Exploit Cve 2025 39596 Hackingtutorial Websecurity Bugbounty Defacewebsite Belajarhacking
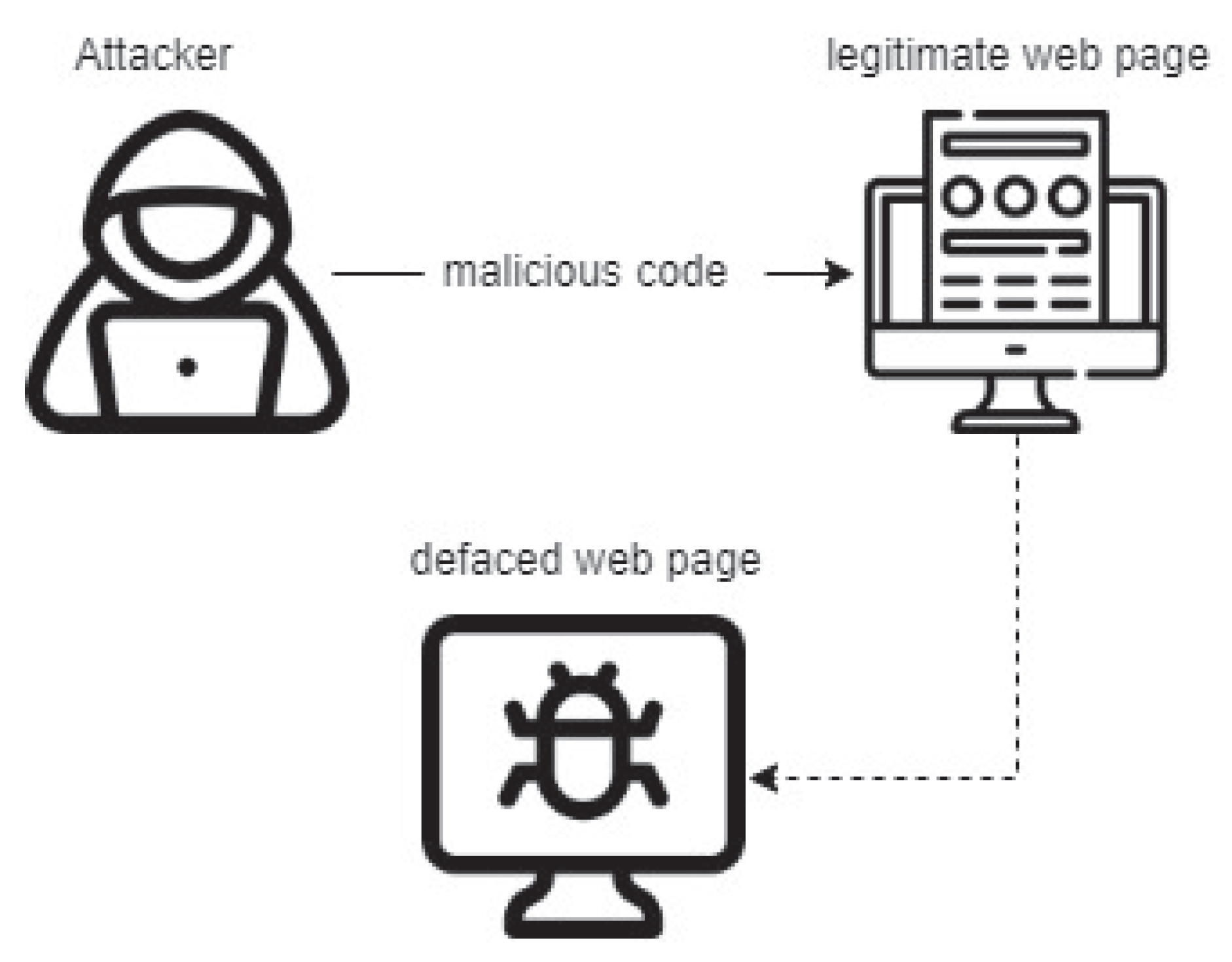
Website Defacement Detection And Monitoring Methods A Review Below is the impact analysis for cve 2025 39596, showing how confidentiality, integrity, and availability might be affected if the vulnerability is exploited. Understand the critical aspects of cve 2025 39596 with a detailed vulnerability assessment, exploitation potential, affected technologies, and remediation guidance.

Bug Bounties Total Cyber Solutions Training Site Cve 2025 39596 is a privilege escalation vulnerability in quentn wp caused by weak authentication. attackers can exploit this flaw to gain elevated privileges. this article covers technical details, affected versions, and mitigation. The exploit database exploits, shellcode, 0days, remote exploits, local exploits, web apps, vulnerability reports, security articles, tutorials and more. Weak authentication vulnerability in quentn gmbh quentn wp allows privilege escalation. this issue affects quentn wp: from n a through 1.2.8. This repository contains a python exploit for cve 2025 39596, allowing the creation of a new wordpress admin user without authentication using a crafted api request.
