Encryption Key Management Simplified

Key Management Pdf Key Cryptography Encryption This article introduces 16 encryption key management best practices that enable you to stay in control of your cryptography strategy. implementing the measures below helps prevent data breaches, avoid fines, and ensure encryption remains safe and effective. Key management refers to the processes and procedures involved in generating, storing, distributing, and managing cryptographic keys used in cryptographic algorithms to protect sensitive data. it ensures that keys used to protect sensitive data are kept safe from unauthorized access or loss.
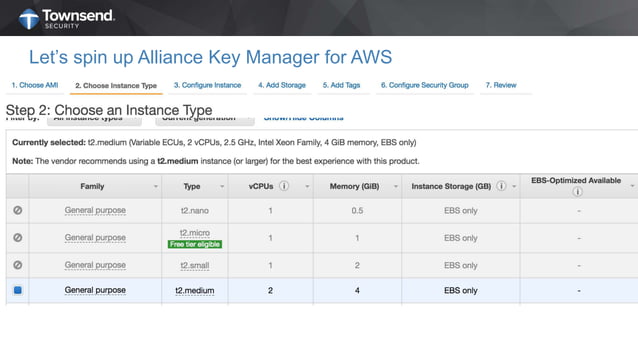
Simplified Encryption And Key Management Ppt In this video, we’ll discuss privacy, how encryption key management works, and its impact on data security. links & resources 👉 encryption key management:. This key management cheat sheet provides developers with guidance for implementation of cryptographic key management within an application in a secure manner. it is important to document and harmonize rules and practices for:. To ensure that your online data remains protected, it’s critical to understand the different components of encryption key management, so that you know the right questions to ask when evaluating new and existing encryption technologies. This article outlines technical best practices for managing symmetric encryption keys, including secure generation, storage, wrapping, rotation, and lifecycle management, aligned with nist guidance and real world implementation considerations.
Simplified Encryption And Key Management Ppt To ensure that your online data remains protected, it’s critical to understand the different components of encryption key management, so that you know the right questions to ask when evaluating new and existing encryption technologies. This article outlines technical best practices for managing symmetric encryption keys, including secure generation, storage, wrapping, rotation, and lifecycle management, aligned with nist guidance and real world implementation considerations. Key management, or encryption key management, is the process of generating, exchanging, storing and managing cryptographic keys to ensure the security of encrypted data. it is crucial for effective data encryption, as poor key management can lead to unauthorized access, data loss and data breaches. Encryption key management protects the lifecycle of these keys, ensuring their secure generation, storage, rotation, and retirement. this protects sensitive information from unauthorized access and helps software and systems maintain compliance with industry standards. Encryption key management operates through a systematic approach that governs cryptographic keys from creation to destruction. the process begins with secure key generation using hardware security modules (hsms) or software based random number generators that produce cryptographically strong keys. This document provides an overview of encryption key management. it discusses how encryption keys are the most important part of an encryption strategy and how key management hardware security modules are designed to create and manage encryption keys according to best practices.
Encryption Key Management A Beginner S Guide Stormagic Key management, or encryption key management, is the process of generating, exchanging, storing and managing cryptographic keys to ensure the security of encrypted data. it is crucial for effective data encryption, as poor key management can lead to unauthorized access, data loss and data breaches. Encryption key management protects the lifecycle of these keys, ensuring their secure generation, storage, rotation, and retirement. this protects sensitive information from unauthorized access and helps software and systems maintain compliance with industry standards. Encryption key management operates through a systematic approach that governs cryptographic keys from creation to destruction. the process begins with secure key generation using hardware security modules (hsms) or software based random number generators that produce cryptographically strong keys. This document provides an overview of encryption key management. it discusses how encryption keys are the most important part of an encryption strategy and how key management hardware security modules are designed to create and manage encryption keys according to best practices.
