Ch03 Crypto7e Pdf Cryptography Cipher

Cipher Pdf Cryptography Secure Communication Ch03 crypto7e free download as pdf file (.pdf), text file (.txt) or view presentation slides online. Vigenère cipher • best known and one of the simplest polyalphabetic substitution ciphers • in this scheme the set of related monoalphabetic substitution rules consists of the 26 caesar ciphers with shifts of 0 through 25.
Ch 2 Cryptography Pdf Cryptography Cryptanalysis Ieee technical committee on security and privacy: home of the electronic newsletter cipher, which provides book reviews, new crypto and security links, and links to reports and papers available online. The document discusses various polyalphabetic ciphers including the vigenere cipher, one time pad cipher, playfair cipher, and hill cipher. it provides examples of encrypting and decrypting messages with the vigenere cipher and playfair cipher. Helpful and available for students of seu monash in suzhou seu monash 2017 2018 the 3rd semester fit5191 network protocols and network security exam solutions crypto7e 1 10.pdf at master · nonoking seu monash 2017 2018. A. it provides the time duration that the certificate will be acceptable. 3.if the user’s file encryption key has been updated, you can use the cipher command with the option to update files that have been encrypted with the previous key.

Q07 Cipher Algorithm 40 Marks Pdf Encryption String Computer Helpful and available for students of seu monash in suzhou seu monash 2017 2018 the 3rd semester fit5191 network protocols and network security exam solutions crypto7e 1 10.pdf at master · nonoking seu monash 2017 2018. A. it provides the time duration that the certificate will be acceptable. 3.if the user’s file encryption key has been updated, you can use the cipher command with the option to update files that have been encrypted with the previous key. You have found an old ciphertext, where you know that the plaintext discusses cryptographic methods. you suspect that a vigenere cipher has been used and therefore look for repeated strings in the ciphertext. This textbook places greater emphasis on computer security issues as opposed to cryptography and network security issues. for instructors and students, there is a technical resource and course page to supplement the book. Ch03 crypto7e free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. computer network & security chapter 3. Ch03 crypto7e free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online.

Cryptographyand Information Security Third Edition Pdf You have found an old ciphertext, where you know that the plaintext discusses cryptographic methods. you suspect that a vigenere cipher has been used and therefore look for repeated strings in the ciphertext. This textbook places greater emphasis on computer security issues as opposed to cryptography and network security issues. for instructors and students, there is a technical resource and course page to supplement the book. Ch03 crypto7e free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. computer network & security chapter 3. Ch03 crypto7e free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online.

Cryptography Chapter1 Pdf Ch03 crypto7e free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. computer network & security chapter 3. Ch03 crypto7e free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online.
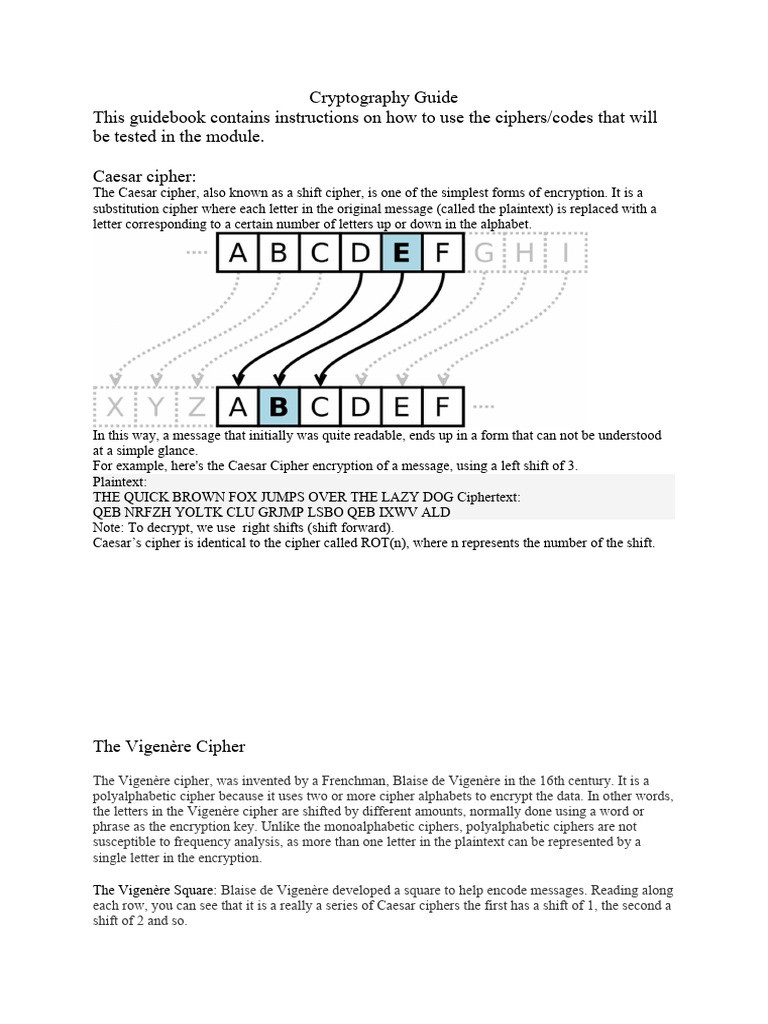
Cryptography Guide Pdf Cipher Cryptography
Comments are closed.