Gpg Encryption Cloakguru Documentation

Automate Open Pgp And Gpg Encryption Goanywhere Mft Gpg encryption on this page, you will see how you can import your gpg encryption key and force cloakguru to encrypt all the emails forwarded to you using your key. Refer to the menu on the left sidebar to access the entire cloakguru knowledge base!.
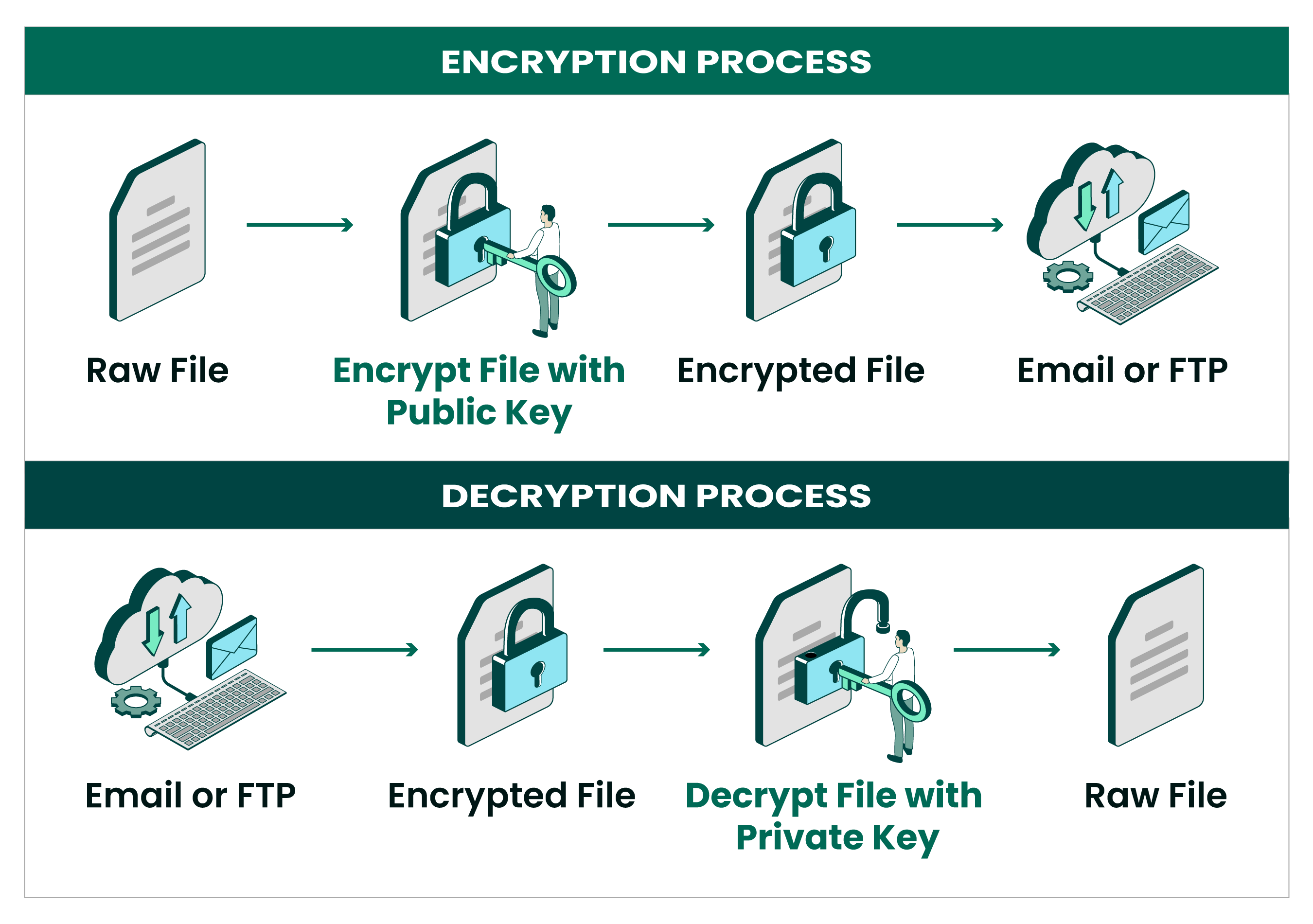
Automate Open Pgp And Gpg Encryption Goanywhere Mft This section provides a step by step guide on generating your key pair, sharing your public key, and configuring your email client to use gpg encryption, laying the groundwork for secure email communication. Find a list of some key features provided by cloakguru we think you will love:. Is my alias permanent? can cloakguru encrypts my email with my own gpg key? yes, cloakguru supports gpg encryption. cloakguru will encrypt email body and all attachments using your gpg public key to ensure maximum protection. The procedure for encrypting and decrypting documents is straightforward with this mental model. if you want to encrypt a message to alice, you encrypt it using alice's public key, and she decrypts it with her private key.
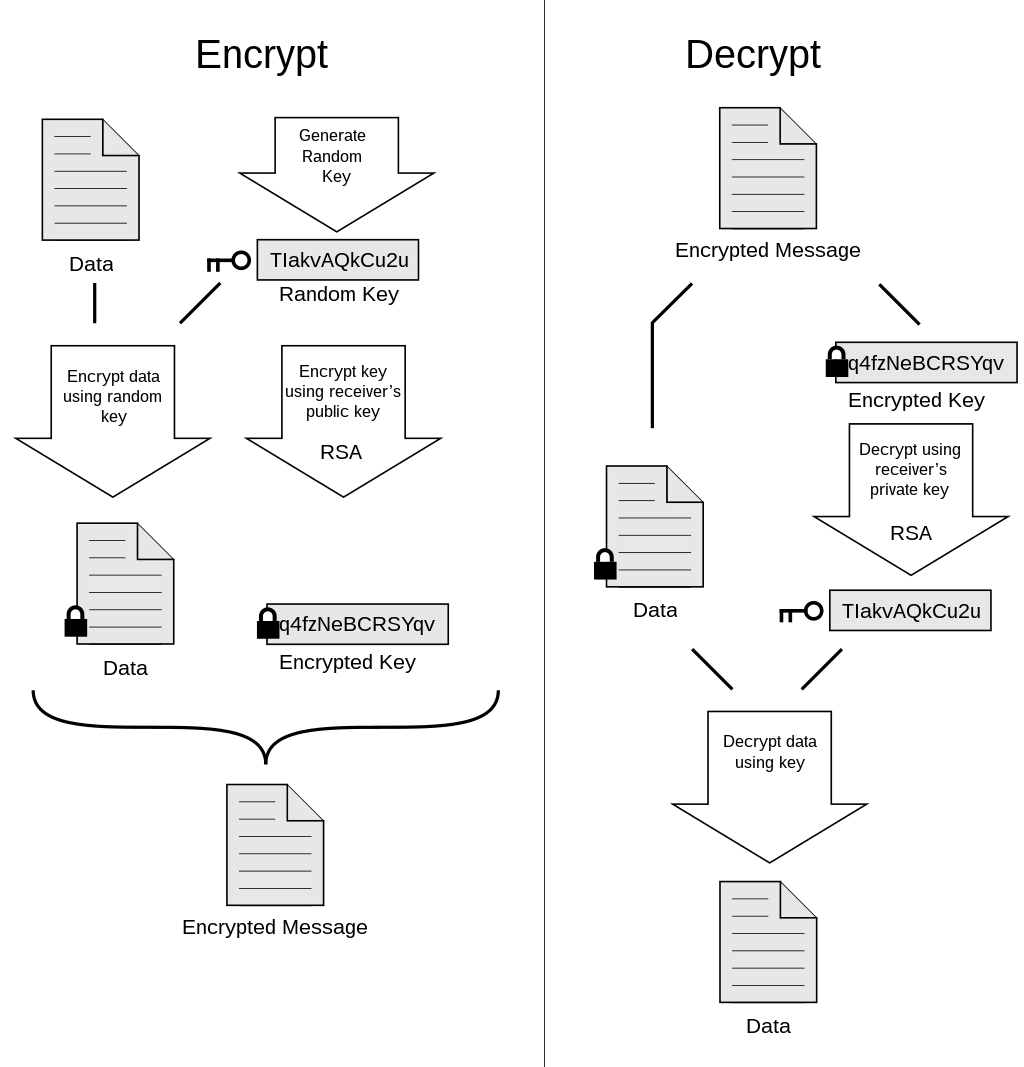
What Is Gpg Encryption And Do You Need It Liquid Web Is my alias permanent? can cloakguru encrypts my email with my own gpg key? yes, cloakguru supports gpg encryption. cloakguru will encrypt email body and all attachments using your gpg public key to ensure maximum protection. The procedure for encrypting and decrypting documents is straightforward with this mental model. if you want to encrypt a message to alice, you encrypt it using alice's public key, and she decrypts it with her private key. Learn how gpg encryption protects your data through authenticity, integrity and nonrepudiation. this guide covers installation and symmetric and asymmetric cryptography basics. In this article, we