How To Identify Intel Computers Vulnerable To Downfall
How To Identify Computers Vulnerable To Downfall Pdq Intel’s new downfall vulnerability has been disclosed, and your devices are likely impacted. discover how to identify devices vulnerable to cve 2022 40982. There is a serious security flaw in billions of intel cpus that can let attackers steal confidential data like passwords and encryption keys.
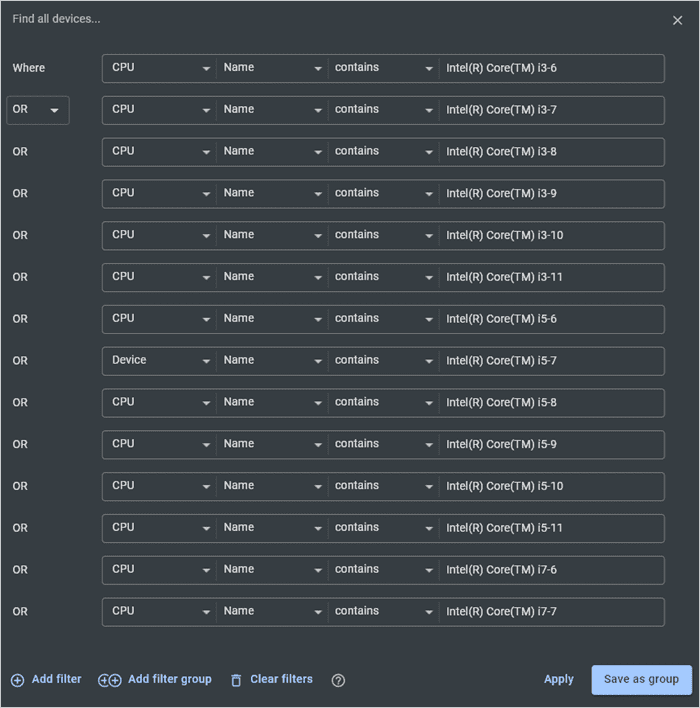
How To Identify Computers Vulnerable To Downfall Pdq Downfall, known as gather data sampling (gds) by intel, [1] is a computer security vulnerability found in 6th through 11th generations of consumer and 1st through 4th generations of intel xeon scalable x86 64 microprocessors. [2]. Intel, and nearly the entire technology industry, follows a disclosure practice called coordinated disclosure, under which a cybersecurity vulnerability is generally publicly disclosed only after mitigations are available. Understand the critical aspects of cve 2022 40982 with a detailed vulnerability assessment, exploitation potential, affected technologies, and remediation guidance. With potentially billions of processors at risk, chances are you have vulnerable devices. find out how to identify impacted devices quickly with pdq inventory and pdq connect.

How To Identify Computers Vulnerable To Downfall Pdq Understand the critical aspects of cve 2022 40982 with a detailed vulnerability assessment, exploitation potential, affected technologies, and remediation guidance. With potentially billions of processors at risk, chances are you have vulnerable devices. find out how to identify impacted devices quickly with pdq inventory and pdq connect. Yesterday, different security researchers published details on two different vulnerabilities, one affecting multiple generations of intel processors and another affecting the newest amd cpus. The vulnerability is caused by memory optimization features in intel processors that unintentionally reveal internal hardware registers to software. this allows untrusted software to access data stored by other programs, which should not normally be accessible. Downfall is a new cpu vulnerability that intel has disclosed, which uses gather data sampling in order to extract data and other sensitive information on a number of cpus. Many customers, after reviewing intel's risk assessment guidance, may determine to disable the mitigation via switches made available through windows and linux operating systems as well as vmms.
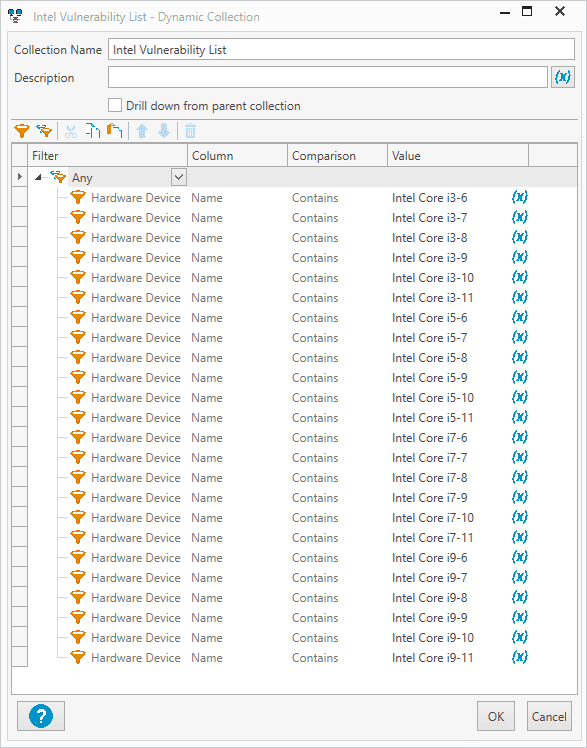
How To Identify Computers Vulnerable To Downfall Pdq Yesterday, different security researchers published details on two different vulnerabilities, one affecting multiple generations of intel processors and another affecting the newest amd cpus. The vulnerability is caused by memory optimization features in intel processors that unintentionally reveal internal hardware registers to software. this allows untrusted software to access data stored by other programs, which should not normally be accessible. Downfall is a new cpu vulnerability that intel has disclosed, which uses gather data sampling in order to extract data and other sensitive information on a number of cpus. Many customers, after reviewing intel's risk assessment guidance, may determine to disable the mitigation via switches made available through windows and linux operating systems as well as vmms.

How To Identify Computers Vulnerable To Downfall Pdq Downfall is a new cpu vulnerability that intel has disclosed, which uses gather data sampling in order to extract data and other sensitive information on a number of cpus. Many customers, after reviewing intel's risk assessment guidance, may determine to disable the mitigation via switches made available through windows and linux operating systems as well as vmms.
Intel Downfall Bug Steals Encryption Keys Data From Years Of Cpus
Comments are closed.