Gpg Key Tutorial

Gpg Pgp Tutorial Getbutterfly Learn how gpg encryption protects your data through authenticity, integrity and nonrepudiation. this guide covers installation and symmetric and asymmetric cryptography basics. gnupg, commonly known as gpg, is an open source implementation of the pretty good privacy cryptography standard. This guide covers installing gpg on various operating systems (windows, macos, and linux), generating a new key pair using modern elliptic curve cryptography (ecc), exporting your public key, encrypting and decrypting files using users’ public keys, and encryption best practices.
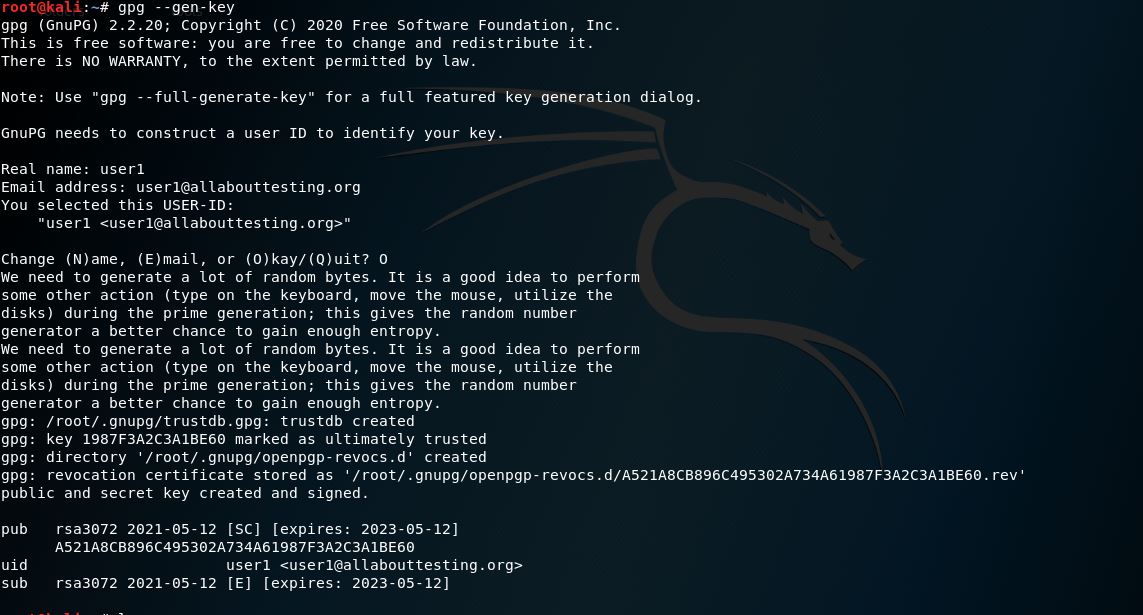
Gpg Gen Key All About Testing In this article, we show you how to encrypt files with gpg in linux, generate key pairs, share encrypted files securely, and decrypt them. It’s easy to get started with gpg, and you can be on your way with using it in a matter of minutes. in this tutorial, i’ll show you how to encrypt and decrypt files with gpg. Gpg, or gnu privacy guard, is a public key cryptography implementation. this allows for the secure transmission of information between parties and can be used to verify that the origin of a message is genuine. in this guide, we will discuss how gpg works and how to implement it. This tutorial series will teach you how to use gpg (gnu privacy guard) in the linux terminal, so you will be able to send encrypted email messages and digitally sign documents.
Create Gpg Keys All About Testing Gpg, or gnu privacy guard, is a public key cryptography implementation. this allows for the secure transmission of information between parties and can be used to verify that the origin of a message is genuine. in this guide, we will discuss how gpg works and how to implement it. This tutorial series will teach you how to use gpg (gnu privacy guard) in the linux terminal, so you will be able to send encrypted email messages and digitally sign documents. Gpg (gnu privacy guard) is a powerful tool for creating cryptographic keys, encrypting and decrypting data, and digitally signing content. this tutorial will guide you through generating gpg keys, exporting and managing them, and using gpg to encrypt, decrypt, and sign messages. Creating a gpg key pair is an essential first step for anyone looking to securely encrypt and sign data. by generating a public and private key pair, users establish a personal identity that they can use to encrypt files, sign documents, or authenticate messages. Learn how to use gpg for secure communication generate your keys, import others' keys, encrypt and decrypt messages. This tutorial covers the methodology for the creation of gpg keys. for those who don't know, gpg is a free open source implementation created in 1991. gpg, also gnu privacy card, uses strong encryption algorithms.

