Github Bhargavi369 Signature Verification Using The Rsa Algorithm
Github Bhargavi369 Signature Verification Using The Rsa Algorithm The rsa public key cryptosystem provides a digital signature scheme (sign verify), based on the math of the modular exponentiations and discrete logarithms and the computational difficulty of the rsa problem. Contribute to bhargavi369 signature verification using the rsa algorithm development by creating an account on github.
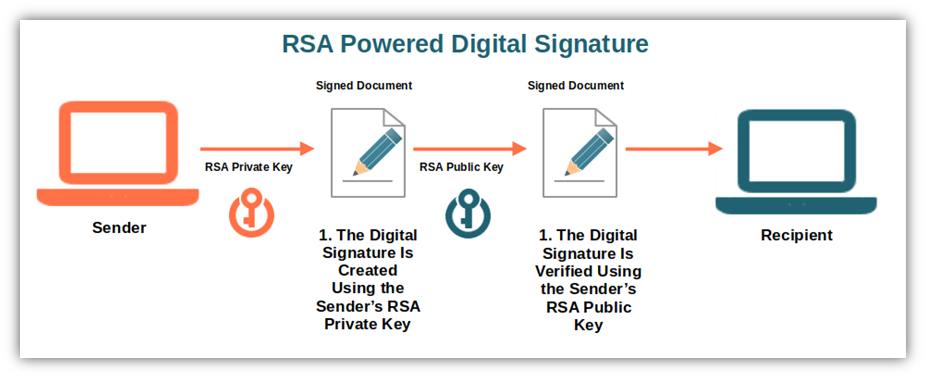
What Is The Rsa Algorithm A Look At Rsa Encryption Contribute to bhargavi369 signature verification using the rsa algorithm development by creating an account on github. After the keys are generated, we shall compute rsa digital signatures and verify signatures by a simple modular exponentiation (by encrypting and decrypting the message hash). From lectures, students should have learned the theoretic part of the rsa algorithm, so they know mathematically how to generate public private keys and how to perform encryption decryption and signature generation verification. Digital signatures are used to verify the authenticity of the message sent electronically. a digital signature algorithm uses a public key system. the intended transmitter signs his her message with his her private key and the intended receiver verifies it with the transmitter’s public key.
Digital Signature Using Rsa Algorithm Youtube From lectures, students should have learned the theoretic part of the rsa algorithm, so they know mathematically how to generate public private keys and how to perform encryption decryption and signature generation verification. Digital signatures are used to verify the authenticity of the message sent electronically. a digital signature algorithm uses a public key system. the intended transmitter signs his her message with his her private key and the intended receiver verifies it with the transmitter’s public key. The implementation described above outlines the foundational steps of creating and verifying digital signatures with the rsa algorithm in python. below is an example output of the signing. Being able to do both encryption and digital signatures is one of the rsa algorithm’s key benefits. to confirm that the message has not been tampered with, digital signatures are made by encrypting a message hash with the sender’s private key. In this exercise we shall sign messages and verify signatures using the pkcs#1 v.1.5 rsa signature algorithm with 4096 bit keys, following the technical specification from rfc 8017, using sha3 512 for hashing the input message. The aim of this study is to present an improved algorithm modified from rsa for signing and verifying digital signatures. the main goal is to optimize computing resources in modular multiplication and modular square operations.
