Creating A Gpg Key Practicalli Spacemacs
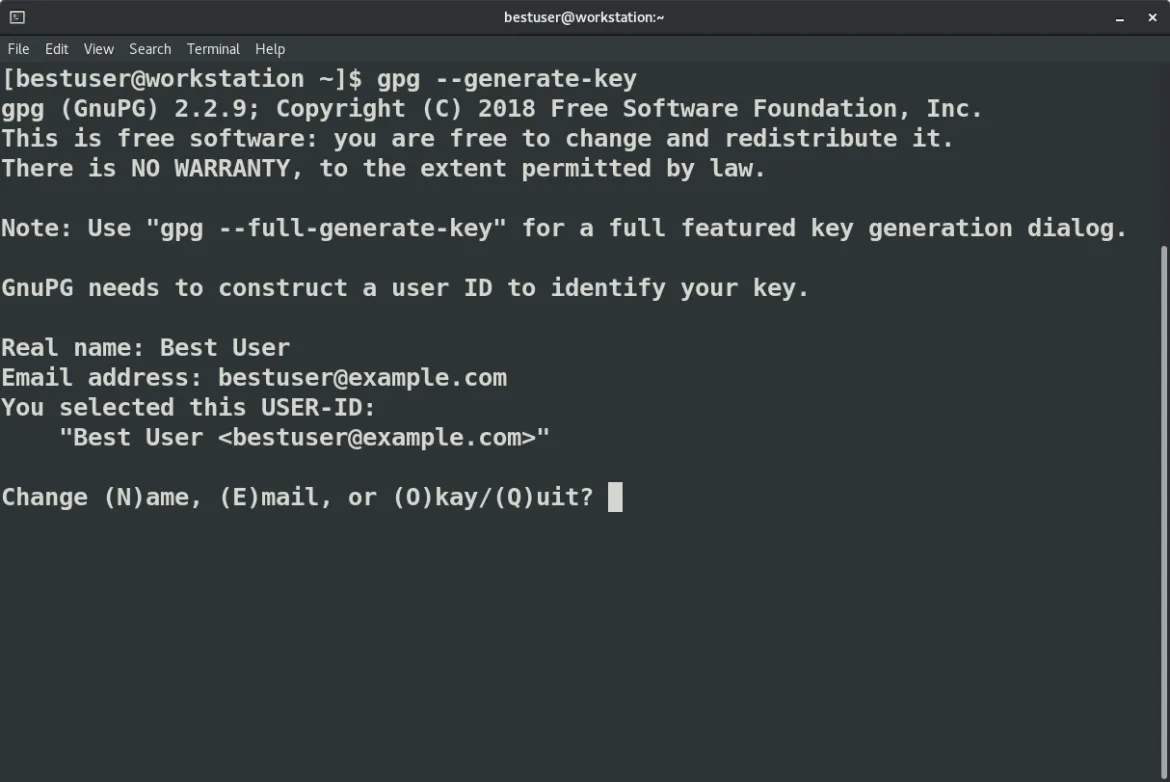
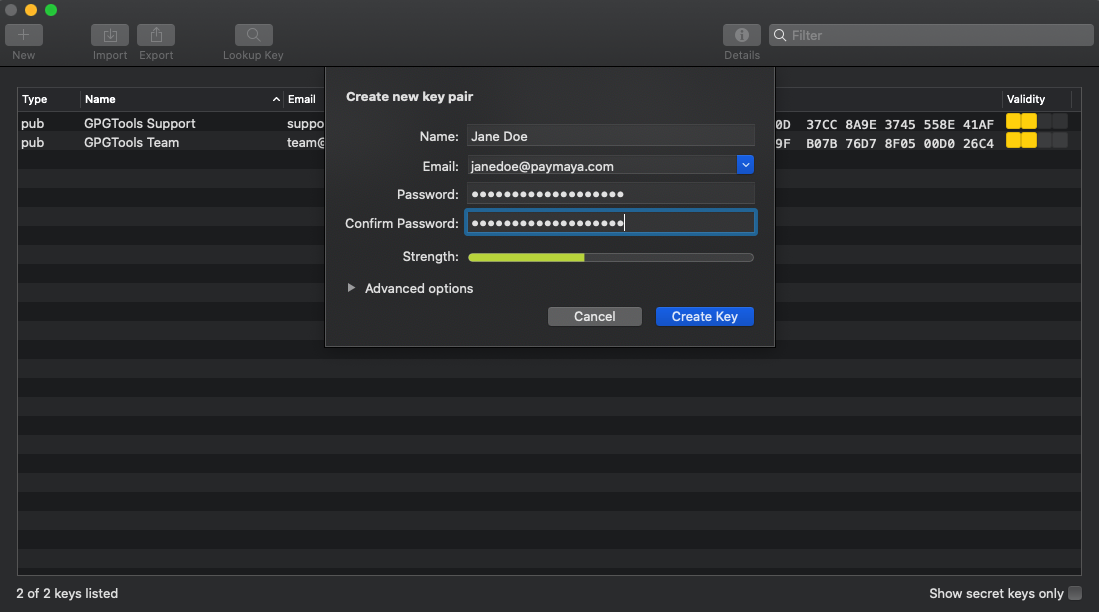
How To Create Gpg Keypairs Those details will be associated with your key. next, you’ll be asked to create a passphrase. this is like the password to your secret key. if you lose it, you’ll have no access to any of the information encrypted with this key. so don’t ever lose it… here’s how this flow looks like:. Those details will be associated with your key. next, you’ll be asked to create a passphrase. this is like the password to your secret key. if you lose it, you’ll have no access to any of the information encrypted with this key. so don’t ever lose it… here’s how this flow looks like:.

