Github Yihan0512 Power Side Channel Attack Aes128
Power Side Channel Attack On Software Implemented Aes Embedded Systems Contribute to yihan0512 power side channel attack aes128 development by creating an account on github. Contribute to yihan0512 power side channel attack aes128 development by creating an account on github.
Power Side Channel Attack On Software Implemented Aes Embedded Systems Contribute to yihan0512 power side channel attack aes128 development by creating an account on github. Contribute to yihan0512 power side channel attack aes128 development by creating an account on github. These papers provide a good starting point for understanding the vulnerabilities of aes 128 to side channel attacks, and various techniques and countermeasures that have been proposed to mitigate these vulnerabilities. Contribute to yihan0512 power side channel attack aes128 development by creating an account on github.
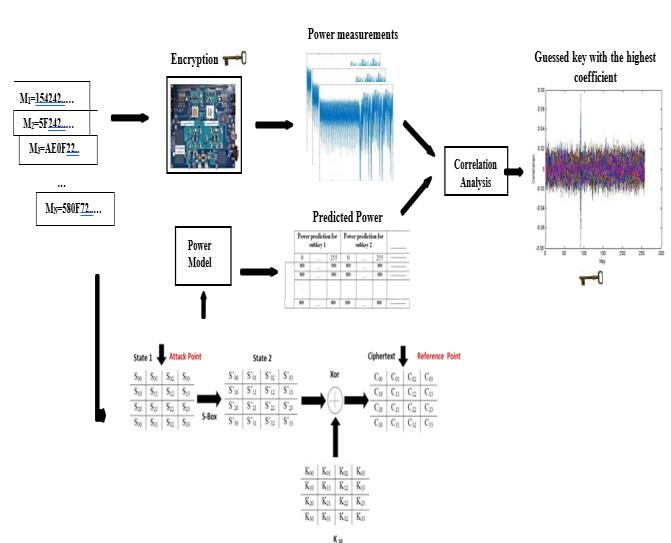
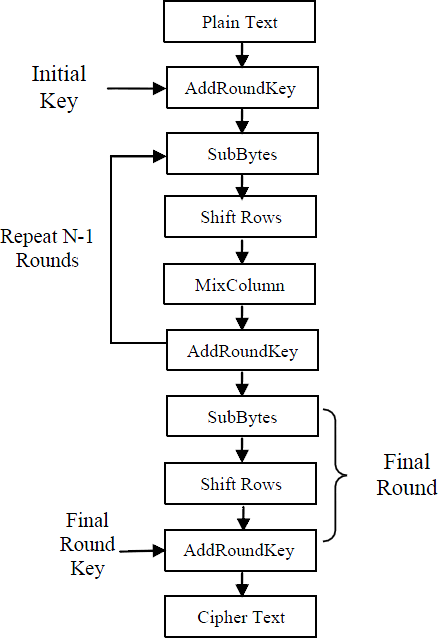
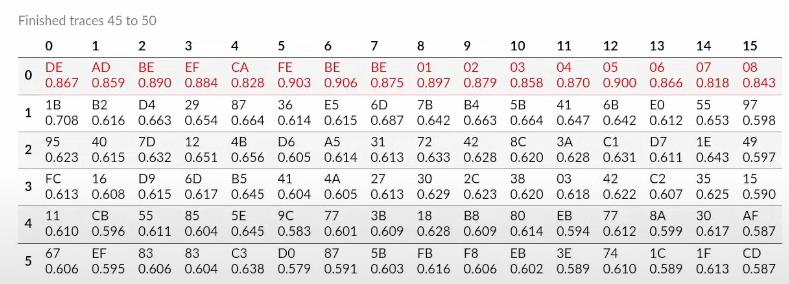
Power Side Channel Attack On Software Implemented Aes Embedded Systems These papers provide a good starting point for understanding the vulnerabilities of aes 128 to side channel attacks, and various techniques and countermeasures that have been proposed to mitigate these vulnerabilities. Contribute to yihan0512 power side channel attack aes128 development by creating an account on github. We loaded a standard avr architecture aes 128 implementation onto the chip and encrypted randomly chosen plaintexts with several different keys. Side channel attacks (scas), an attack that exploits the physical information generated when an encryption algorithm is executed on a device to recover the key,. Introduction power analysis is a branch of side channel attacks where the side channel used is the power consumption. in electronic devices, the instantaneous power consumption is dependent on the data that is being processed in the device as well as the operation performed by that device. This paper reviews various machine learning based power side channel attacks, including feature extraction techniques, classification methods, and countermeasures.
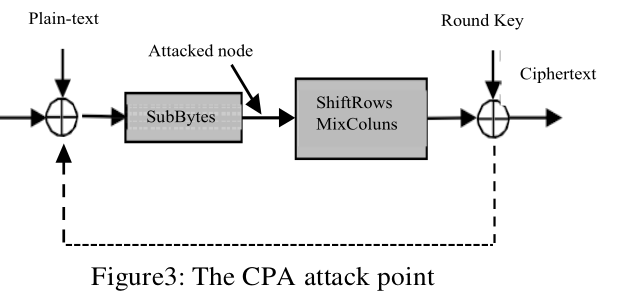
Power Side Channel Attack On Software Implemented Aes Embedded Systems We loaded a standard avr architecture aes 128 implementation onto the chip and encrypted randomly chosen plaintexts with several different keys. Side channel attacks (scas), an attack that exploits the physical information generated when an encryption algorithm is executed on a device to recover the key,. Introduction power analysis is a branch of side channel attacks where the side channel used is the power consumption. in electronic devices, the instantaneous power consumption is dependent on the data that is being processed in the device as well as the operation performed by that device. This paper reviews various machine learning based power side channel attacks, including feature extraction techniques, classification methods, and countermeasures.

Side Channel Attack Setup For Power Leakage Based Evaluations Introduction power analysis is a branch of side channel attacks where the side channel used is the power consumption. in electronic devices, the instantaneous power consumption is dependent on the data that is being processed in the device as well as the operation performed by that device. This paper reviews various machine learning based power side channel attacks, including feature extraction techniques, classification methods, and countermeasures.
Comments are closed.