show you how to encrypt files with gpg in linux, generate key pairs, share encrypted files securely, and decrypt them. It’s easy to get started with gpg, and you can be on your way with using it in a matter of minutes. in this tutorial, i’ll show you how to encrypt and decrypt files with gpg. But these three are easy to use encryption and decryption options that will get you started protecting your files right away. i will demonstrate some of the other options in a future article unless one of you wants to do that and submit it to enable sysadmin for publication.

Architecting Secure And Compliant Managed File Transfers With Aws Learn how gpg encryption protects your data through authenticity, integrity and nonrepudiation. this guide covers installation and symmetric and asymmetric cryptography basics. In this article, we show you how to encrypt files with gpg in linux, generate key pairs, share encrypted files securely, and decrypt them. It’s easy to get started with gpg, and you can be on your way with using it in a matter of minutes. in this tutorial, i’ll show you how to encrypt and decrypt files with gpg. But these three are easy to use encryption and decryption options that will get you started protecting your files right away. i will demonstrate some of the other options in a future article unless one of you wants to do that and submit it to enable sysadmin for publication.

Getting Started With Gpg Gnupg It’s easy to get started with gpg, and you can be on your way with using it in a matter of minutes. in this tutorial, i’ll show you how to encrypt and decrypt files with gpg. But these three are easy to use encryption and decryption options that will get you started protecting your files right away. i will demonstrate some of the other options in a future article unless one of you wants to do that and submit it to enable sysadmin for publication.
Comments are closed.