Fog Computing For Reduced Latency Icon Ppt Example

Fog Computing For Reduced Latency Icon Ppt Example The topics discussed in these slides are fog computing, reduced latency icon. this is an immediately available powerpoint presentation that can be conveniently customized. The document discusses security and privacy challenges, including authentication issues and attacks like man in the middle, while proposing future enhancements to improve fog computing capabilities. download as a pptx, pdf or view online for free.

Fog Computing Powerpoint Ppt Template Bundles Ppt Slide Fog computing extends cloud computing by processing data closer to the source, reducing latency and improving efficiency for real time applications. it is crucial for smart cities, healthcare, and industrial iot, enabling real time decision making and optimizing bandwidth usage. Lay your hands on our well researched fog computing ppt template to describe how fog computing facilitates real time automation and network data processing without high latency and low bandwidth issues. 14 advantages of fog computing fog aims to place the data close to the end users. big data and analytics can be done faster with better results. administrators are able to support location based mobiliy demands and not have to traverse the entire network. enhance the cloud experience by isolating user data that needs to live on the edge . 15. Edge devices request compute, storage and communication services from the fog. the fog provides local, low latency response to these requests and forwards relevant data for computationally intensive processing.

Latency Special Flat Icon 14 advantages of fog computing fog aims to place the data close to the end users. big data and analytics can be done faster with better results. administrators are able to support location based mobiliy demands and not have to traverse the entire network. enhance the cloud experience by isolating user data that needs to live on the edge . 15. Edge devices request compute, storage and communication services from the fog. the fog provides local, low latency response to these requests and forwards relevant data for computationally intensive processing. Enter fog computing, a paradigm that addresses these issues by extending cloud computing capabilities to the edge of the network. this article delves into the concept of fog computing in iot and provides insights for creating an insightful powerpoint presentation on the topic. It highlights the need for low latency processing and local data management, emphasizing the role of fog nodes in enhancing efficiency and security in various applications such as healthcare, smart cities, and traffic control. Edge fog computing iot motivates the need for a hierarchical platform that extends from the edge to the core of the network. Fog computing mitigates insider data theft in cloud environments through offensive decoy technology. the proposed method uses user behavior profiling and decoy information to enhance security.
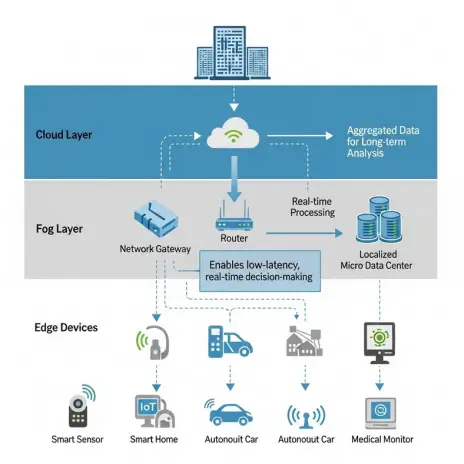
Fog Computing For Low Latency Applications Enter fog computing, a paradigm that addresses these issues by extending cloud computing capabilities to the edge of the network. this article delves into the concept of fog computing in iot and provides insights for creating an insightful powerpoint presentation on the topic. It highlights the need for low latency processing and local data management, emphasizing the role of fog nodes in enhancing efficiency and security in various applications such as healthcare, smart cities, and traffic control. Edge fog computing iot motivates the need for a hierarchical platform that extends from the edge to the core of the network. Fog computing mitigates insider data theft in cloud environments through offensive decoy technology. the proposed method uses user behavior profiling and decoy information to enhance security.

Latency Generic Color Lineal Color Icon Edge fog computing iot motivates the need for a hierarchical platform that extends from the edge to the core of the network. Fog computing mitigates insider data theft in cloud environments through offensive decoy technology. the proposed method uses user behavior profiling and decoy information to enhance security.

Latency Generic Flat Gradient Icon
Comments are closed.