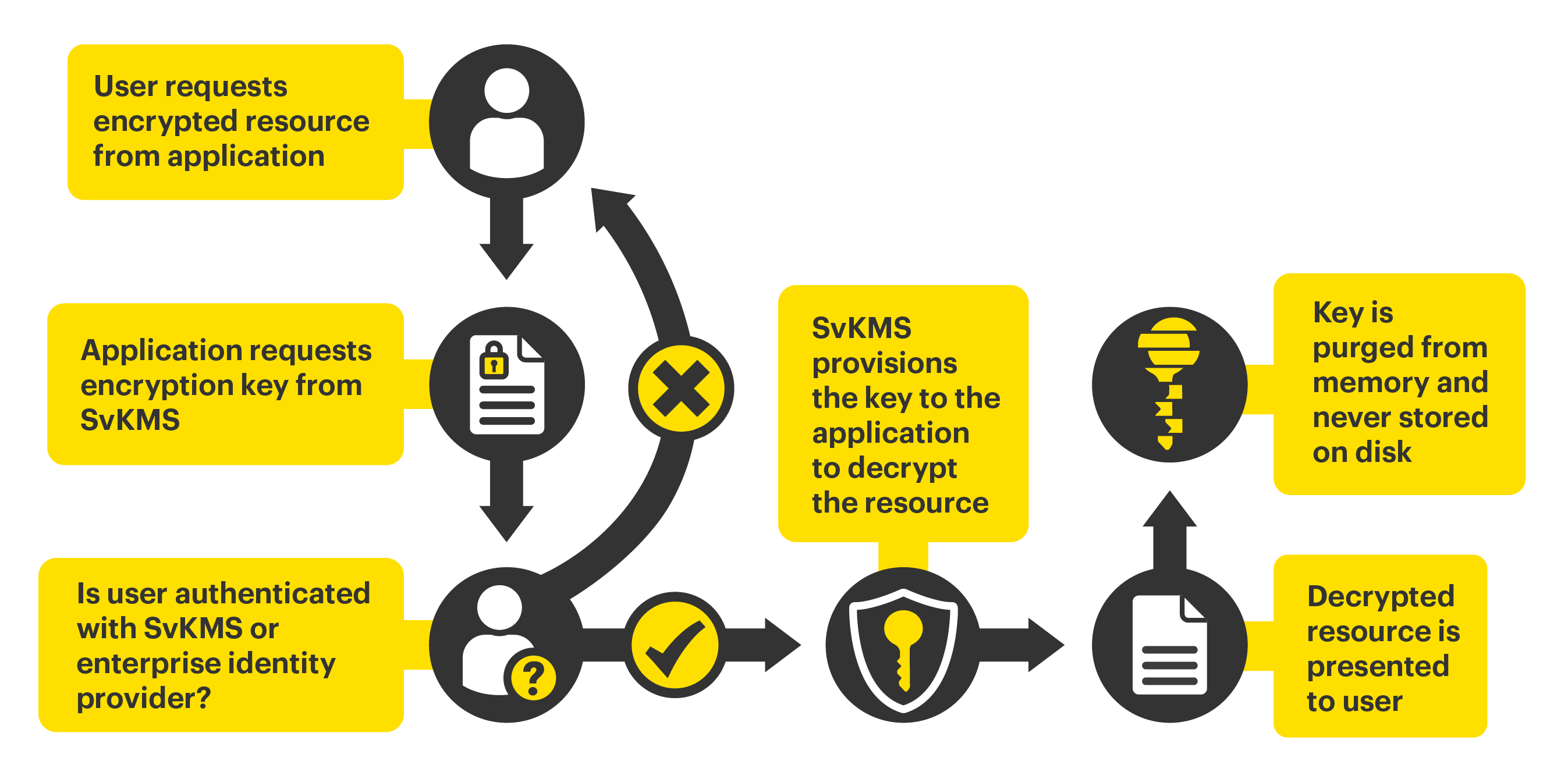
Encryption Key Management Svkms Stormagic Encryption key management operates through a systematic approach that governs cryptographic keys from creation to destruction. the process begins with secure key generation using hardware security modules (hsms) or software based random number generators that produce cryptographically strong keys. This document provides an overview of encryption key management. it discusses how encryption keys are the most important part of an encryption strategy and how key management hardware security modules are designed to create and manage encryption keys according to best practices.
Comments are closed.