Gpg4usb Project Howto Generate A Gpg Keypair
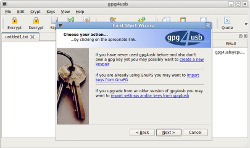
A Practical Guide To Gpg Part 1 Generate Your Keypair Linuxbabe There are four steps for generating a keypair. we assume, that alice wants to generate a keypair, so she can decrypt texts, which are encrypted for her. To say it straight in only one sentence: gpg4usb is a very easy to use portable application, which combines a simple text editor with a gnupg frontend to write, encrypt and decrypt your text messages and files. gpg4usb should work on almost any computer you're working on, should it be a linux machine or even one with a microsoft os running.
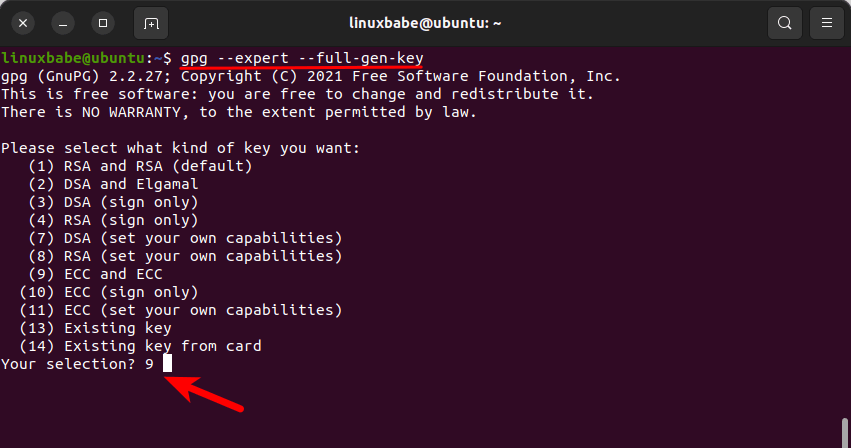
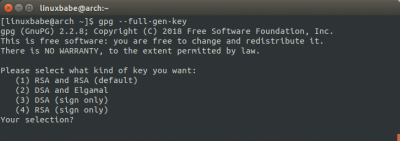
A Practical Guide To Gpg Part 1 Generate Your Public Private Key Pair Here you find some beginner guides to gpg4usb. learn how to use gpg4usb create your private keys and encrypt messages and files. Since there are multiple versions of gpg, you may need to consult the relevant man page to find the appropriate key generation command. if you are on version 2.1.17 or greater, paste the text below to generate a gpg key pair. In this article, we saw how to generate cryptographic keys with gpg and how it can take time due to the lack of randomness. we then saw the various ways by which we can increase the entropy. This guide will walk you through generating a gpg keypair on linux, understanding its components, and creating secure backups. by the end, you’ll have a robust setup to protect your data and recover from key loss or compromise.
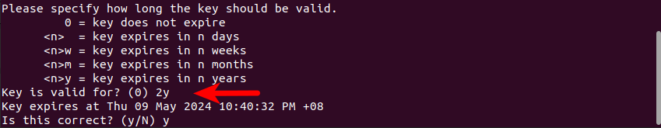
A Practical Guide To Gpg Part 1 Generate Your Public Private Key Pair In this article, we saw how to generate cryptographic keys with gpg and how it can take time due to the lack of randomness. we then saw the various ways by which we can increase the entropy. This guide will walk you through generating a gpg keypair on linux, understanding its components, and creating secure backups. by the end, you’ll have a robust setup to protect your data and recover from key loss or compromise. The main interface will be familiar to anyone who has used pgp gpg encryption in the past, you can create a keypair, import, export encryption keys, check key properties, upload keys to a keyserver, sign files, encrypt and decrypt files. This post is meant to simplify the procedure for generating gnupg keys on a linux machine. in the example below, i am generating a 4096 bit rsa public private key pair. The most common tool for this is gnupg (gpg), a free and open source implementation of the openpgp standard. below, we outline the process of generating your public and private keys using gpg, but the general principles apply to other pgp software as well. At the end of this article, you should be able to generate your own public private key pair and a revocation certificate, which is used to revoke your public private key pair when your private key is compromised or you forget the passphrase for your private key.
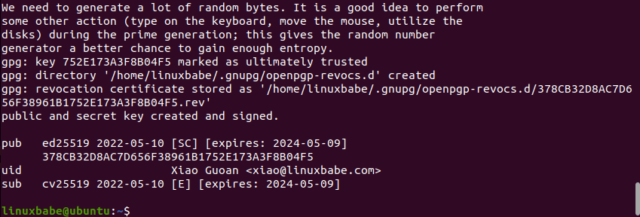
A Practical Guide To Gpg Part 1 Generate Your Public Private Key Pair The main interface will be familiar to anyone who has used pgp gpg encryption in the past, you can create a keypair, import, export encryption keys, check key properties, upload keys to a keyserver, sign files, encrypt and decrypt files. This post is meant to simplify the procedure for generating gnupg keys on a linux machine. in the example below, i am generating a 4096 bit rsa public private key pair. The most common tool for this is gnupg (gpg), a free and open source implementation of the openpgp standard. below, we outline the process of generating your public and private keys using gpg, but the general principles apply to other pgp software as well. At the end of this article, you should be able to generate your own public private key pair and a revocation certificate, which is used to revoke your public private key pair when your private key is compromised or you forget the passphrase for your private key.
Gpg4usb Project Home The most common tool for this is gnupg (gpg), a free and open source implementation of the openpgp standard. below, we outline the process of generating your public and private keys using gpg, but the general principles apply to other pgp software as well. At the end of this article, you should be able to generate your own public private key pair and a revocation certificate, which is used to revoke your public private key pair when your private key is compromised or you forget the passphrase for your private key.
Comments are closed.