Crypto Qb Pdf Cryptography Cipher

Crypto Qb Pdf Cryptography Cipher Crypto qb free download as pdf file (.pdf), text file (.txt) or read online for free. this document discusses modern cryptography and steganography. Convention: alicekazam is sending encrypted messages to bobasaur, bobasaur is decrypting them, and eevee is an eavesdropper who overhears everything being sent, but hopefully still can’t understand it. an encryption method together with a decryption method is known as a cryptographic scheme.
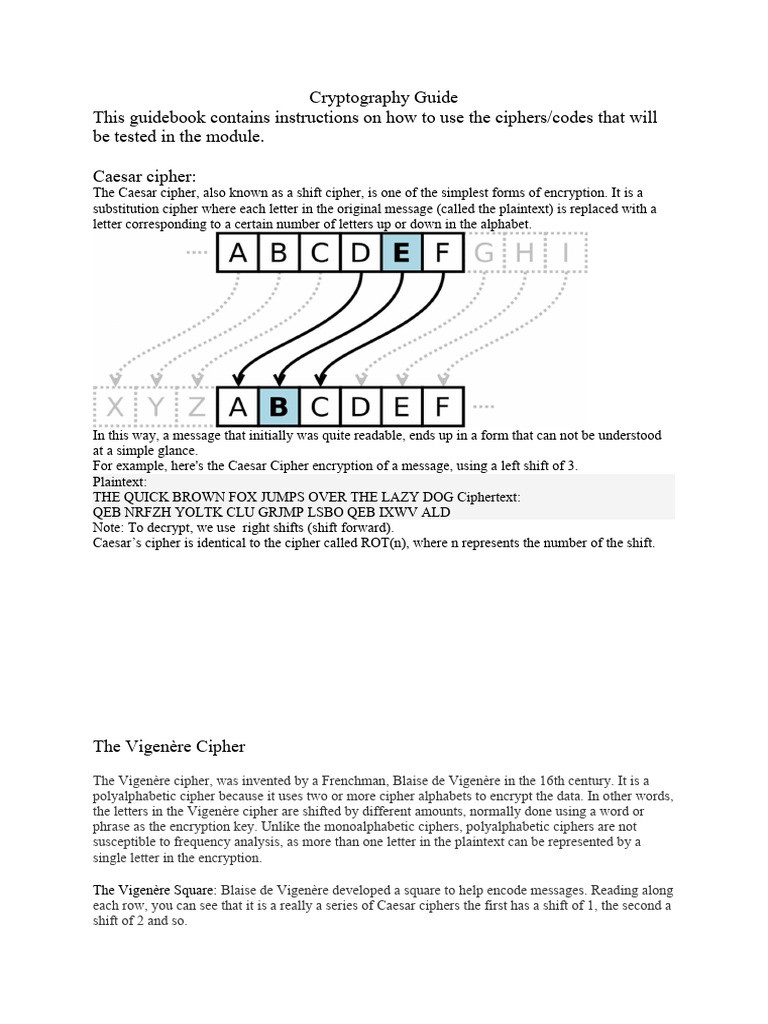
Cryptography Guide Pdf Cipher Cryptography Course objectives: learn to analyze the security of in built cryptosystems. know the fundamental mathematical concepts related to security. develop cryptographic algorithms for information security. of data integrity and authentication schem understand cyber crimes and cyber security. unit i introduction to security 9. Our book provides the reader with a deep understanding of how modern cryp tographic schemes work. we introduce the necessary mathematical concepts in a way that is accessible for every reader with a minimum background in college level calculus. It presents in a coherent manner most of the important cryptographic tools one needs to implement secure cryptographic systems, and explains many of the cryptographic principles and protocols of existing systems. We shall only be using these general forms of finite fields when discussing the rijndael block cipher, stream ciphers based on linear feedback shift registers and when we look at elliptic curve based systems.

Quantum Cryptography Pdf Cryptography Cyberwarfare It presents in a coherent manner most of the important cryptographic tools one needs to implement secure cryptographic systems, and explains many of the cryptographic principles and protocols of existing systems. We shall only be using these general forms of finite fields when discussing the rijndael block cipher, stream ciphers based on linear feedback shift registers and when we look at elliptic curve based systems. 1. compare stream cipher with block cipher with example. ses the input stream co tinuously and producing one element at a time. example: caeser cipher. block cipher: processes the input one bloc of elements t time producing an output block for each input block. example: des. 2. differentiate unconditionally secured and computationally secured . Ptographic keys are exchanged between two parties, allowing use of a cryptographic algorithm. if sender and receiver wish to exchange encrypted messages, each must be equipped to encrypt messages to be sent and decrypt messages received. The following pages contain solutions to core problems from exams in cryptography given at the faculty of mathematics, natural sciences and information technologies at the university of primorska. After all, given this subtlety, a single course in cryptography is no guarantee of using (let alone inventing) crypto correctly. in my view, regardless of its immense and growing practical importance, cryptography is worth studying for its intellectual content.

Quantum Cryptography A Review Pdf Cryptography Key Cryptography 1. compare stream cipher with block cipher with example. ses the input stream co tinuously and producing one element at a time. example: caeser cipher. block cipher: processes the input one bloc of elements t time producing an output block for each input block. example: des. 2. differentiate unconditionally secured and computationally secured . Ptographic keys are exchanged between two parties, allowing use of a cryptographic algorithm. if sender and receiver wish to exchange encrypted messages, each must be equipped to encrypt messages to be sent and decrypt messages received. The following pages contain solutions to core problems from exams in cryptography given at the faculty of mathematics, natural sciences and information technologies at the university of primorska. After all, given this subtlety, a single course in cryptography is no guarantee of using (let alone inventing) crypto correctly. in my view, regardless of its immense and growing practical importance, cryptography is worth studying for its intellectual content.

Ch 02 Basics Of Cryptography Download Free Pdf Cipher Computer The following pages contain solutions to core problems from exams in cryptography given at the faculty of mathematics, natural sciences and information technologies at the university of primorska. After all, given this subtlety, a single course in cryptography is no guarantee of using (let alone inventing) crypto correctly. in my view, regardless of its immense and growing practical importance, cryptography is worth studying for its intellectual content.
Comments are closed.