Gpg Key Usage Serverspace Tutorials
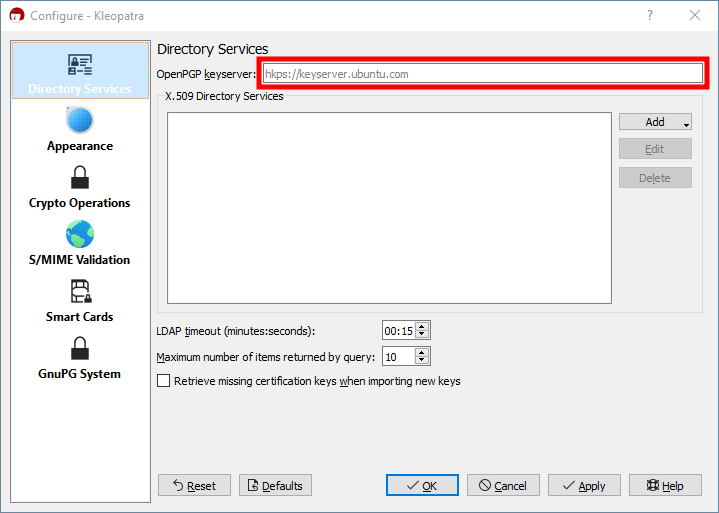
Gpg4win Tutorials Changekeyserver Gnupg Wiki In gpg (gnu privacy guard), each key can have several components that define its function. these components are represented in brackets in the output of the command gpg list keys or gpg list secret keys. Learn how to securely manage your gpg keyring on linux and windows. this step by step guide covers generating, importing, exporting, and deleting gpg keys to protect your files and communications.
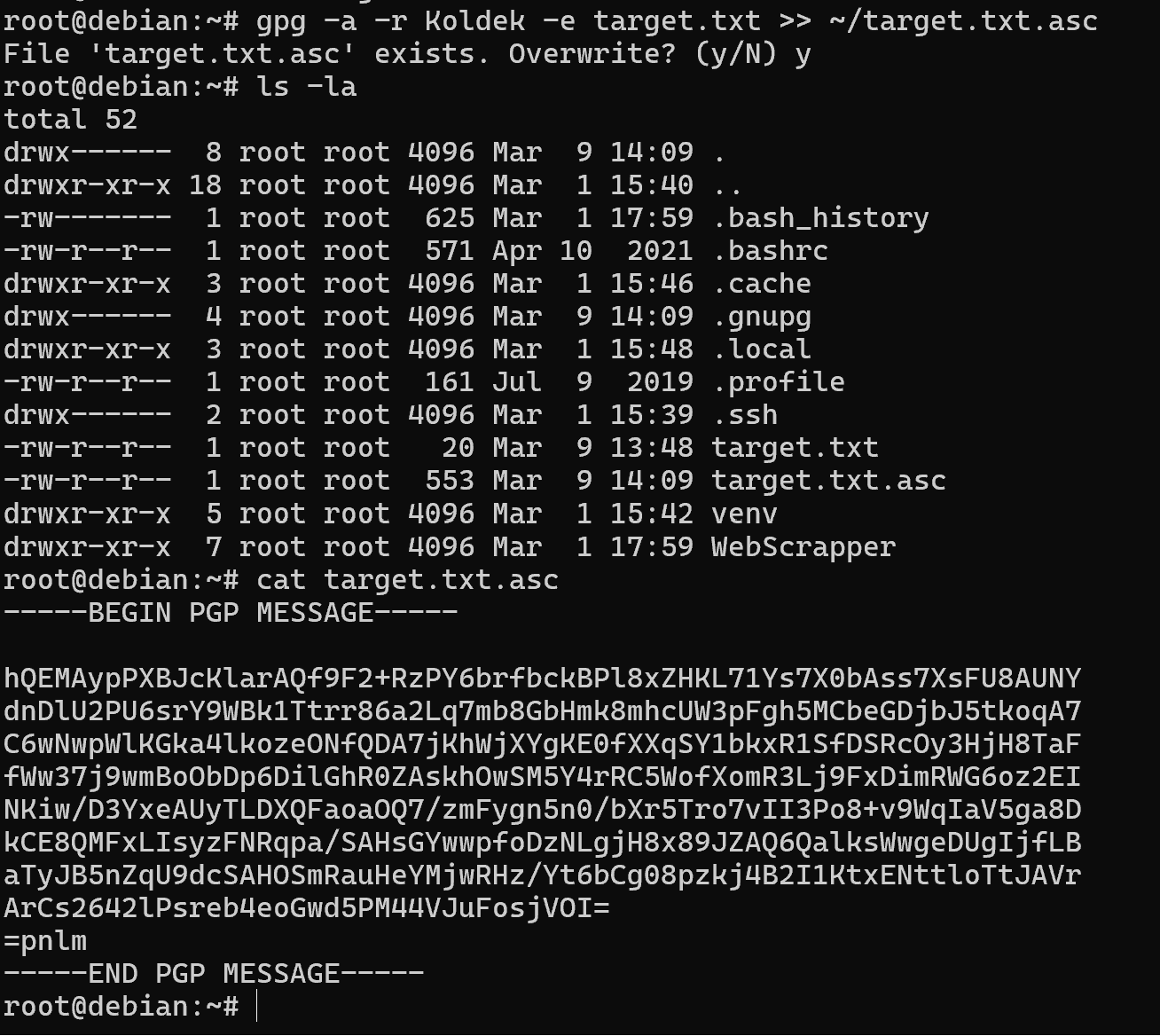
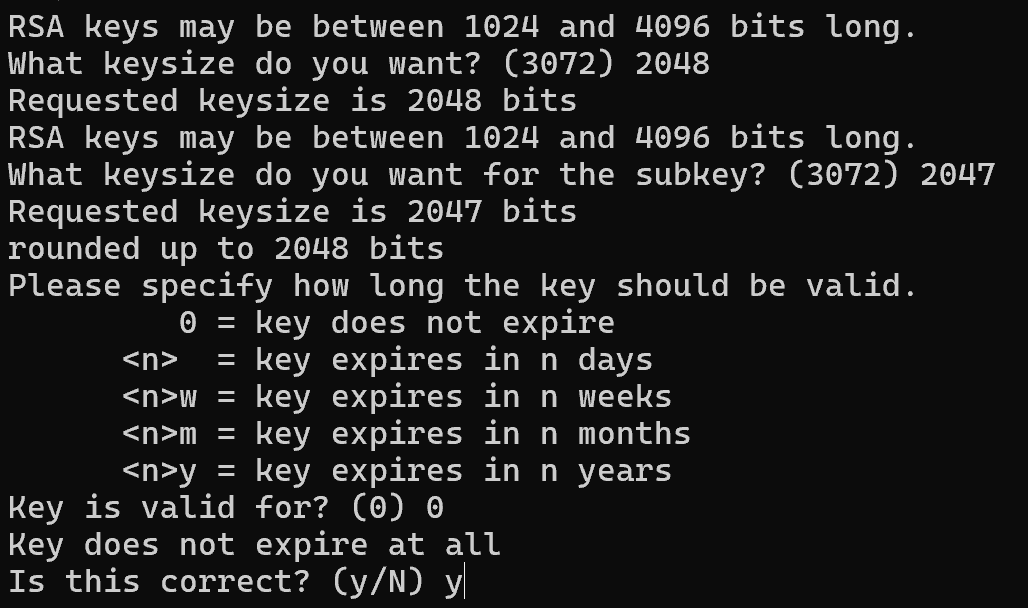
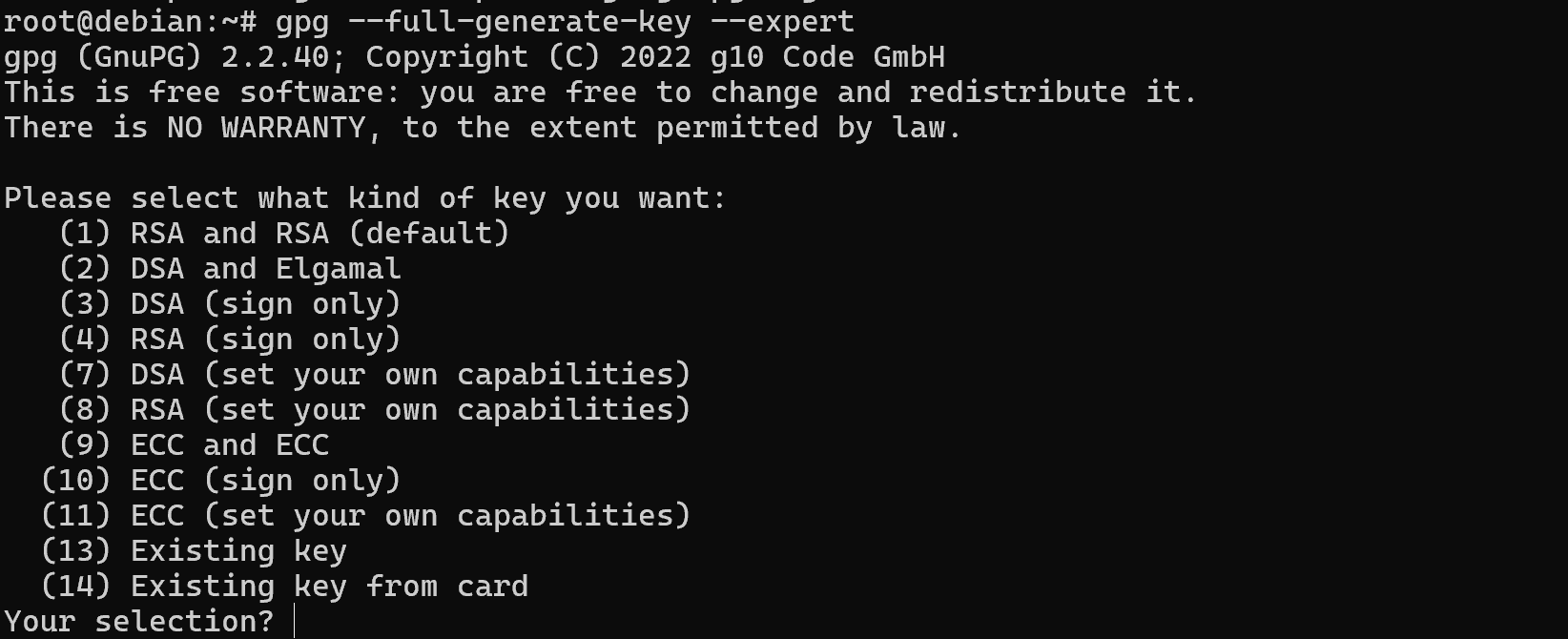
Gpg Key Usage Serverspace Tutorials Gpg, or gnu privacy guard, is a public key cryptography implementation. this allows for the secure transmission of information between parties and can be used to verify that the origin of a message is genuine. in this guide, we will discuss how gpg works and how to implement it. In this article, we show you how to encrypt files with gpg in linux, generate key pairs, share encrypted files securely, and decrypt