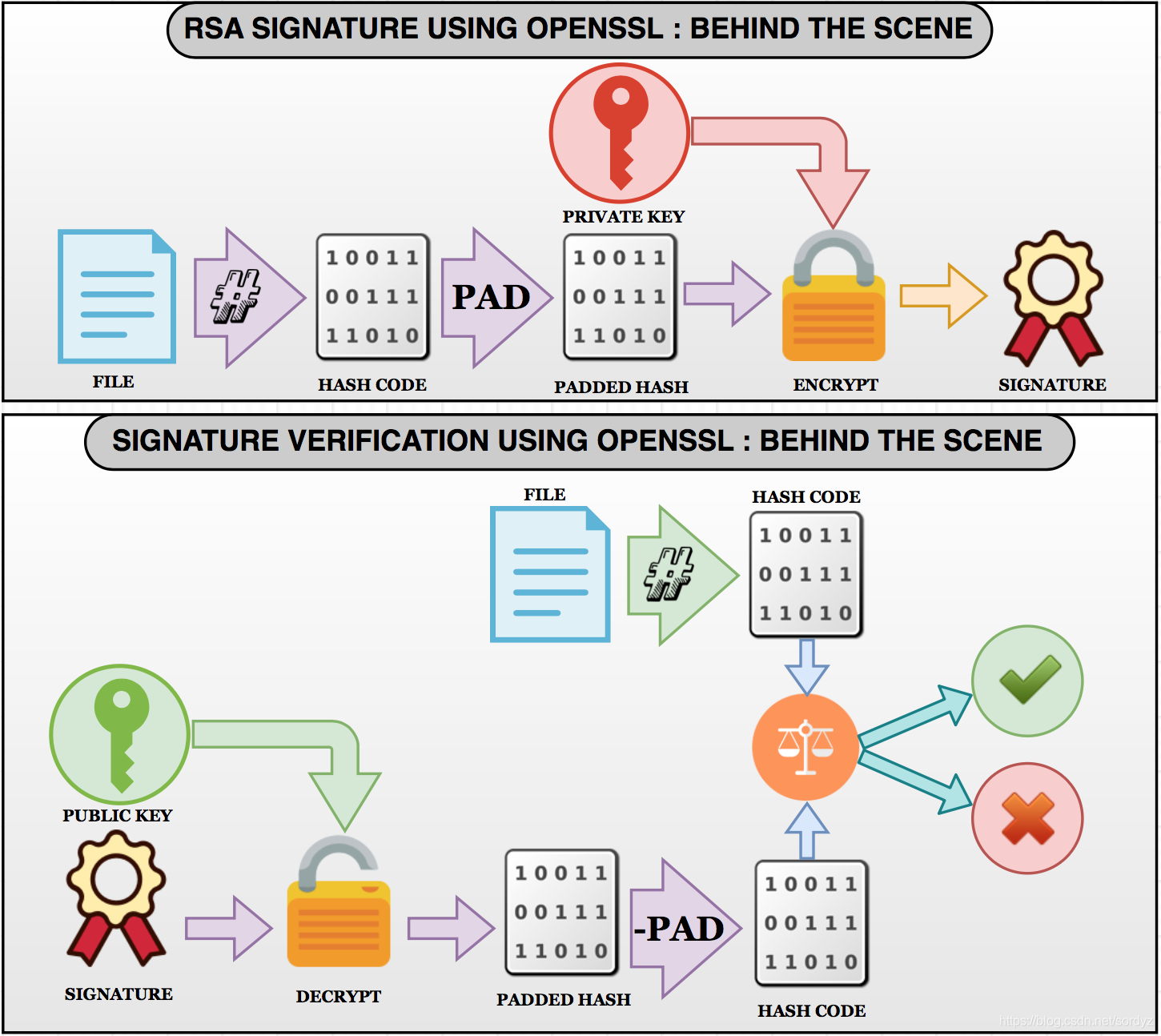
Rsa Sign And Verify Rsa Sign Verify Csdn博客 The implementation described above outlines the foundational steps of creating and verifying digital signatures with the rsa algorithm in python. below is an example output of the signing. Being able to do both encryption and digital signatures is one of the rsa algorithm’s key benefits. to confirm that the message has not been tampered with, digital signatures are made by encrypting a message hash with the sender’s private key. In this exercise we shall sign messages and verify signatures using the pkcs#1 v.1.5 rsa signature algorithm with 4096 bit keys, following the technical specification from rfc 8017, using sha3 512 for hashing the input message. The aim of this study is to present an improved algorithm modified from rsa for signing and verifying digital signatures. the main goal is to optimize computing resources in modular multiplication and modular square operations.
Comments are closed.