Implementing Post Quantum Cryptography Guide Integration For Existing

High Speed Design Of Post Quantum Cryptography With Optimized Hashing Implementing post quantum cryptography guide integration for existing systems discover a clear, step by step approach to integrating post quantum cryptography into your existing systems. this guide provides practical insights to ensure a seamless and secure transition. This technical guide provides it and security professionals with practical instructions for implementing nist approved post quantum cryptographic algorithms in enterprise environments.

Guide Integration Pdf Key Cryptography Encryption Comprehensive guide for implementing nist finalized post quantum cryptography in enterprise environments. migration strategies, hsm integration, and cnsa 2.0 compliance. Identifying relevant locations first step in implementing pqc in an existing application. Organizations should begin applying these standards now to migrate their systems to quantum resistant cryptography. Industry leaders are already using pqc in production, proving that it can be integrated into existing infrastructures. this guide is designed to help you chart your path across the divide.

Implementing Post Quantum Cryptography Guide Integration For Existing Organizations should begin applying these standards now to migrate their systems to quantum resistant cryptography. Industry leaders are already using pqc in production, proving that it can be integrated into existing infrastructures. this guide is designed to help you chart your path across the divide. This paper presents a structured literature review of ongoing global efforts to integrate post quantum cryptography (pqc) into widely deployed communication and identity protocols. In our paper, we have demonstrated how to integrate some of the candidate algorithms from the nist post quantum cryptography standardization contest to a widely used programming library. At secure quantum, we understand the complexities of integrating new cryptographic solutions into existing it infrastructures. our pqc implementation service ensures seamless integration by carefully mapping post quantum algorithms to your current systems, without compromising performance. By integrating the recently finalized nist pqc standards deep into the platform, we’re establishing a new, quantum resistant chain of trust. this chain of trust secures the platform continuously—from the moment the os powers on, to the execution of applications distributed globally.
Post Quantum Cryptography Integration Study Enisa This paper presents a structured literature review of ongoing global efforts to integrate post quantum cryptography (pqc) into widely deployed communication and identity protocols. In our paper, we have demonstrated how to integrate some of the candidate algorithms from the nist post quantum cryptography standardization contest to a widely used programming library. At secure quantum, we understand the complexities of integrating new cryptographic solutions into existing it infrastructures. our pqc implementation service ensures seamless integration by carefully mapping post quantum algorithms to your current systems, without compromising performance. By integrating the recently finalized nist pqc standards deep into the platform, we’re establishing a new, quantum resistant chain of trust. this chain of trust secures the platform continuously—from the moment the os powers on, to the execution of applications distributed globally.
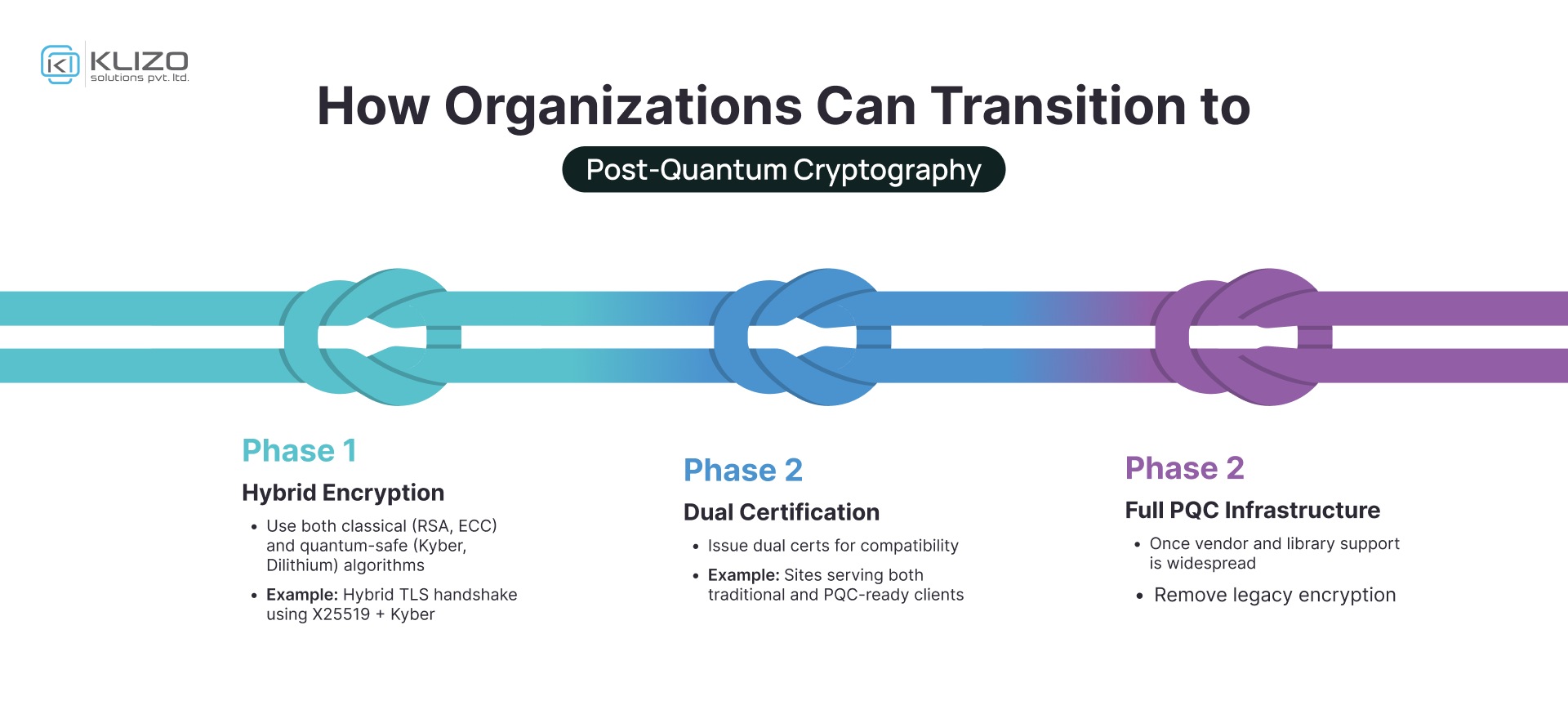
Post Quantum Cryptography The Future Of Secure Computing Klizos At secure quantum, we understand the complexities of integrating new cryptographic solutions into existing it infrastructures. our pqc implementation service ensures seamless integration by carefully mapping post quantum algorithms to your current systems, without compromising performance. By integrating the recently finalized nist pqc standards deep into the platform, we’re establishing a new, quantum resistant chain of trust. this chain of trust secures the platform continuously—from the moment the os powers on, to the execution of applications distributed globally.
Comments are closed.