How Does Rsa Cryptography Work Youtube
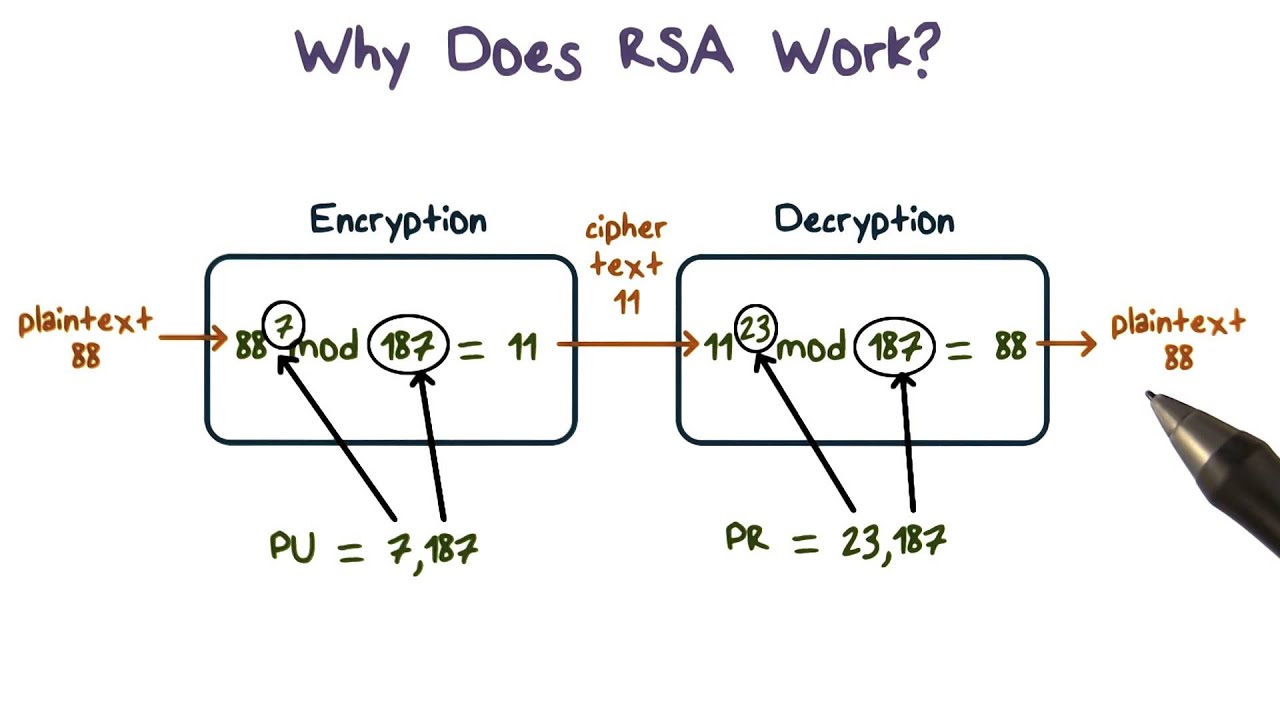
Why Does Rsa Work Youtube By the end of this video, you’ll have a solid understanding of how rsa works, from key generation to encryption and decryption, with a practical example of how alice can send a secure message. Without encryption, every conversation you had online would be visible to anyone. we couldn't have online banking or shopping if we couldn't encrypt our financial information to transmit it safely. rsa stands for rivest shamir adleman, the three people who developed it.

Cryptography Rsa Youtube Rsa creates a pair of commutative keys allowing encryption with one key and decryption with the other, unlike other asymmetric encryption algorithms like diffie hellman or digital signature algorithm. Here, he explains how the rsa algorithm works in general, and goes through 2 worked examples with small prime numbers. Using intuitive explanations and helpful visuals, i'll simplify the complexities, allowing you to fully comprehend how this robust encryption method operates. 💻 getting hands on: theory meets. But how does it actually work under the hood? in this video, we strip away the confusing analogies and dive into the pure mathematics of public key cryptography without the hand waving.

Rsa Cryptography 2 Youtube Using intuitive explanations and helpful visuals, i'll simplify the complexities, allowing you to fully comprehend how this robust encryption method operates. 💻 getting hands on: theory meets. But how does it actually work under the hood? in this video, we strip away the confusing analogies and dive into the pure mathematics of public key cryptography without the hand waving. We walk our way through a math example of generating rsa keys, and then proving the ability to encrypt a message with one key and decrypt with the other (in both directions). In this video, john and deb provide an overview of rsa encryption, explaining its fundamental principles and applications. they discuss the significance of public and private keys, the process. Welcome to our tutorial video on rsa encryption! in this comprehensive guide, we will demystify the concept of rsa encryption, a widely used asymmetric cryptographic algorithm. The rsa algorithm is the only asymmetric algorithm that can do asymmetric encryption. it's often used as the definition of asymmetric crypto, but technically asymmetric crypto includes so much.
Rsa Cryptography Youtube We walk our way through a math example of generating rsa keys, and then proving the ability to encrypt a message with one key and decrypt with the other (in both directions). In this video, john and deb provide an overview of rsa encryption, explaining its fundamental principles and applications. they discuss the significance of public and private keys, the process. Welcome to our tutorial video on rsa encryption! in this comprehensive guide, we will demystify the concept of rsa encryption, a widely used asymmetric cryptographic algorithm. The rsa algorithm is the only asymmetric algorithm that can do asymmetric encryption. it's often used as the definition of asymmetric crypto, but technically asymmetric crypto includes so much.
Comments are closed.