Gpg Encryption Decryption Cryptography Key Cryptography
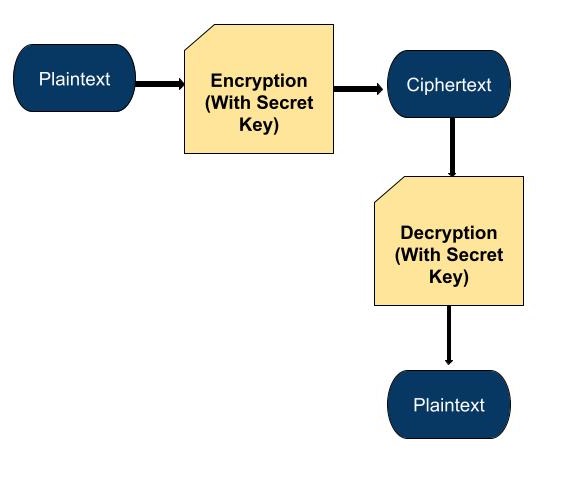
Cryptography Symmetric Key Encryption Learn how gpg encryption protects your data through authenticity, integrity and nonrepudiation. this guide covers installation and symmetric and asymmetric cryptography basics. The encrypted document can only be decrypted by someone with a private key that complements one of the recipients' public keys. in particular, you cannot decrypt a document encrypted by you unless you included your own public key in the recipient list.

Public Key Encryption In Cryptography In this article, we show you how to encrypt files with gpg in linux, generate key pairs, share encrypted files securely, and decrypt them. It’s easy to get started with gpg, and you can be on your way with using it in a matter of minutes. in this tutorial, i’ll show you how to encrypt and decrypt files with gpg. Encrypt and decrypt using gpg gpg is an implementation of pgp (pretty good privacy) cryptography method which uses a pair of private and public keys for the encryption and decryption of the messages. Comprehensive technical guide to gpg pgp encryption covering key generation, message encryption decryption, digital signatures, enterprise implementation, and advanced security practices.

Encryption And Decryption Using Public Key Cryptography Download Encrypt and decrypt using gpg gpg is an implementation of pgp (pretty good privacy) cryptography method which uses a pair of private and public keys for the encryption and decryption of the messages. Comprehensive technical guide to gpg pgp encryption covering key generation, message encryption decryption, digital signatures, enterprise implementation, and advanced security practices. Gnu privacy guard (gpg) is a free and open source command line tool that allows you to encrypt, decrypt, and sign data and communications. it implements the open pretty good privacy (openpgp) standard, providing secure message exchange through public key cryptography. Gpg (gnu privacy guard) is a free and open source implementation of the openpgp standard. it allows you to encrypt, decrypt, sign, and verify messages and files securely using public key cryptography. Gpg, or gnu privacy guard, is a public key cryptography implementation. this allows for the secure transmission of information between parties and can be used to verify that the origin of a message is genuine. in this guide, we will discuss how gpg works and how to implement it. Gpg in python offers a powerful way to add encryption and signing capabilities to your python applications. by understanding the fundamental concepts, mastering the usage methods, following common practices, and adhering to best practices, you can ensure the security and integrity of your data.

Cryptography Using Gpg For Encryption And Key Management Virtual Lab Gnu privacy guard (gpg) is a free and open source command line tool that allows you to encrypt, decrypt, and sign data and communications. it implements the open pretty good privacy (openpgp) standard, providing secure message exchange through public key cryptography. Gpg (gnu privacy guard) is a free and open source implementation of the openpgp standard. it allows you to encrypt, decrypt, sign, and verify messages and files securely using public key cryptography. Gpg, or gnu privacy guard, is a public key cryptography implementation. this allows for the secure transmission of information between parties and can be used to verify that the origin of a message is genuine. in this guide, we will discuss how gpg works and how to implement it. Gpg in python offers a powerful way to add encryption and signing capabilities to your python applications. by understanding the fundamental concepts, mastering the usage methods, following common practices, and adhering to best practices, you can ensure the security and integrity of your data.
Comments are closed.