Cyber Attack Explained Target 2013

Attack Pdf Security Computer Security The target breach demonstrated the vulnerabilities in corporate systems and raised questions about the preparedness of businesses to handle large scale cyberattacks. in this blog post, we will explore the target data breach in detail, discussing its timeline, causes, impact, and the lessons learned from this monumental cybersecurity failure. Learn what happened in the target data breach — when it occurred, what data was exposed, who was affected, and key lessons learned.

Target 2013 Holiday Data Breach Cyber Attack Astern europe. this report presents an explanation of how the target breach occurred, based on media reports and expert analyses that have been published since target publicly acknowledged this breach on. This case study will first consider target’s vulnerabilities to an external attack in 2013 and explain how the attackers stole the data. second, this case study will discuss the importance of corporate responses to data breaches when they do happen, using target as an example. What happened in the target data breach? the target data breach of 2013 remains one of the most studied cyberattacks in retail history. a company with a $1.6 billion it budget and security tools from fireeye got breached through an hvac vendor’s stolen password. Hackers stole 40 million credit cards through an hvac vendor. the target breach changed cybersecurity forever — here's the full breakdown and key lessons.

Target Data Breach Lessons Learned From 2013 Attack Course Hero What happened in the target data breach? the target data breach of 2013 remains one of the most studied cyberattacks in retail history. a company with a $1.6 billion it budget and security tools from fireeye got breached through an hvac vendor’s stolen password. Hackers stole 40 million credit cards through an hvac vendor. the target breach changed cybersecurity forever — here's the full breakdown and key lessons. Target was required to pay an $18.5 million settlement after hackers stole 40 million credit and debit records. but as with many unprecedented security attacks, target’s data breach came with both warnings and lessons — which are still valid today. To a server in eastern europe. this report presents an explanation of how the target breach occurred, based on media reports and expert analyses that have been published since target publicly acknow. Abstract—this paper investigates and examines the events leading up to the second most devastating data breach in history: the attack on the target corporation. it includes a thorough step by step analysis of this attack and a comprehensive anatomy of the malware named blackpos. In 2013 a single overlooked email resulted in a data breach at target, stealing the data of up to one hundred and ten million customers. a simple attack — targeting not target itself, but a small heating and air conditioning company in pennsylvania.

Target Cyber Attack Key Lessons For Cybersecurity Target was required to pay an $18.5 million settlement after hackers stole 40 million credit and debit records. but as with many unprecedented security attacks, target’s data breach came with both warnings and lessons — which are still valid today. To a server in eastern europe. this report presents an explanation of how the target breach occurred, based on media reports and expert analyses that have been published since target publicly acknow. Abstract—this paper investigates and examines the events leading up to the second most devastating data breach in history: the attack on the target corporation. it includes a thorough step by step analysis of this attack and a comprehensive anatomy of the malware named blackpos. In 2013 a single overlooked email resulted in a data breach at target, stealing the data of up to one hundred and ten million customers. a simple attack — targeting not target itself, but a small heating and air conditioning company in pennsylvania.
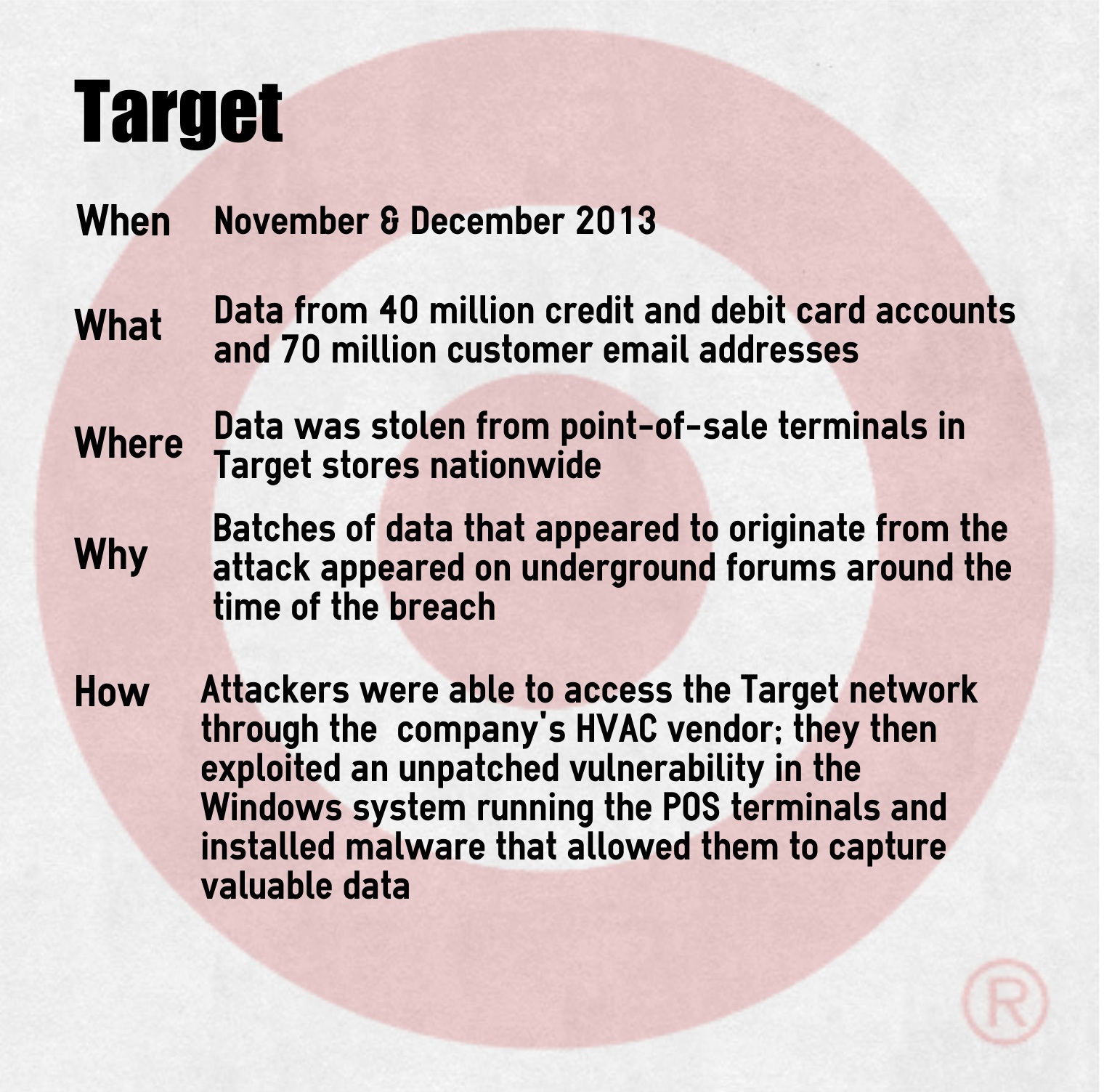
Targetdatabreach2013 Workflow Studios Abstract—this paper investigates and examines the events leading up to the second most devastating data breach in history: the attack on the target corporation. it includes a thorough step by step analysis of this attack and a comprehensive anatomy of the malware named blackpos. In 2013 a single overlooked email resulted in a data breach at target, stealing the data of up to one hundred and ten million customers. a simple attack — targeting not target itself, but a small heating and air conditioning company in pennsylvania.

The Complete Guide To Understanding Cyber Attacks Cyber Command
Comments are closed.