8 Gpg Generate 8192 Key Generatekey Create a gpg key (pretty good privacy) to encrypt your github gitlab personal access token in a file called .authinfo.gpg. add your forge username to your ~ .gitconfig file for your operating system account. for example, if your username on github is practicalli, then run this command in a terminal:. Easypg assistant commands are prefixed by ‘epa ’. for example, while the code is focused, press alt f1 for a menu of operations. Creating gpg keys using the command line. this command generates a key pair that consists of a public and a private key. other people use your public key to authenticate and or decrypt your communications. When creating a key, individuals may designate a specific keyserver to use to pull their keys from. it is recommended that you use the following option to ~ .gnupg gpg.conf, which will ignore such designations:.

8 Gpg Generate 8192 Key Generatekey Creating gpg keys using the command line. this command generates a key pair that consists of a public and a private key. other people use your public key to authenticate and or decrypt your communications. When creating a key, individuals may designate a specific keyserver to use to pull their keys from. it is recommended that you use the following option to ~ .gnupg gpg.conf, which will ignore such designations:. Gpg (gnu privacy guard) is a powerful tool for creating cryptographic keys, encrypting and decrypting data, and digitally signing content. this tutorial will guide you through generating gpg keys, exporting and managing them, and using gpg to encrypt, decrypt, and sign messages. At the end of this article, you should be able to generate your own public private key pair and a revocation certificate, which is used to revoke your public private key pair when your private key is compromised or you forget the passphrase for your private key. Gnupg is a tool for secure communication. this chapter is a quick start guide that covers the core functionality of gnupg. this includes keypair creation, exchanging and verifying keys, encrypting and decrypting documents, and authenticating documents with digital signatures. By following the methods that have been detailed above, you will be able to simply generate your own keys using gpg and start encrypting your emails, signing documents, and exchanging information in a secure manner almost immediately.

Creating A Gpg Key Practicalli Spacemacs Gpg (gnu privacy guard) is a powerful tool for creating cryptographic keys, encrypting and decrypting data, and digitally signing content. this tutorial will guide you through generating gpg keys, exporting and managing them, and using gpg to encrypt, decrypt, and sign messages. At the end of this article, you should be able to generate your own public private key pair and a revocation certificate, which is used to revoke your public private key pair when your private key is compromised or you forget the passphrase for your private key. Gnupg is a tool for secure communication. this chapter is a quick start guide that covers the core functionality of gnupg. this includes keypair creation, exchanging and verifying keys, encrypting and decrypting documents, and authenticating documents with digital signatures. By following the methods that have been detailed above, you will be able to simply generate your own keys using gpg and start encrypting your emails, signing documents, and exchanging information in a secure manner almost immediately.
Gpg Guide Gnupg is a tool for secure communication. this chapter is a quick start guide that covers the core functionality of gnupg. this includes keypair creation, exchanging and verifying keys, encrypting and decrypting documents, and authenticating documents with digital signatures. By following the methods that have been detailed above, you will be able to simply generate your own keys using gpg and start encrypting your emails, signing documents, and exchanging information in a secure manner almost immediately.

How To Backup Your Gpg Key In Linux With Paperkey Make Tech Easier
Comments are closed.