Cryptography File Integrity

Integrity And Security Pdf Public Key Cryptography Encryption By creating and maintaining cryptographic hashes for files, a file integrity checker (fic) protects data security and enables users to identify changes through verification checks. the goal of this project is to create an automated integrity monitoring system using a python based fic. Learn how cryptographic hash functions create digital fingerprints for files, enabling you to detect corruption and verify authenticity through checksum verification.

Cryptography Counters File Integrity Attacks Fiwork File integrity monitoring (fim) is a security process that continuously monitors and analyzes the integrity of an organization's assets by comparing them against a trusted baseline to detect unauthorized changes or suspicious activity. These cryptographic functions, including md5, sha, and crc32, help create a unique fingerprint for each file, which you can then verify against a known value to establish file integrity. This guide shows practical, no‑nonsense ways to verify file integrity, from quick checks you can do today to cryptographic hashes you can automate. it works across macos, windows, and linux, and pairs perfectly with privacy controls in comfyfile. Explore the fundamental concepts and techniques that ensure data integrity in cryptography, including methods and best practices.
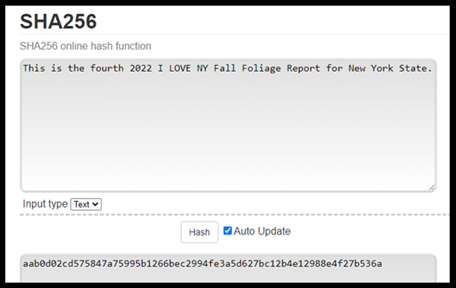
Cryptography Counters File Integrity Attacks Fiwork This guide shows practical, no‑nonsense ways to verify file integrity, from quick checks you can do today to cryptographic hashes you can automate. it works across macos, windows, and linux, and pairs perfectly with privacy controls in comfyfile. Explore the fundamental concepts and techniques that ensure data integrity in cryptography, including methods and best practices. Hashdeep is a versatile and powerful tool for file integrity checking and digital forensics. its support for multiple hash algorithms, recursive directory hashing, and file comparison make it an indispensable utility for anyone working in security, forensics, or system administration. A comprehensive python based system for ensuring file integrity using sha 256 sha 3 hashing algorithms, merkle trees, and real time alerting mechanisms. In an era where data breaches and cyber threats are becoming increasingly sophisticated, cryptographic integrity has emerged as a cornerstone of modern security practices. it ensures that data remains unaltered, authentic, and secure during transmission and storage. To verify file integrity, organizations utilize file integrity monitoring (fim) tools that employ checksums or cryptographic hashes to assess the integrity of files.
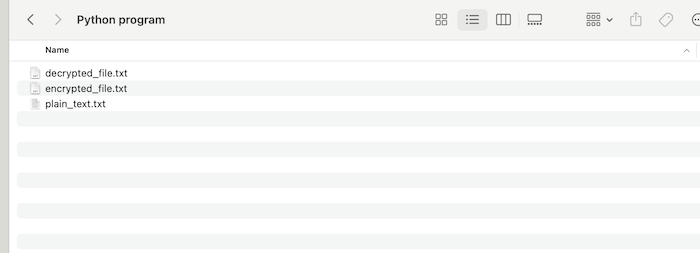
Cryptography File Hashdeep is a versatile and powerful tool for file integrity checking and digital forensics. its support for multiple hash algorithms, recursive directory hashing, and file comparison make it an indispensable utility for anyone working in security, forensics, or system administration. A comprehensive python based system for ensuring file integrity using sha 256 sha 3 hashing algorithms, merkle trees, and real time alerting mechanisms. In an era where data breaches and cyber threats are becoming increasingly sophisticated, cryptographic integrity has emerged as a cornerstone of modern security practices. it ensures that data remains unaltered, authentic, and secure during transmission and storage. To verify file integrity, organizations utilize file integrity monitoring (fim) tools that employ checksums or cryptographic hashes to assess the integrity of files.

File Integrity Monitoring Sashank Dara In an era where data breaches and cyber threats are becoming increasingly sophisticated, cryptographic integrity has emerged as a cornerstone of modern security practices. it ensures that data remains unaltered, authentic, and secure during transmission and storage. To verify file integrity, organizations utilize file integrity monitoring (fim) tools that employ checksums or cryptographic hashes to assess the integrity of files.
Comments are closed.