Cyber Security You Are A Target
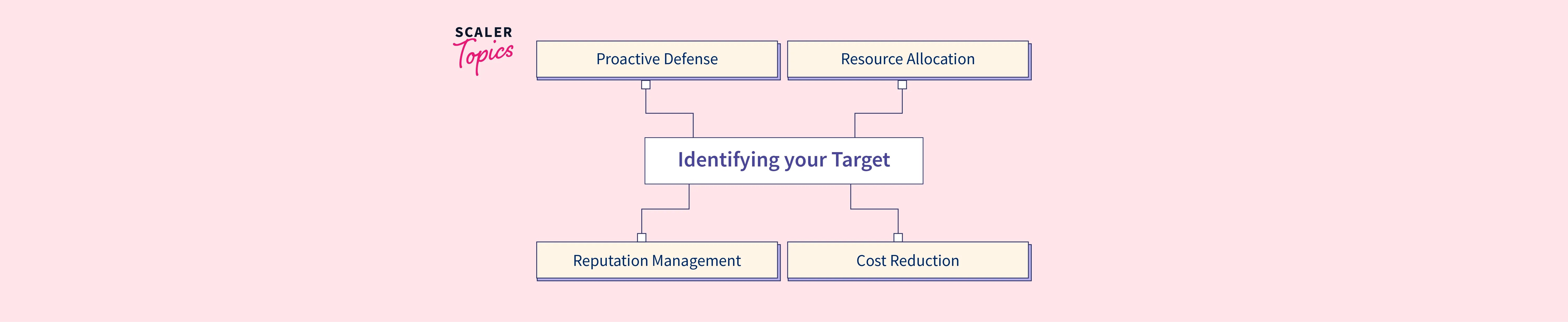
Cyber Security Target Identification Scaler Topics This course provides insights and practical steps so senior decision makers can create a business savvy cybersecurity program. Launched in 1989 as a cooperative for information security thought leadership, it is sans’ ongoing mission to empower cybersecurity professionals with the practical skills and knowledge they need to make our world a safer place.

Blog Who S The Target Audience For Cyber Security Nowcomms You are the target s no value. in reality, individuals like yourself are a cyber criminal’s primary target; you and your computer are attacke every day. the first step to protecting yourself is realizing you are under cons. Targeted attacks are like a carefully planned heist. attackers research their target, identify weaknesses, and use advanced techniques to achieve their specific goals, which often involve stealing sensitive data or causing significant disruption. Spotting malicious email messages (itsap.00.100) email is a convenient communication tool for individuals and organizations. it provides an easy way to exchange documents, images, links and various files. however, threat actors can use email for malicious purposes. they frequently target organizations and their networks to steal information. threat actors are technologically savvy, conscious. Cisa shares up to date information about high impact types of security activity affecting the community at large and in depth analysis on new and evolving cyber threats.

Are You An Easy Target Cybersecurity For Small Businesses Spotting malicious email messages (itsap.00.100) email is a convenient communication tool for individuals and organizations. it provides an easy way to exchange documents, images, links and various files. however, threat actors can use email for malicious purposes. they frequently target organizations and their networks to steal information. threat actors are technologically savvy, conscious. Cisa shares up to date information about high impact types of security activity affecting the community at large and in depth analysis on new and evolving cyber threats. Once you become a target of a phishing attack, you might remain a target indefinitely. for corporations and government agencies, the persistence of contact information in phishing databases adds an extra layer of danger. Everyone is going to be a target of cyber attacks and needs to know how to be protected online. online danger provides valuable tips and tricks to keep you safe and secure online. You are a target t cybersecurity. each week in october, we will provide information and tips on protecting yourself t work and home. our goal is to help you make the most of today’s technology saf yone's business. we are sharing the you are a target poster. this poster identifies and explains different ways cybercriminals can make money from a. Understanding the psychological drivers of cybercrime and the factors that enable it is essential for crafting prevention strategies that target these root causes.

Effective Cybersecurity Starts With Seeing Yourself As A Target Once you become a target of a phishing attack, you might remain a target indefinitely. for corporations and government agencies, the persistence of contact information in phishing databases adds an extra layer of danger. Everyone is going to be a target of cyber attacks and needs to know how to be protected online. online danger provides valuable tips and tricks to keep you safe and secure online. You are a target t cybersecurity. each week in october, we will provide information and tips on protecting yourself t work and home. our goal is to help you make the most of today’s technology saf yone's business. we are sharing the you are a target poster. this poster identifies and explains different ways cybercriminals can make money from a. Understanding the psychological drivers of cybercrime and the factors that enable it is essential for crafting prevention strategies that target these root causes.

Who Is The Target Audience For Cybersecurity You are a target t cybersecurity. each week in october, we will provide information and tips on protecting yourself t work and home. our goal is to help you make the most of today’s technology saf yone's business. we are sharing the you are a target poster. this poster identifies and explains different ways cybercriminals can make money from a. Understanding the psychological drivers of cybercrime and the factors that enable it is essential for crafting prevention strategies that target these root causes.

Cybersecurity Myth Busted We Re Not A Target
Comments are closed.