Cybersecurity Framework Guide To Types Components Of Cybersecurity

Components Of Cybersecurity Framework Pdf Computer Security Security This draft explains how to find, filter, and apply informative references using nist tools. review and submit comments here. the final version of nist cybersecurity framework 2.0: cybersecurity, enterprise risk management, and workforce management quick start guide. This has been a guide to cybersecurity framework. here we discuss the introduction, types, and various components of a cybersecurity framework and how to implement it.
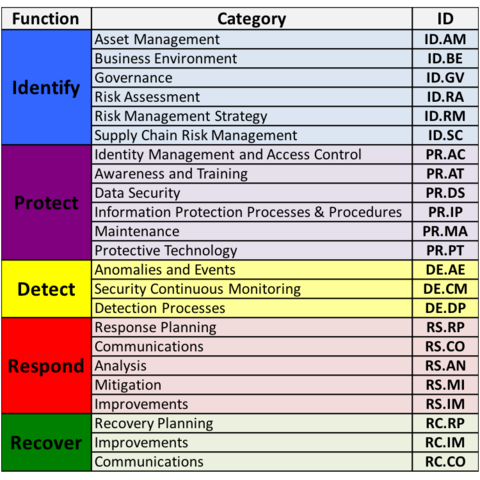
Cybersecurity Framework 1 1 Components Nist There are three main components of cyber security frameworks —framework core, implementation tiers, and profiles. framework core: in addition to an association’s current cybersecurity framework and risk management processes, the core guides oversee and reduce the vulnerabilities to cybersecurity. Master the nist csf 2.0 with this comprehensive guide covering all 6 functions, 22 categories, and 106 subcategories. perfect for cybersecurity professionals starting their journey with this essential framework. The framework describes a set of security outcomes to achieve and breaks those into three levels of increasing detail: functions, categories, and subcategories. Discover essential insights on cybersecurity frameworks: definitions, types, implementation, and best practices for robust security.
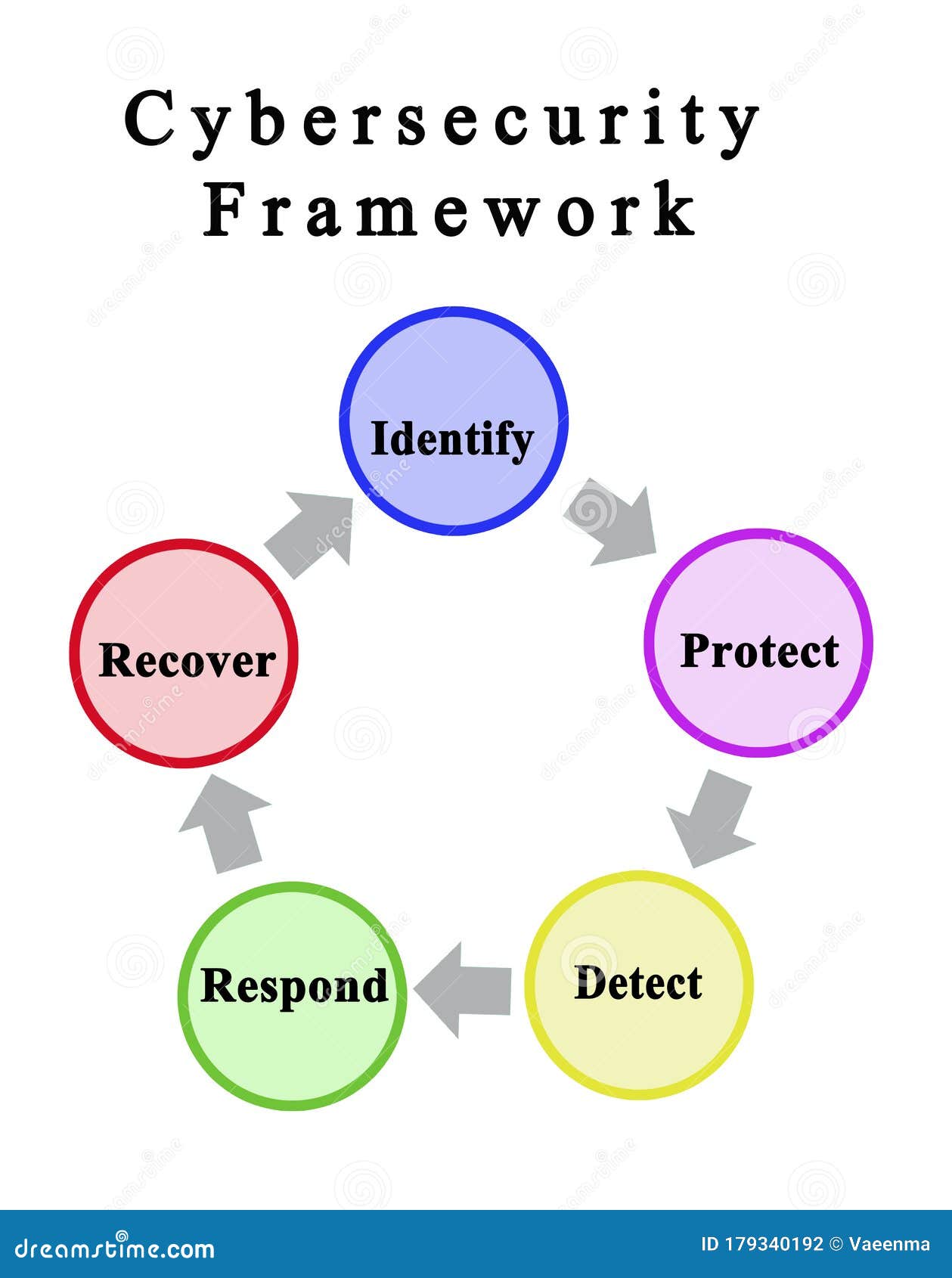
Components Of Cybersecurity Framework Stock Illustration Illustration The framework describes a set of security outcomes to achieve and breaks those into three levels of increasing detail: functions, categories, and subcategories. Discover essential insights on cybersecurity frameworks: definitions, types, implementation, and best practices for robust security. At its core, the nist cybersecurity framework 2.0 provides a taxonomy of high level cybersecurity outcomes — not a checklist of specific controls or technologies, but a structured way to think about what your organization needs to achieve. The nist cybersecurity framework provides organizations with a proven, flexible