Testing Post Quantum Cryptography With Cyperf

High Speed Design Of Post Quantum Cryptography With Optimized Hashing In this video, we demonstrate how cyperf introduces post quantum cryptography (pqc) groups within its tls stack, enabling customers to confidently test pqc enabled devices. Post quantum cryptography (pqc) is moving from theory to practice — and it needs to be tested. as post quantum algorithms such as ml kem and ml dsa start to appear in real deployments.
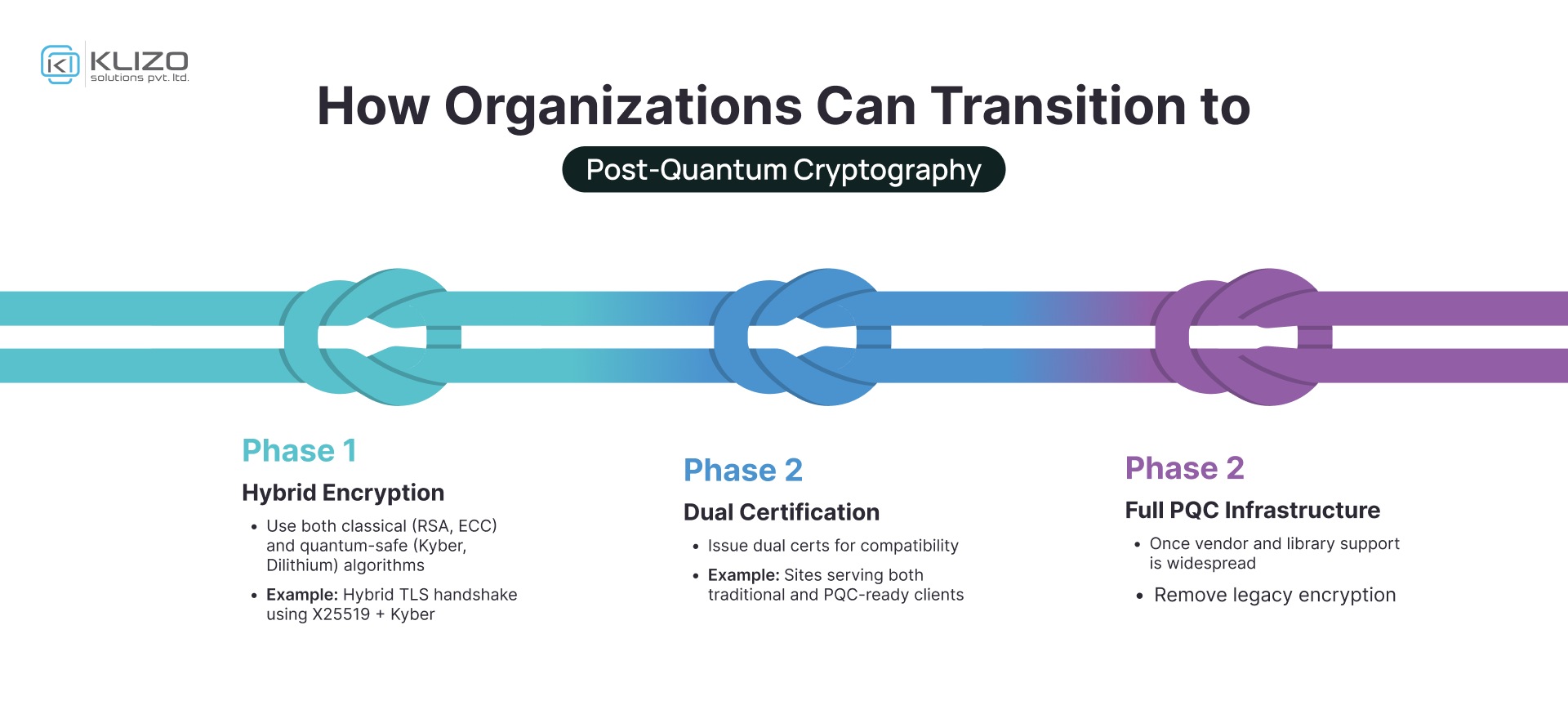
Post Quantum Cryptography The Future Of Secure Computing Klizos Test performance and security both pre deployment in a lab or safely in live production networks. portable subscription based software solution with a robust and intuitive cloud native gui management dashboard. This paper first analyzes the threat of quantum computing to existing cryptographic systems, then introduces in detail the main technical routes of pqc and its standardization process. Learn how to use keysight's cyperf distributed, elastic performance and security test system. Post quantum cryptography (pqc) is a critical area of research aimed at addressing the threat quantum computing poses to traditional cryptographic systems. it focuses on evaluating the.
Post Quantum Cryptography Ml Kem Implementation Guide Learn how to use keysight's cyperf distributed, elastic performance and security test system. Post quantum cryptography (pqc) is a critical area of research aimed at addressing the threat quantum computing poses to traditional cryptographic systems. it focuses on evaluating the. Post quantum cryptography (pqc) is here, and it’s time to prepare. current encryption methods will become obsolete, potentially setting back our privacy and security by years. I will provide a high level overview of our efforts in generating test vectors to assess side channel leakage in ntt transformations, with a particular focus on butterfly ntt transformations within the ml dsa pqc algorithm. This paper investigates the feasibility of deploying post quantum cryptography (pqc) algorithms on resource constrained devices. in particular, we implement three pqc algorithms — bike, crystals kyber, and hqc — on a lightweight iot platform built with raspberry pi devices. In the coming years the internet will move to post quantum cryptography. today we are offering our customers the tools to get a headstart and test post quantum key agreements.
Quantum Resilient Encryption Post Quantum Cyrptography Solutions By Tyto Post quantum cryptography (pqc) is here, and it’s time to prepare. current encryption methods will become obsolete, potentially setting back our privacy and security by years. I will provide a high level overview of our efforts in generating test vectors to assess side channel leakage in ntt transformations, with a particular focus on butterfly ntt transformations within the ml dsa pqc algorithm. This paper investigates the feasibility of deploying post quantum cryptography (pqc) algorithms on resource constrained devices. in particular, we implement three pqc algorithms — bike, crystals kyber, and hqc — on a lightweight iot platform built with raspberry pi devices. In the coming years the internet will move to post quantum cryptography. today we are offering our customers the tools to get a headstart and test post quantum key agreements.
/vnd/media/post_attachments/wp-content/uploads/2022/09/Post-Quantum-Cryptography-fig11.jpg)
Post Quantum Cryptography Pqc This paper investigates the feasibility of deploying post quantum cryptography (pqc) algorithms on resource constrained devices. in particular, we implement three pqc algorithms — bike, crystals kyber, and hqc — on a lightweight iot platform built with raspberry pi devices. In the coming years the internet will move to post quantum cryptography. today we are offering our customers the tools to get a headstart and test post quantum key agreements.

The Urgency Of Post Quantum Cryptography Adoption Ieee Spectrum
Comments are closed.