them. This guide covers installing gpg on various operating systems (windows, macos, and linux), generating a new key pair using modern elliptic curve cryptography (ecc), exporting your public key, encrypting and decrypting files using users’ public keys, and encryption best practices. It’s easy to get started with gpg, and you can be on your way with using it in a matter of minutes. in this tutorial, i’ll show you how to encrypt and decrypt files with gpg.
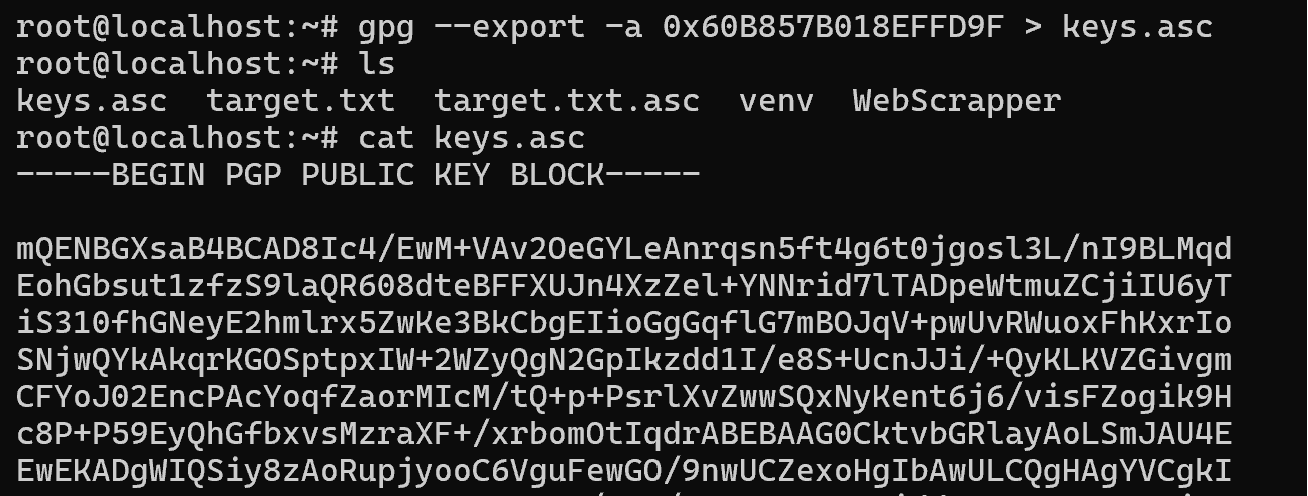
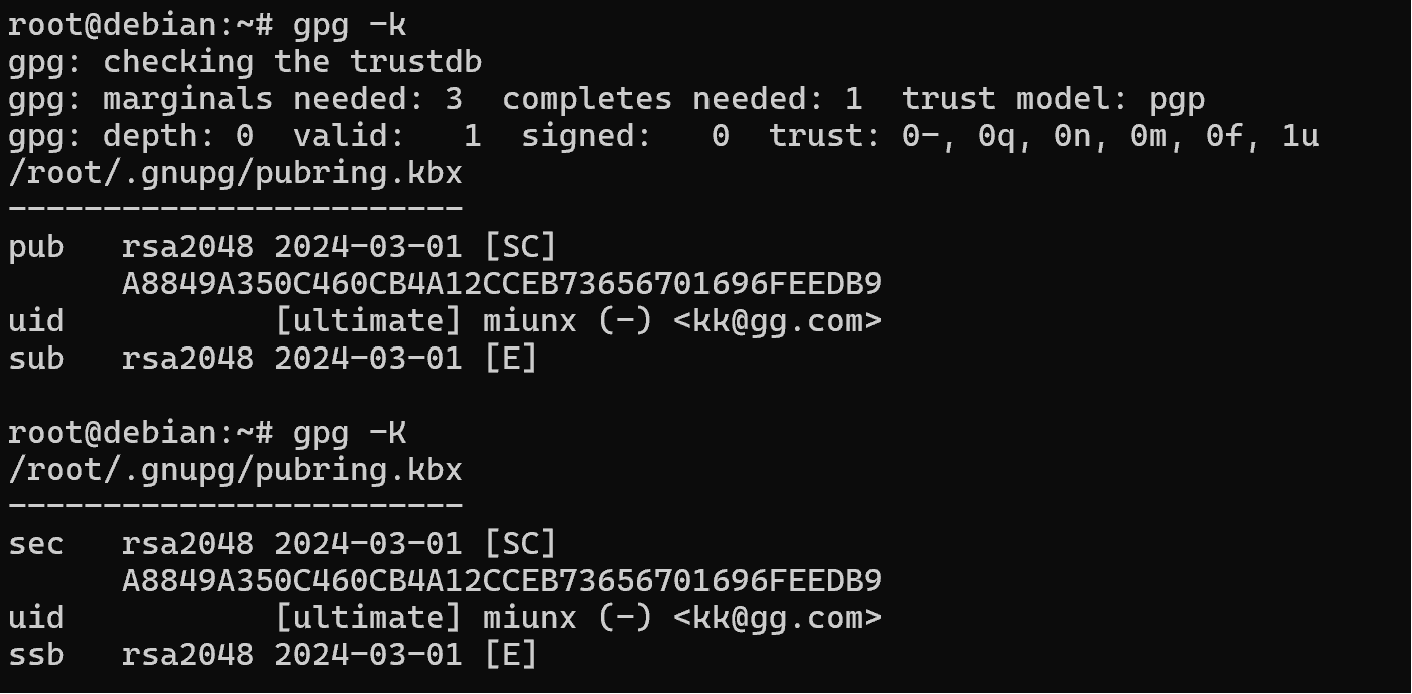
Gpg Key Usage Serverspace Tutorials This guide covers installing gpg on various operating systems (windows, macos, and linux), generating a new key pair using modern elliptic curve cryptography (ecc), exporting your public key, encrypting and decrypting files using users’ public keys, and encryption best practices. It’s easy to get started with gpg, and you can be on your way with using it in a matter of minutes. in this tutorial, i’ll show you how to encrypt and decrypt files with gpg. To share public keys or to backup transfer private keys, you