Exploit Cve 2025 47539 Bugbounty Hackingcourse Ethicalhacking

Cve 2025 43859 Security Vulnerability Exploit Details Jon tackles trump's king ish antics & kosta covers doj shakedown and east wing demo | the daily show. This python script is a standalone exploitation tool for cve 2025 47539. it will: auto generate a valid csv payload file. upload the file to the vulnerable endpoint. automatically trigger the import process. provide immediate feedback including full credentials of the created admin account.
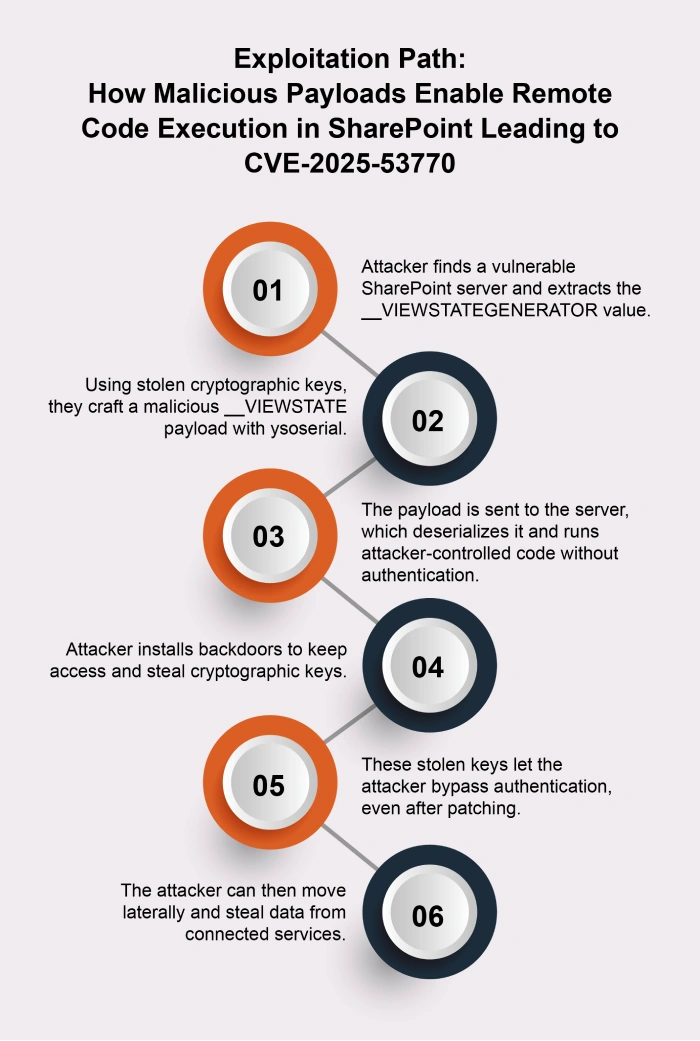
Cve 2025 53770 Sharepoint Auth Bypass Risk Fidelis Security Incorrect privilege assignment vulnerability in themewinter eventin allows privilege escalation. this issue affects eventin: from n a through 4.0.26. published: 2025 05 23. Enrichment data supplied by the nvd may require amendment due to these changes. incorrect privilege assignment vulnerability in arraytics eventin wp event solution allows privilege escalation.this issue affects eventin: from n a through <= 4.0.26. incorrect privilege assignment vulnerability in themewinter eventin allows privilege escalation. Cve 2025 47539 vulnerability intelligence. threat score 20 100. cvss, epss, exploit data, and threat analysis. Welcome to the most complete cybersecurity, ethical hacking & penetration testing course — packed with real world techniques, tools, and hands on labs!.
Gumroad Cve 2025 47539 vulnerability intelligence. threat score 20 100. cvss, epss, exploit data, and threat analysis. Welcome to the most complete cybersecurity, ethical hacking & penetration testing course — packed with real world techniques, tools, and hands on labs!. Over 10,000 wordpress sites at risk from eventin plugin flaw cve 2025 47539. attackers can gain admin access via unauthenticated api exploit. A product incorrectly assigns a privilege to a particular actor, creating an unintended sphere of control for that actor. Below is the impact analysis for cve 2025 47539, showing how confidentiality, integrity, and availability might be affected if the vulnerability is exploited. An attacker can exploit this vulnerability to escalate privileges without requiring authentication, user interaction, or complex attack conditions. this could allow unauthorized access to sensitive functionality, data modification, and system compromise.

Jual Ec5 E Course Ethical Hacking Penetration Testing Bug Bounty Over 10,000 wordpress sites at risk from eventin plugin flaw cve 2025 47539. attackers can gain admin access via unauthenticated api exploit. A product incorrectly assigns a privilege to a particular actor, creating an unintended sphere of control for that actor. Below is the impact analysis for cve 2025 47539, showing how confidentiality, integrity, and availability might be affected if the vulnerability is exploited. An attacker can exploit this vulnerability to escalate privileges without requiring authentication, user interaction, or complex attack conditions. this could allow unauthorized access to sensitive functionality, data modification, and system compromise.
Cve 2025 24813 Exploit Cve 2025 24813 Exploit Py At Main Below is the impact analysis for cve 2025 47539, showing how confidentiality, integrity, and availability might be affected if the vulnerability is exploited. An attacker can exploit this vulnerability to escalate privileges without requiring authentication, user interaction, or complex attack conditions. this could allow unauthorized access to sensitive functionality, data modification, and system compromise.
Comments are closed.