Encryption Key Management

Key Management Pdf Key Cryptography Encryption Learn how microsoft 365 encrypts data at rest and in transit, securely manages encryption keys, and provides key management options to customers to meet their business needs and compliance obligations. Key management refers to the processes and procedures involved in generating, storing, distributing, and managing cryptographic keys used in cryptographic algorithms to protect sensitive data. it ensures that keys used to protect sensitive data are kept safe from unauthorized access or loss.

1 Keymanagement En Pdf Key Cryptography Cryptography Key management, or encryption key management, is the process of generating, exchanging, storing and managing cryptographic keys to ensure the security of encrypted data. it is crucial for effective data encryption, as poor key management can lead to unauthorized access, data loss and data breaches. Learn how to implement cryptographic key management within an application in a secure manner. this cheat sheet provides guidance for key selection, life cycle, storage, agreement and compromise. This article introduces 16 encryption key management best practices that enable you to stay in control of your cryptography strategy. implementing the measures below helps prevent data breaches, avoid fines, and ensure encryption remains safe and effective. Encryption key management is the practice of generating, organizing, protecting, storing, backing up and distributing encryption keys. high profile data losses and regulatory compliance requirements have caused a dramatic increase in the use of encryption to protect data in the enterprise.

Lecture 3 Key Management Download Free Pdf Key Cryptography This article introduces 16 encryption key management best practices that enable you to stay in control of your cryptography strategy. implementing the measures below helps prevent data breaches, avoid fines, and ensure encryption remains safe and effective. Encryption key management is the practice of generating, organizing, protecting, storing, backing up and distributing encryption keys. high profile data losses and regulatory compliance requirements have caused a dramatic increase in the use of encryption to protect data in the enterprise. Analogy: keys are like a vault key set and key management is the vault, locksmithing, and access log combined. formal: systematic control over cryptographic key material and associated policies for confidentiality, integrity, and availability. Learn encryption key management best practices to secure data, reduce breach risk, and ensure compliance across cloud and on prem systems. Key management involves separating keys from data for increased flexibility and security. you can have multiple keys for the same data, the same key for multiple files, key backup and recovery, and many more choices. Discover key management best practices to secure your organization's sensitive data. learn about the importance of key management, real world examples, best practices, solutions, and a checklist to fortify your cybersecurity foundation.
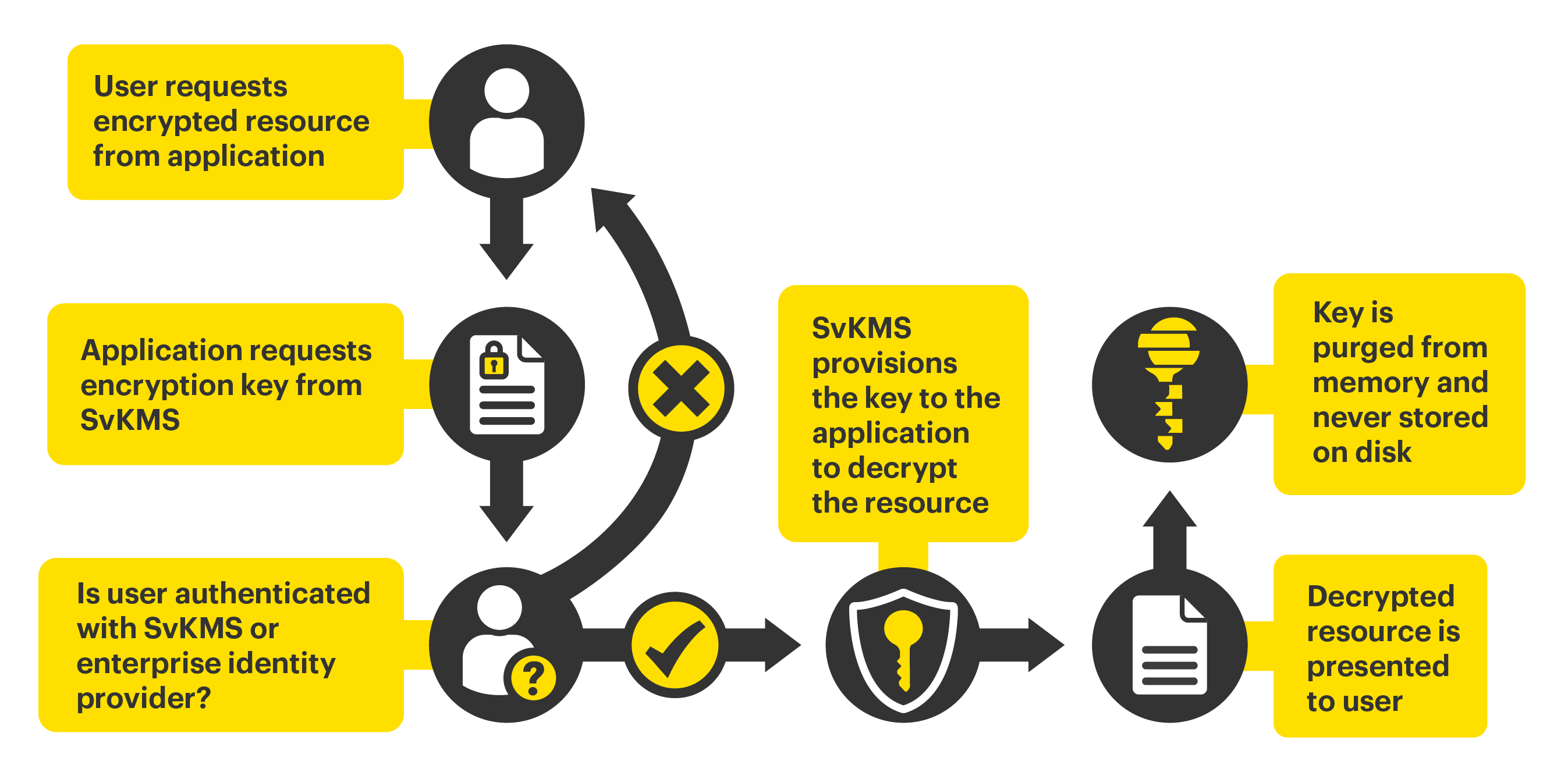
Encryption Key Management Svkms Stormagic Analogy: keys are like a vault key set and key management is the vault, locksmithing, and access log combined. formal: systematic control over cryptographic key material and associated policies for confidentiality, integrity, and availability. Learn encryption key management best practices to secure data, reduce breach risk, and ensure compliance across cloud and on prem systems. Key management involves separating keys from data for increased flexibility and security. you can have multiple keys for the same data, the same key for multiple files, key backup and recovery, and many more choices. Discover key management best practices to secure your organization's sensitive data. learn about the importance of key management, real world examples, best practices, solutions, and a checklist to fortify your cybersecurity foundation.
Comments are closed.