Cryptanalytic Timing Attacks 1 Ppt
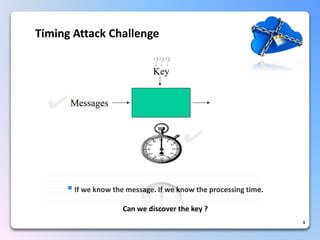
Cryptanalytic Timing Attacks 1 Ppt Don't worry, we will help you get to the right place. are you looking for:. Timing attacks: expose private information, such as rsa keys, by measuring the amount of time required to perform private key operations (decryptions).

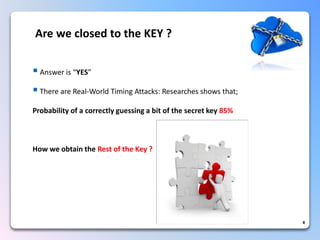
Cryptanalytic Timing Attacks 1 Ppt Exploiting openssl’s timing vulnerability: one process can extract keys from another. insecure vm can attack secure vm. breaks vm isolation. extract web server key remotely. our attack works across stanford campus. why are timing attacks against openssl interesting?. This document discusses timing attacks on rsa implementations. it begins with an overview of timing attacks and how they can expose private keys by measuring the time required for private key operations like decryption. Difference in decryption times between g and ghi will be small difference in decryption times between g and ghi will be large slide * timing attack details what is “large” and “small”?. Queries 17 real world attack (1 2) discuss an attack on ssl applications such as an apache web server with mod ssl. during the handshake, ssl server performs rsa decryption of client key exchange message (sent by client) using its private key. the goal is getting this key. after decryption, the server checks pkcs 1 padded.

Cryptanalytic Timing Attacks 1 Ppt Difference in decryption times between g and ghi will be small difference in decryption times between g and ghi will be large slide * timing attack details what is “large” and “small”?. Queries 17 real world attack (1 2) discuss an attack on ssl applications such as an apache web server with mod ssl. during the handshake, ssl server performs rsa decryption of client key exchange message (sent by client) using its private key. the goal is getting this key. after decryption, the server checks pkcs 1 padded. Attack attempts to “brute force” its way through the problem space to a solution. systematically check each and every possible key, encryption method, etc. until the correct one is found. Outline of kocher’s attack • idea: guess some bits of the exponent and predict how long decryption will take • if guess is correct, will observe correlation; if incorrect, then prediction will look random • this is a signal detection problem, where signal is timing variation due to guessed exponent bits • the more bits you already. This template helps you present information on seven stages. you can also present information on timing attacks, metadata security, information leakage, cryptographic vulnerabilities using this ppt design. this layout is completely editable so personalize it now to meet your audiences expectations. Contemporary cryptanalysis surprising attacks in unexpected places usually highly effective and hard to detect techniques. side channels underestimation of the physical nature of cryptographic devices. science leaps underestimation of the heuristic nature of cryptographic algorithms. social engineering underestimation of the human factor.
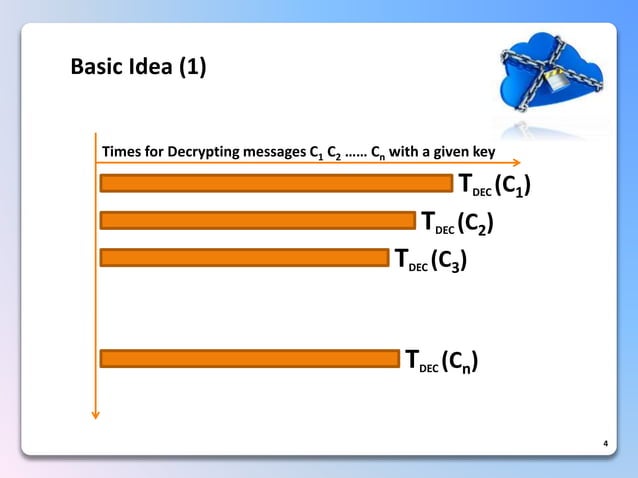
Cryptanalytic Timing Attacks 1 Ppt Attack attempts to “brute force” its way through the problem space to a solution. systematically check each and every possible key, encryption method, etc. until the correct one is found. Outline of kocher’s attack • idea: guess some bits of the exponent and predict how long decryption will take • if guess is correct, will observe correlation; if incorrect, then prediction will look random • this is a signal detection problem, where signal is timing variation due to guessed exponent bits • the more bits you already. This template helps you present information on seven stages. you can also present information on timing attacks, metadata security, information leakage, cryptographic vulnerabilities using this ppt design. this layout is completely editable so personalize it now to meet your audiences expectations. Contemporary cryptanalysis surprising attacks in unexpected places usually highly effective and hard to detect techniques. side channels underestimation of the physical nature of cryptographic devices. science leaps underestimation of the heuristic nature of cryptographic algorithms. social engineering underestimation of the human factor.
Cryptanalytic Timing Attacks 1 Ppt This template helps you present information on seven stages. you can also present information on timing attacks, metadata security, information leakage, cryptographic vulnerabilities using this ppt design. this layout is completely editable so personalize it now to meet your audiences expectations. Contemporary cryptanalysis surprising attacks in unexpected places usually highly effective and hard to detect techniques. side channels underestimation of the physical nature of cryptographic devices. science leaps underestimation of the heuristic nature of cryptographic algorithms. social engineering underestimation of the human factor.
Cryptanalytic Timing Attacks 1 Ppt
Comments are closed.