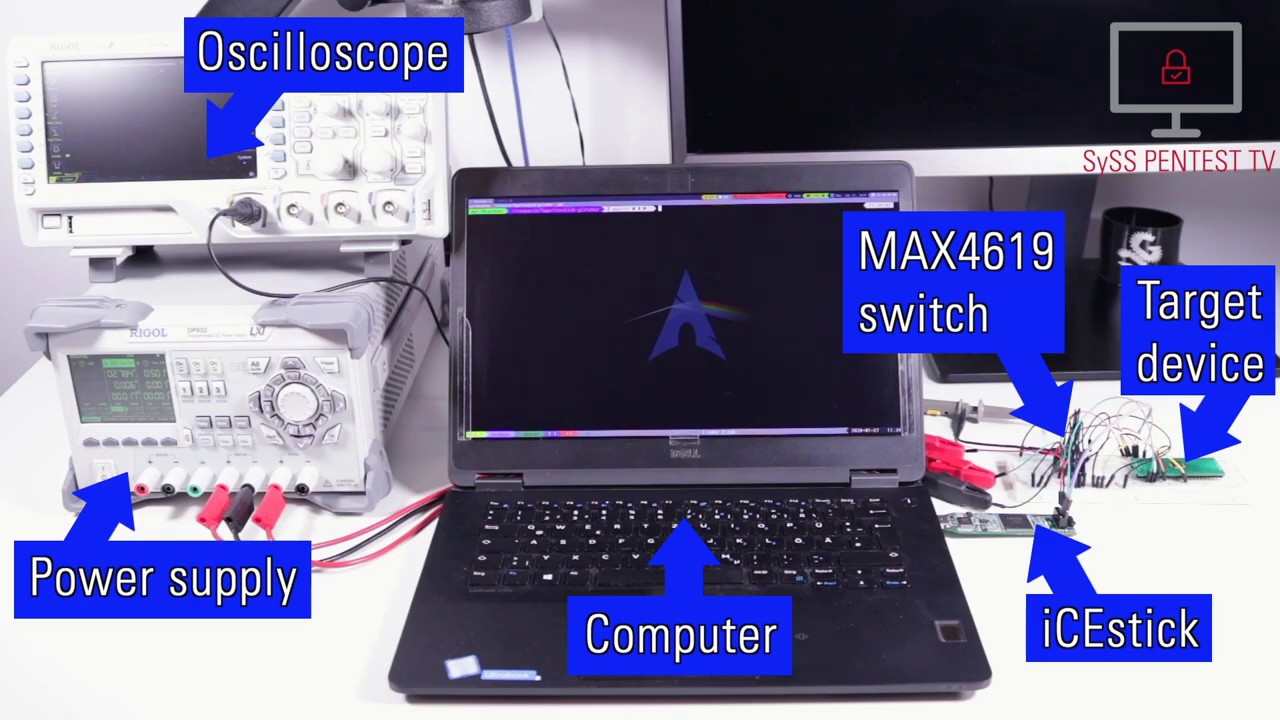
Black Hat Talk Implementing Practical Electrical Glitching Attacks In this talk, we attempt to implement and execute successful voltage and clock glitching attacks on a group of target devices. Explore the world of electrical glitching attacks in this 43 minute black hat conference talk. delve into techniques for implementing and executing successful voltage and clock glitching attacks on various target devices.

Electrical Hacks Youtube In this talk, we attempt to implement and execute successful voltage and clock glitching attacks on a group of target devices. during the talk, we detail the necessary conditions required to create an affordable, and reliable exploit for a target device. Together we will built a power glitching circuit that is able to break several different chip protections and despite the demanding content, no prerequisites are necessary. we learn everything. By triggering a successful glitch, it may be possible to bypass security features like read back protections, to activate disabled debug interfaces, or to bypass authentication or integrity. We're trying to get errors from running the chip beyond it's limits, for this we should start by running it at it's absolute limit. for example, you may want to run the target at as low a voltage.

Easy Electrical Hacks Youtube By triggering a successful glitch, it may be possible to bypass security features like read back protections, to activate disabled debug interfaces, or to bypass authentication or integrity. We're trying to get errors from running the chip beyond it's limits, for this we should start by running it at it's absolute limit. for example, you may want to run the target at as low a voltage. In episode 4, we investigate how to conduct a power glitch attack, exploits that some hardware wallets though not ledger's are still vulnerable to. watch, learn, and enter the donjon. I will talk about basic tools needed to begin, what to look for, and how you too can play with just about any iot type device. this talk came from the idea of wanting to reset a point to point. In this talk, we attempt to implement and execute successful voltage and clock glitching attacks on a group of target devices. during the talk, we detail the necessary conditions required to create an affordable, and reliable exploit for a target device. Submit a pr with new resources following the existing structure. this collection is provided for educational and research purposes.

Electrician Hack Youtube In episode 4, we investigate how to conduct a power glitch attack, exploits that some hardware wallets though not ledger's are still vulnerable to. watch, learn, and enter the donjon. I will talk about basic tools needed to begin, what to look for, and how you too can play with just about any iot type device. this talk came from the idea of wanting to reset a point to point. In this talk, we attempt to implement and execute successful voltage and clock glitching attacks on a group of target devices. during the talk, we detail the necessary conditions required to create an affordable, and reliable exploit for a target device. Submit a pr with new resources following the existing structure. this collection is provided for educational and research purposes.

Clever Electrical Hacks Technical Tricks Youtube In this talk, we attempt to implement and execute successful voltage and clock glitching attacks on a group of target devices. during the talk, we detail the necessary conditions required to create an affordable, and reliable exploit for a target device. Submit a pr with new resources following the existing structure. this collection is provided for educational and research purposes.
Voltage Glitching Attack Using Syss Icestick Glitcher Youtube
Comments are closed.