Cryptography Counters File Integrity Attacks Fiwork

Cryptography Counters File Integrity Attacks Fiwork In the previous article we summarized the vulnerabilities that can affect the computing infrastructure. for educational purposes, we have grouped these generic vulnerabilities into three: integrity. confidentiality. authenticity. in this second article we will explain what tools cryptogr. Various verified cyberattacks that were executed against cis in recent years are analyzed. moreover, the general framework of cis is demonstrated together with the employed technologies and cryptographic primitives.
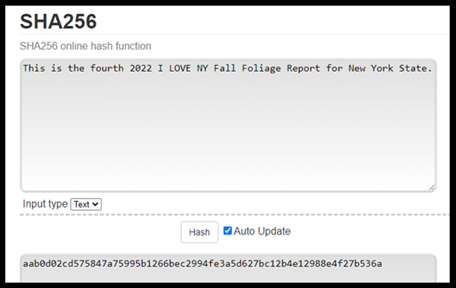
Cryptography Counters File Integrity Attacks Fiwork Cryptography and network security are essential for protecting information systems from unauthorized access, ensuring secure communication, and maintaining trust in today’s digital world. A hash function creates a unique digital fingerprint (a fixed length string of characters) for a file. even a one bit change in the file will produce a completely different hash, making it an excellent tool for detecting tampering. We introduce an algorithm agnostic solution that provides both data integrity and con dentiality protection at the disk sector layer. our open source solution is intended for drives without any special hardware extensions and is based on per sector metadata elds implemented in software. This paper describes the design and implementation of a new real time file integrity monitoring system, named websguard. it is a client server system intended for windows based environments.

Mitigating Software Integrity Attacks With Trusted Pdf Key We introduce an algorithm agnostic solution that provides both data integrity and con dentiality protection at the disk sector layer. our open source solution is intended for drives without any special hardware extensions and is based on per sector metadata elds implemented in software. This paper describes the design and implementation of a new real time file integrity monitoring system, named websguard. it is a client server system intended for windows based environments. Effective cyber defense enables organizations to anticipate, withstand, and recover from cyber attacks through proactive monitoring, threat detection, and incident response. it combines security operations, automation, and resilient architecture to reduce risk and minimize attack impact. Learn about tracking file change with file integrity monitoring in microsoft defender for cloud. Cryptography attacks are on the rise and becoming more sophisticated. in this blog post, we'll take a look at some of the most common types of cryptography attacks and how to defend against them. In this article, we’ll explore six popular categories of cryptography attacks, investigate how they happen, and offer practical preventative strategies to strengthen your online defenses.

Cryptography And Network Security Pdf Effective cyber defense enables organizations to anticipate, withstand, and recover from cyber attacks through proactive monitoring, threat detection, and incident response. it combines security operations, automation, and resilient architecture to reduce risk and minimize attack impact. Learn about tracking file change with file integrity monitoring in microsoft defender for cloud. Cryptography attacks are on the rise and becoming more sophisticated. in this blog post, we'll take a look at some of the most common types of cryptography attacks and how to defend against them. In this article, we’ll explore six popular categories of cryptography attacks, investigate how they happen, and offer practical preventative strategies to strengthen your online defenses.
Comments are closed.