Implementing Post Quantum Cryptography With Nick Sullivan

Post Quantum Cryptography Kwantumg Research Labs Pvt Ltd In this interview with nick sullivan, cryptography consultant and former head of research at cloudflare, we explore practical implications of migrating post quantum cryptography (pqc). Nick sullivan, and adam langley join melanie and mark to provide a pragmatic view on post quantum cryptography and what it means to research security for the potential of quantum computing.

Post Quantum Cryptography With Nick Sullivan And Adam Langley R Adam langley and nick sullivan help us understand post quantum cryptography and what security research looks like for quantum computing. In this interview with nick sullivan, world renowned cryptographer, infosec global 's advisor, and former head of research at cloudflare, we explore the practical steps to migrate to. Listen to post quantum cryptography with nick sullivan and adam langley and 333 more episodes by google cloud platform podcast, free! no signup or install needed. Nick sullivan, and adam langley join melanie and mark to provide a pragmatic view on post quantum cryptography and what it means to research security for the potential of quantum computing.
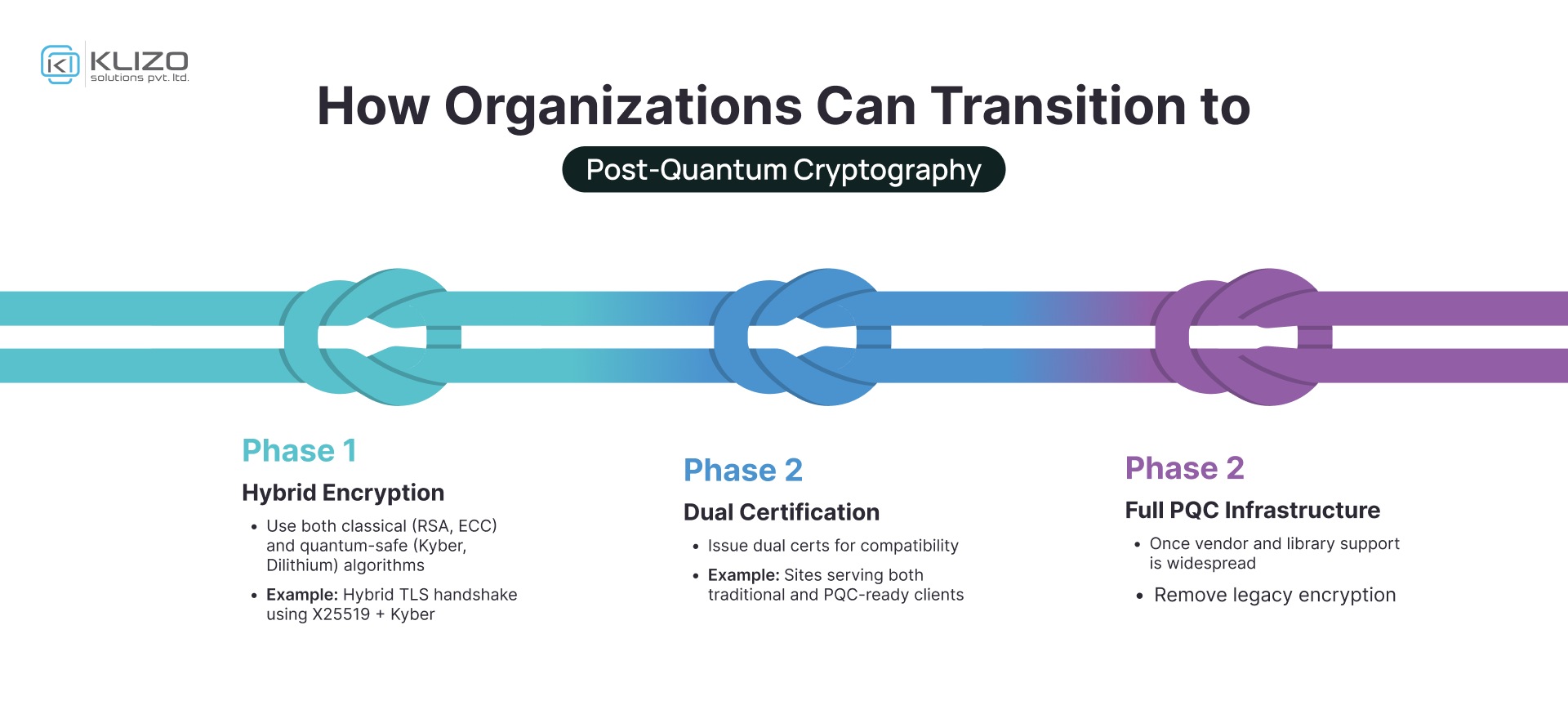
Post Quantum Cryptography The Future Of Secure Computing Klizos Listen to post quantum cryptography with nick sullivan and adam langley and 333 more episodes by google cloud platform podcast, free! no signup or install needed. Nick sullivan, and adam langley join melanie and mark to provide a pragmatic view on post quantum cryptography and what it means to research security for the potential of quantum computing. As quantum computing continues to mature, research and development efforts in cryptography are keeping pace. we’re working with academia and industry peers to help create a new set of cryptography standards that are resilient to attack from quantum computers. This technical guide provides it and security professionals with practical instructions for implementing nist approved post quantum cryptographic algorithms in enterprise environments. The table below summarizes the proposed criteria. proposed post quantum prioritization. b. build a cryptographic inventory cryptography algorithms’ strength decays with time, as depicted in the chart below. since the inception of cryptography, we have seen multiple ciphers and algorithms rise and fall with regards to security and adoption rate. Google cloud platform podcast post quantum cryptography with nick sullivan and adam langley.
Comments are closed.