Cyber Security Framework Mercury It

Cyber Security Framework Mercury It Email * message * submit mercury it we help organisations of all sizes manage their it support services, it infrastructure, telecommunications, and software development needs. locations auckland. The framework is mandatory for australian federal government agencies under the protective security policy framework (pspf) and is now considered best practice for all australian organisations. mercury it specialises in essential eight implementation and assessment.
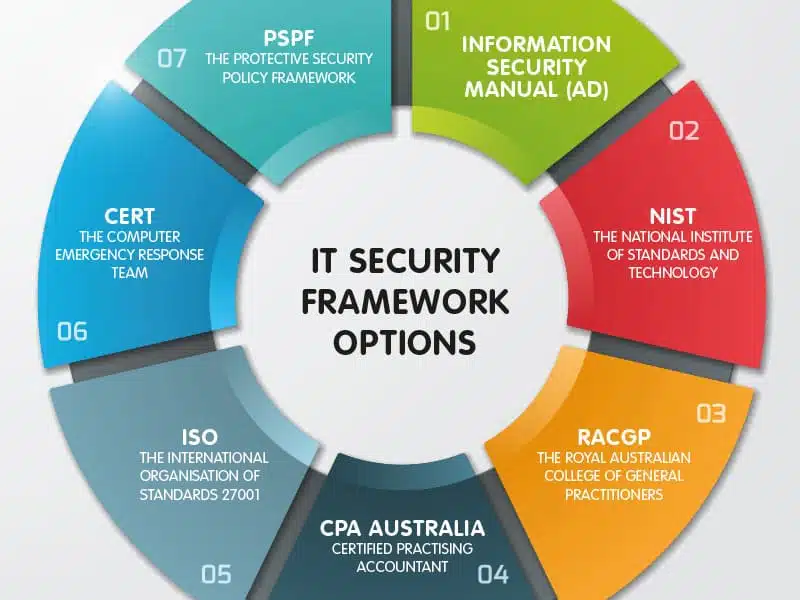
The 7 Most Common It Security Framework Options In Australia Stanfield It For organizations seeking a reliable, standards based foundation for secure physical access, mercury mp controllers offer the architectural depth, integration flexibility and cybersecurity rigor necessary to support evolving enterprise environments. We can develop or modify detailed information security procedures that support policy requirements, and align these procedures to a specific security control framework so you can ensure that all required controls are supported by both procedure and policy level documentation. A cybersecurity framework is a documented set of policies, processes, and controls, both technical and organizational, designed to manage cyber risk and protect sensitive data. think of it as a blueprint that describes “what good looks like” for security without mandating specific tools or vendors. popular frameworks like the nist cybersecurity framework, iso iec 27001, and cis critical. Learn about the top it security frameworks and standards available and get advice on choosing the ones that will help protect your company's data.

Cyber Security Framework Pacom A cybersecurity framework is a documented set of policies, processes, and controls, both technical and organizational, designed to manage cyber risk and protect sensitive data. think of it as a blueprint that describes “what good looks like” for security without mandating specific tools or vendors. popular frameworks like the nist cybersecurity framework, iso iec 27001, and cis critical. Learn about the top it security frameworks and standards available and get advice on choosing the ones that will help protect your company's data. In this article, we aim to demystify cybersecurity frameworks, offering insights into their importance, the various frameworks available, and the benefits they bring to organizations. cybersecurity frameworks are structured guidelines designed to manage and mitigate cyber risks systematically. In this article, we will dive deep into the main concepts and share some cybersecurity framework examples. Explore the top cybersecurity frameworks for risk management and compliance. find a list of the best cybersecurity frameworks for your business in 2025. The mercury it set of cybersecurity products includes extended detection and response (xdr), url filtering, darkweb monitoring, siem, patch management, secops and application control.

Top 6 Cybersecurity Frameworks For Your Business Sprinto In this article, we aim to demystify cybersecurity frameworks, offering insights into their importance, the various frameworks available, and the benefits they bring to organizations. cybersecurity frameworks are structured guidelines designed to manage and mitigate cyber risks systematically. In this article, we will dive deep into the main concepts and share some cybersecurity framework examples. Explore the top cybersecurity frameworks for risk management and compliance. find a list of the best cybersecurity frameworks for your business in 2025. The mercury it set of cybersecurity products includes extended detection and response (xdr), url filtering, darkweb monitoring, siem, patch management, secops and application control.
Comments are closed.