can export them and then importing them into ‘keyrings’ on different media systems. furthermore, for public keys you can share. Master the gpg command in linux with our comprehensive guide. learn to encrypt, decrypt, sign files, manage gpg keys, and integrate with tools like git. perfect for devops and sysadmins. The gpg wks server is a server site implementation of the web key service. it receives requests for publication, sends confirmation requests, receives confirmations, and published the key. Mastering gpg is an essential skill for anyone serious about security and privacy on a linux server. by following this guide, you’ve learned how to generate your gpg key pair, encrypt and decrypt files, sign and verify messages, and manage your gpg keys effectively.
Gpg Key Usage Serverspace Tutorials To share public keys or to backup transfer private keys, you can export them and then importing them into ‘keyrings’ on different media systems. furthermore, for public keys you can share. Master the gpg command in linux with our comprehensive guide. learn to encrypt, decrypt, sign files, manage gpg keys, and integrate with tools like git. perfect for devops and sysadmins. The gpg wks server is a server site implementation of the web key service. it receives requests for publication, sends confirmation requests, receives confirmations, and published the key. Mastering gpg is an essential skill for anyone serious about security and privacy on a linux server. by following this guide, you’ve learned how to generate your gpg key pair, encrypt and decrypt files, sign and verify messages, and manage your gpg keys effectively.
Gpg Key Usage Serverspace Tutorials The gpg wks server is a server site implementation of the web key service. it receives requests for publication, sends confirmation requests, receives confirmations, and published the key. Mastering gpg is an essential skill for anyone serious about security and privacy on a linux server. by following this guide, you’ve learned how to generate your gpg key pair, encrypt and decrypt files, sign and verify messages, and manage your gpg keys effectively.
Gpg Key Usage Serverspace Tutorials
Comments are closed.