Timing Attack
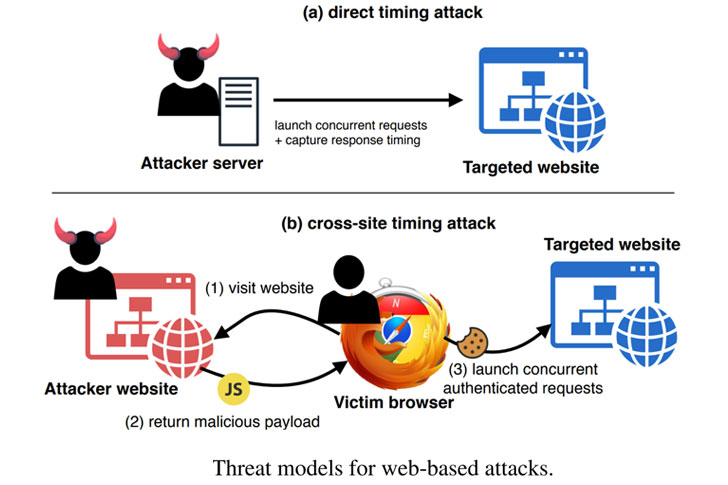
New Attack Leverages Http 2 For Effective Remote Timing Side Channel In cryptography, a timing attack is a side channel attack in which the attacker attempts to compromise a cryptosystem by analyzing the time taken to execute cryptographic algorithms. What is a timing attack? a timing attack is a side channel attack where an adversary observes how long an operation takes and uses that information to infer secret data.
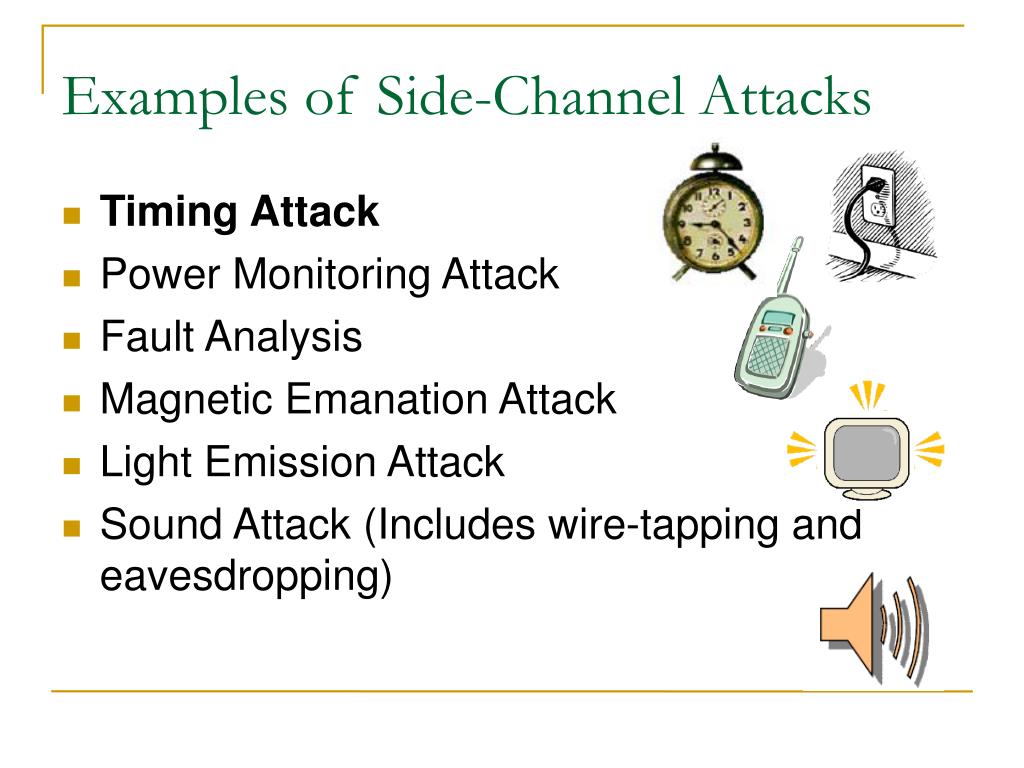
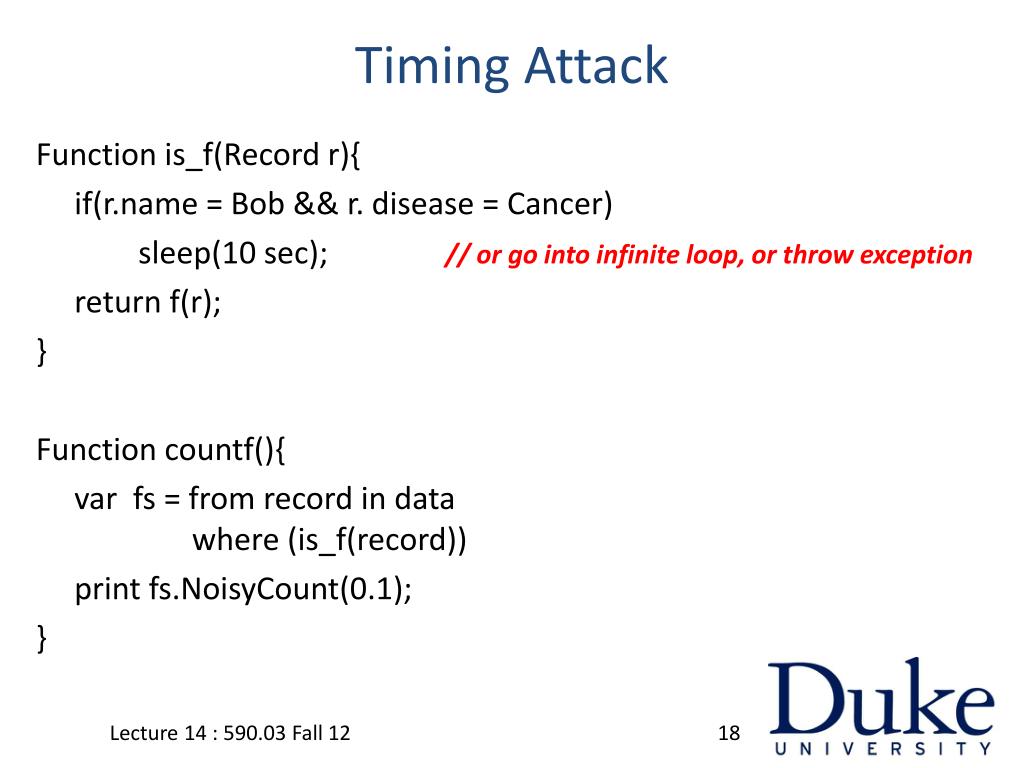
Ppt Side Channel Attack Timing Attack Powerpoint Presentation Free Understanding timing attack risks and implementing countermeasures—such as constant time algorithms and hardware defenses—is essential to securing the future of cryptography as quantum computing evolves. What is a timing attack? a timing attack is a type of side channel attack that exploits the amount of time a computer process runs to gain knowledge about or access a system. The basic goal of a timing attack is basically to be able to answer complicated questions or detect hidden functionalities by just checking the time differences in the responses from similar requests. A timing attack is a side channel attack that exploits the time variations in cryptographic operations to infer sensitive information. learn how timing attacks work, see examples, and discover how to protect against them with various methods.
