Downfall Vulnerability Exposes Intel Cpus To Data And Encryption Keys

New Downfall Vulnerability Can Steal Passwords And Encryption Keys Downfall, known as gather data sampling (gds) by intel, [1] is a computer security vulnerability found in 6th through 11th generations of consumer and 1st through 4th generations of intel xeon scalable x86 64 microprocessors. [2]. Downfall vulnerability impacts various intel microprocessors and enables encryption keys, passwords, and other sensitive data exfiltration. the flaw was dubbed cve 2022 40982 and was reported to intel by security researcher daniel moghimi.
Intel Downfall Bug Steals Encryption Keys Data From Years Of Cpus A senior research scientist at google has devised new cpu attacks to exploit a vulnerability dubbed downfall that affects multiple intel microprocessor families and allows stealing. Also known as cve 2022 40982, the downfall bug exploits a flaw in the “gather” instruction that affected intel cpus use to grab information from multiple places in a system’s memory. On the page, moghami shows demos stealing 128 bit and 256 bit aes keys from other users, as well as spying on typed characters and taking data from the linux kernel. Downfall attacks target a critical weakness found in billions of modern processors used in personal and cloud computers. this vulnerability, identified as cve 2022 40982, enables a user to access and steal data from other users who share the same computer.
Lawsuit Claims Intel Sold Billions Of Avx Enabled Cpus Knowing Of On the page, moghami shows demos stealing 128 bit and 256 bit aes keys from other users, as well as spying on typed characters and taking data from the linux kernel. Downfall attacks target a critical weakness found in billions of modern processors used in personal and cloud computers. this vulnerability, identified as cve 2022 40982, enables a user to access and steal data from other users who share the same computer. Downfall vulnerability scope: the downfall vulnerability, tracked as cve 2022 40982, affects multiple intel microprocessor families from skylake through ice lake, enabling attackers to steal sensitive data, including passwords, encryption keys, and private user data. There is a serious security flaw in billions of intel cpus that can let attackers steal confidential data like passwords and encryption keys. Since at least 2014, several generations of intel cpus have been vulnerable to exactly this type of data leak, exposing billions of chips to an attack that can easily be used to steal sensitive data, including encryption keys. A potential security vulnerability in some intel® processors may allow information disclosure. intel is releasing firmware updates and an optional software sequence to mitigate this potential vulnerability.

Intel Knew About The Downfall Cpu Vulnerability But Did Nothing For Downfall vulnerability scope: the downfall vulnerability, tracked as cve 2022 40982, affects multiple intel microprocessor families from skylake through ice lake, enabling attackers to steal sensitive data, including passwords, encryption keys, and private user data. There is a serious security flaw in billions of intel cpus that can let attackers steal confidential data like passwords and encryption keys. Since at least 2014, several generations of intel cpus have been vulnerable to exactly this type of data leak, exposing billions of chips to an attack that can easily be used to steal sensitive data, including encryption keys. A potential security vulnerability in some intel® processors may allow information disclosure. intel is releasing firmware updates and an optional software sequence to mitigate this potential vulnerability.
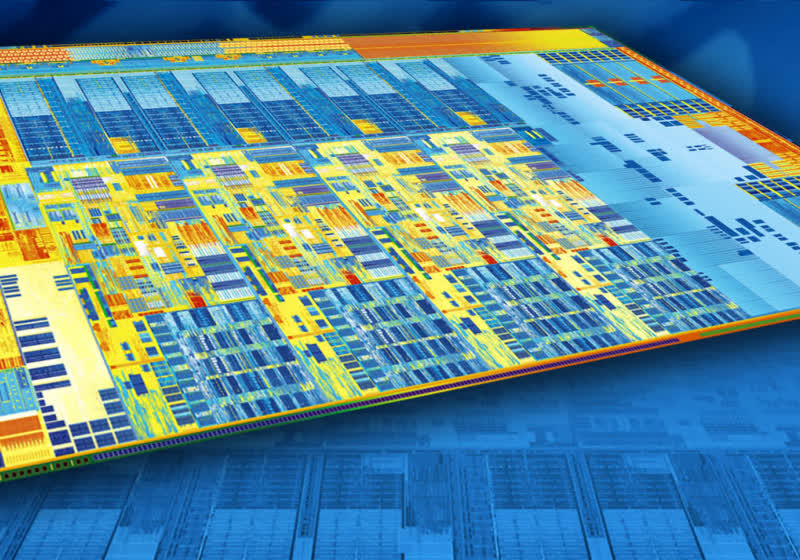
Intel Knew About The Downfall Cpu Vulnerability But Did Nothing For Since at least 2014, several generations of intel cpus have been vulnerable to exactly this type of data leak, exposing billions of chips to an attack that can easily be used to steal sensitive data, including encryption keys. A potential security vulnerability in some intel® processors may allow information disclosure. intel is releasing firmware updates and an optional software sequence to mitigate this potential vulnerability.

Downfall Bug Affects Years Of Intel Cpus Can Leak Encryption Keys
Comments are closed.