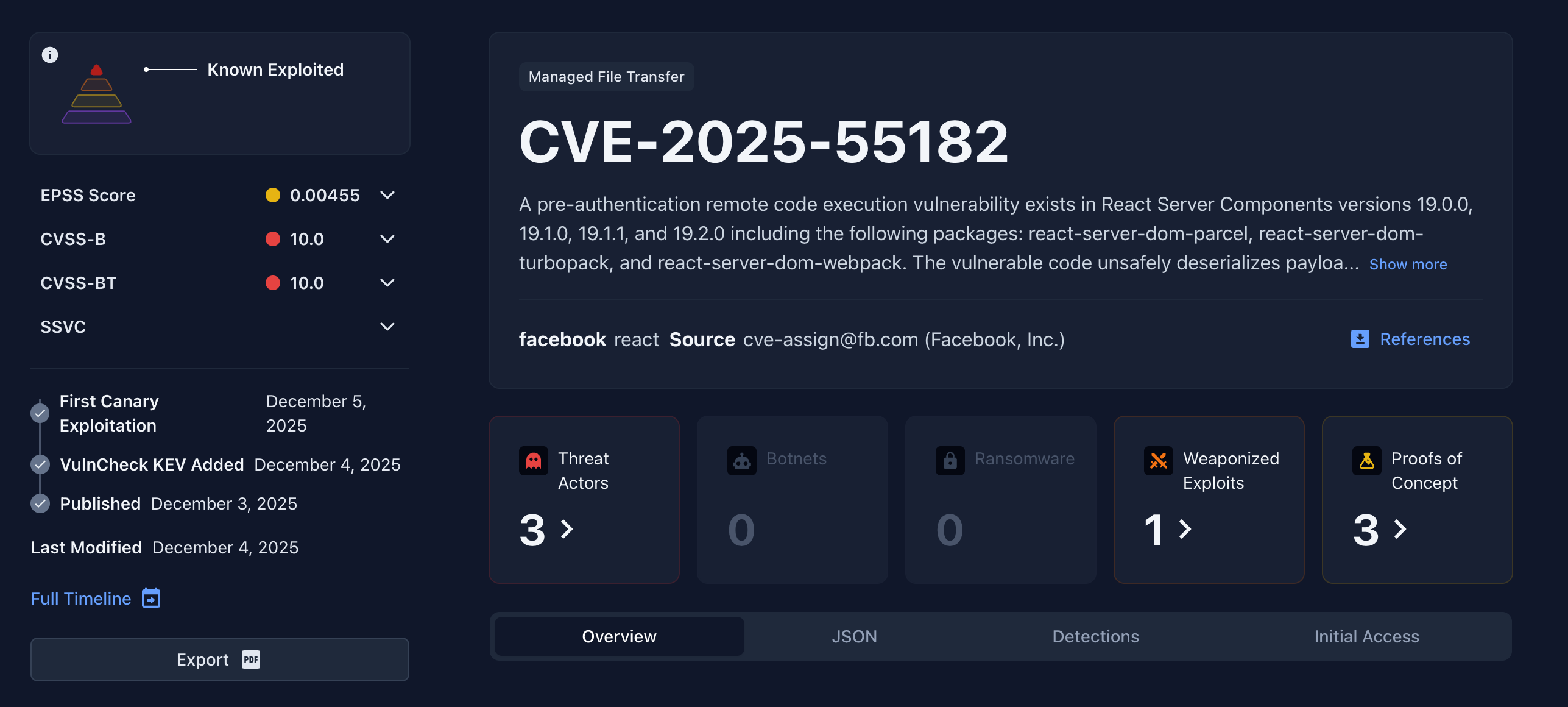
Critical Vulnerability In React And Next Js Cve 2025 55182 Blog Weak authentication vulnerability in quentn gmbh quentn wp allows privilege escalation. this issue affects quentn wp: from n a through 1.2.8. This repository contains a python exploit for cve 2025 39596, allowing the creation of a new wordpress admin user without authentication using a crafted api request. This common vulnerabilities and exposures (cve) entry provides detailed information about a security vulnerability that has been publicly disclosed. cves are standardized identifiers assigned by mitre corporation to track and catalog security vulnerabilities across software and hardware products. Exploit cve 2025 39596 #hackingtutorial #websecurity #bugbounty #defacewebsite #belajarhacking friends exploit 1.89k subscribers subscribe. This repository contains a python exploit for cve 2025 39596, allowing the creation of a new wordpress admin user without authentication using a crafted api request. This is the first post in a tutorial series that will help showcase how trivial it can be for a hacker to exploit public facing web applications. throughout this series, i will lay out my thought process with hopes that it will not only be beneficial for the reader of this blog, but also for myself as i continue to learn.

13 Tanda Website Kena Hack Berhati Hatilah This common vulnerabilities and exposures (cve) entry provides detailed information about a security vulnerability that has been publicly disclosed. cves are standardized identifiers assigned by mitre corporation to track and catalog security vulnerabilities across software and hardware products. Exploit cve 2025 39596 #hackingtutorial #websecurity #bugbounty #defacewebsite #belajarhacking friends exploit 1.89k subscribers subscribe. This repository contains a python exploit for cve 2025 39596, allowing the creation of a new wordpress admin user without authentication using a crafted api request. This is the first post in a tutorial series that will help showcase how trivial it can be for a hacker to exploit public facing web applications. throughout this series, i will lay out my thought process with hopes that it will not only be beneficial for the reader of this blog, but also for myself as i continue to learn.
Comments are closed.