Creating A Gpg Key Practicalli Spacemacs Gpg (gnu privacy guard) is a powerful tool for creating cryptographic keys, encrypting and decrypting data, and digitally signing content. this tutorial will guide you through generating gpg keys, exporting and managing them, and using gpg to encrypt, decrypt, and sign messages. Creating a gpg key pair is an essential first step for anyone looking to securely encrypt and sign data. by generating a public and private key pair, users establish a personal identity that they can use to encrypt files, sign documents, or authenticate messages. Learn how to use gpg for secure communication generate your keys, import others' keys, encrypt and decrypt messages. This tutorial covers the methodology for the creation of gpg keys. for those who don't know, gpg is a free open source implementation created in 1991. gpg, also gnu privacy card, uses strong encryption algorithms.

How To Edit Gpg Key The Security Buddy Learn how to use gpg for secure communication generate your keys, import others' keys, encrypt and decrypt messages. This tutorial covers the methodology for the creation of gpg keys. for those who don't know, gpg is a free open source implementation created in 1991. gpg, also gnu privacy card, uses strong encryption algorithms.
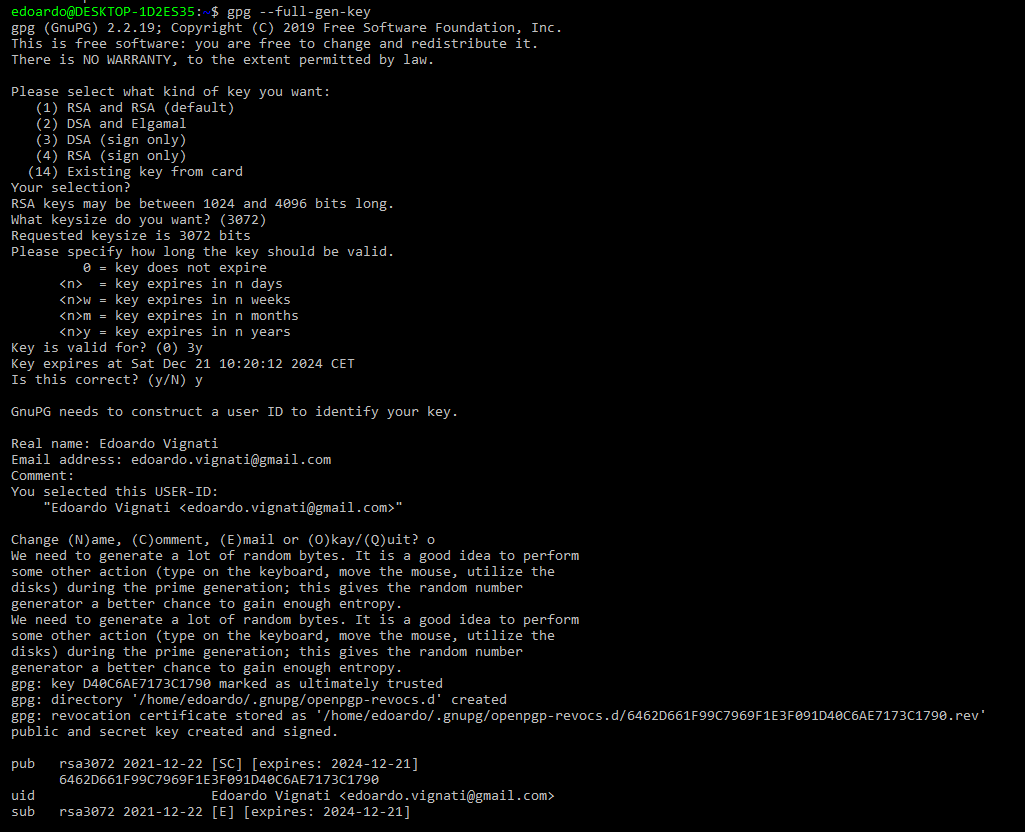
Basic Gpg Pgp Keys Creation And Deployment Tutorial вђ Edoardo Vignati рџ ёрџџ вђќрџ
Comments are closed.