approach to building and managing cybersecurity programs that align with business objectives while effectively managing risk. The framework core is a structured set of cybersecurity functions, categories, and subcategories that help organizations assess and improve their cybersecurity practices by providing a standardized, risk based approach. This comprehensive guide covers everything you need to know about the nist cybersecurity framework, from understanding its core components to implementing a robust cybersecurity program that aligns with industry best practices and regulatory requirements.
Five Components Of Cybersecurity Framework Stock Photo Alamy At its core, the nist cybersecurity framework 2.0 provides a taxonomy of high level cybersecurity outcomes — not a checklist of specific controls or technologies, but a structured way to think about what your organization needs to achieve. The nist cybersecurity framework provides organizations with a proven, flexible approach to building and managing cybersecurity programs that align with business objectives while effectively managing risk. The framework core is a structured set of cybersecurity functions, categories, and subcategories that help organizations assess and improve their cybersecurity practices by providing a standardized, risk based approach. This comprehensive guide covers everything you need to know about the nist cybersecurity framework, from understanding its core components to implementing a robust cybersecurity program that aligns with industry best practices and regulatory requirements.
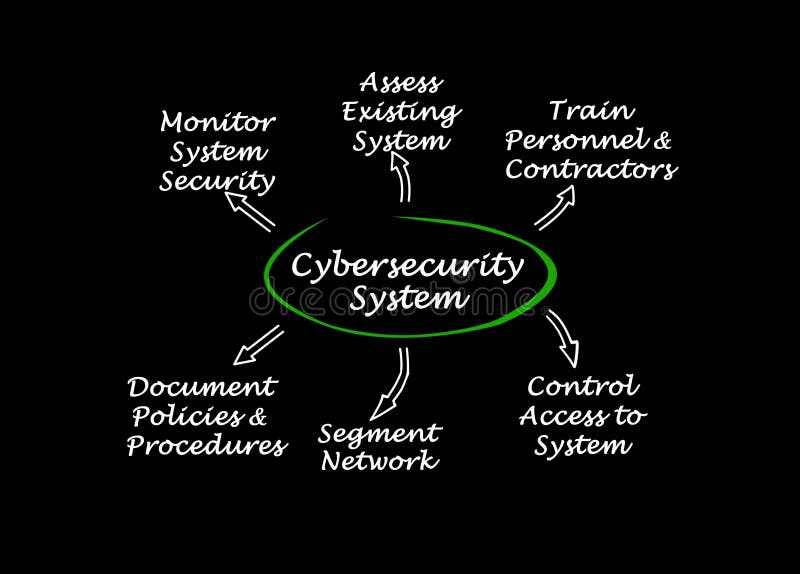
Components Of Cybersecurity Framework Stock Illustration Illustration The framework core is a structured set of cybersecurity functions, categories, and subcategories that help organizations assess and improve their cybersecurity practices by providing a standardized, risk based approach. This comprehensive guide covers everything you need to know about the nist cybersecurity framework, from understanding its core components to implementing a robust cybersecurity program that aligns with industry best practices and regulatory requirements.
Comments are closed.