How Does Rsa Cryptography Work
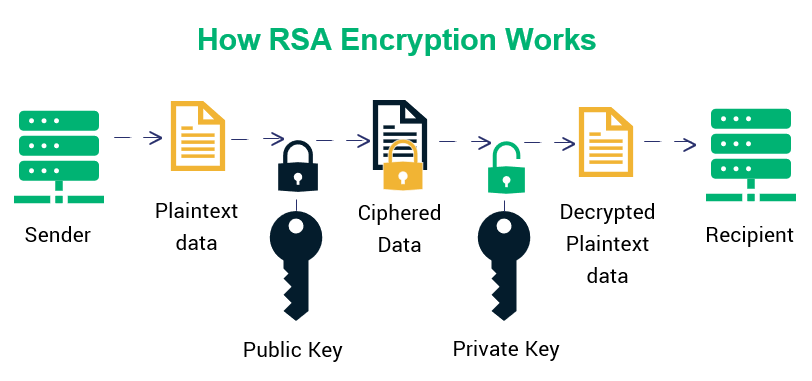
Understanding Rsa Asymmetric Encryption How It Works Public key cryptography: rsa algorithm is a public key cryptography algorithm, which means that it uses two different keys for encryption and decryption. the public key is used to encrypt the data, while the private key is used to decrypt the data. In rsa based cryptography, a user's private key —which can be used to sign messages, or decrypt messages sent to that user—is a pair of large prime numbers chosen at random and kept secret.

Enduring Power Of Rsa Encryption In Securing Network Communications Rsa (rivest–shamir–adleman) is one of the most widely used public key cryptosystems. it’s based on asymmetric encryption, where two keys are used: a public key (shared with everyone) and a. Rsa encryption may sound complex at first glance, but its underlying mechanisms are actually quite straightforward once broken down. this extensive guide aims to make rsa fully accessible to readers of all technical levels – no advanced math or cryptography expertise required!. In public key cryptography, rsa stands out for its strength and reliability. the public key used in the encryption process is shared publicly without compromising the security of the private one due to the complex mathematical relationship between the two. Discover how rsa works, the key algorithm for encrypting data and digital signatures. learn how to use and apply it.
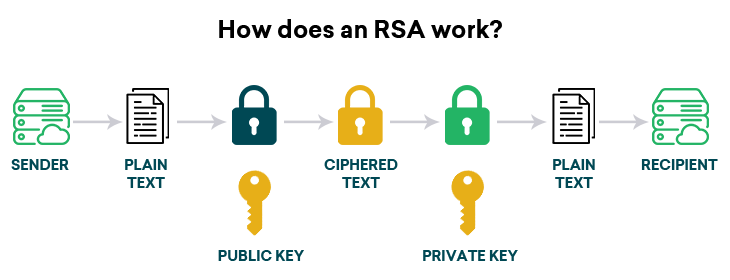
What Is Rsa How Does An Rsa Encryption Work In public key cryptography, rsa stands out for its strength and reliability. the public key used in the encryption process is shared publicly without compromising the security of the private one due to the complex mathematical relationship between the two. Discover how rsa works, the key algorithm for encrypting data and digital signatures. learn how to use and apply it. Rsa encryption is a form of asymmetric cryptography that uses a public key to encrypt data and a private key to decrypt it. unlike symmetric encryption, rsa does not use the same key for both processes. it secures data by relying on the difficulty of factoring large prime numbers. Rsa is a public key cryptosystem for data encryption. explore its security features and common use cases, and learn how to mitigate rsa vulnerabilities. Rsa (rivest shamir adleman) is a famous encryption scheme that makes use of a combination of public and private keys. this means you have a non public key and one that can be shared publicly. each key can be used to encrypt data, but only the opposite can be decrypted. Rsa is a public key encryption algorithm that uses an asymmetric encryption algorithm to encrypt data. rsa is the primary method of encrypting data in motion.
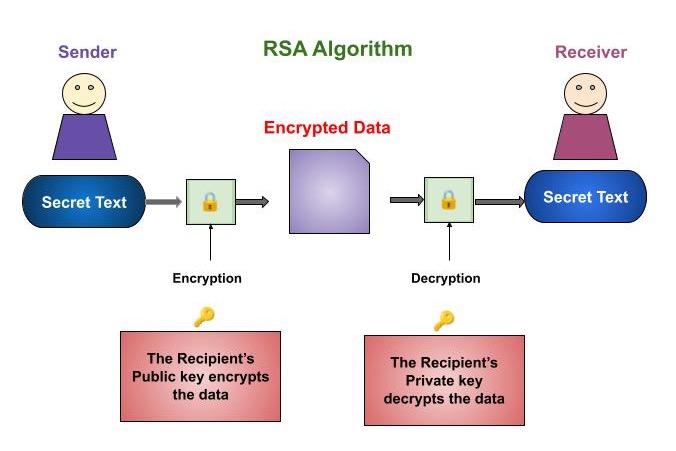
Cryptography Rsa Algorithm Rsa encryption is a form of asymmetric cryptography that uses a public key to encrypt data and a private key to decrypt it. unlike symmetric encryption, rsa does not use the same key for both processes. it secures data by relying on the difficulty of factoring large prime numbers. Rsa is a public key cryptosystem for data encryption. explore its security features and common use cases, and learn how to mitigate rsa vulnerabilities. Rsa (rivest shamir adleman) is a famous encryption scheme that makes use of a combination of public and private keys. this means you have a non public key and one that can be shared publicly. each key can be used to encrypt data, but only the opposite can be decrypted. Rsa is a public key encryption algorithm that uses an asymmetric encryption algorithm to encrypt data. rsa is the primary method of encrypting data in motion.
Comments are closed.