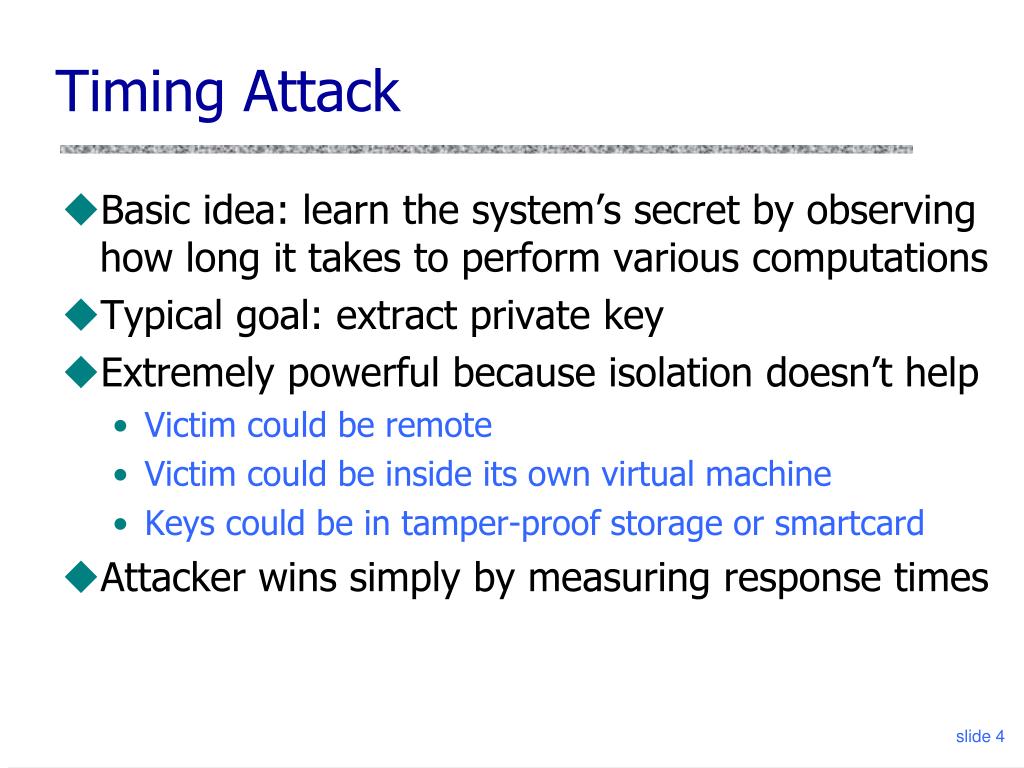
Ppt Timing Attacks Powerpoint Presentation Free Download Id 5804365 The basic goal of a timing attack is basically to be able to answer complicated questions or detect hidden functionalities by just checking the time differences in the responses from similar requests. A timing attack is a side channel attack that exploits the time variations in cryptographic operations to infer sensitive information. learn how timing attacks work, see examples, and discover how to protect against them with various methods. Paul kocher's 1996 timing attack showed how microsecond differences in execution time could leak private keys from rsa implementations. this tutorial recreates the attack journey from clean operation counting through noisy wall clock measurements to sophisticated engineering solutions. Timing attacks are fascinating yet concerning vulnerabilities in computer systems, particularly when it comes to security. at their core, these attacks exploit the time taken to execute cryptographic algorithms. let's dig in and understand the mechanics behind timing attacks!. Defending against timing attacks requires a multi layered approach combining constant time programming, architectural defenses, and monitoring systems. the fundamental principle is ensuring that execution time remains independent of secret data. What are timing attacks? timing attacks are a form of side channel attack where an adversary gains information from the time it takes for a system to respond to various inputs.

Timing Attack Encryption Of Message M With Rsa Algorithm Is C M E Mod Paul kocher's 1996 timing attack showed how microsecond differences in execution time could leak private keys from rsa implementations. this tutorial recreates the attack journey from clean operation counting through noisy wall clock measurements to sophisticated engineering solutions. Timing attacks are fascinating yet concerning vulnerabilities in computer systems, particularly when it comes to security. at their core, these attacks exploit the time taken to execute cryptographic algorithms. let's dig in and understand the mechanics behind timing attacks!. Defending against timing attacks requires a multi layered approach combining constant time programming, architectural defenses, and monitoring systems. the fundamental principle is ensuring that execution time remains independent of secret data. What are timing attacks? timing attacks are a form of side channel attack where an adversary gains information from the time it takes for a system to respond to various inputs.
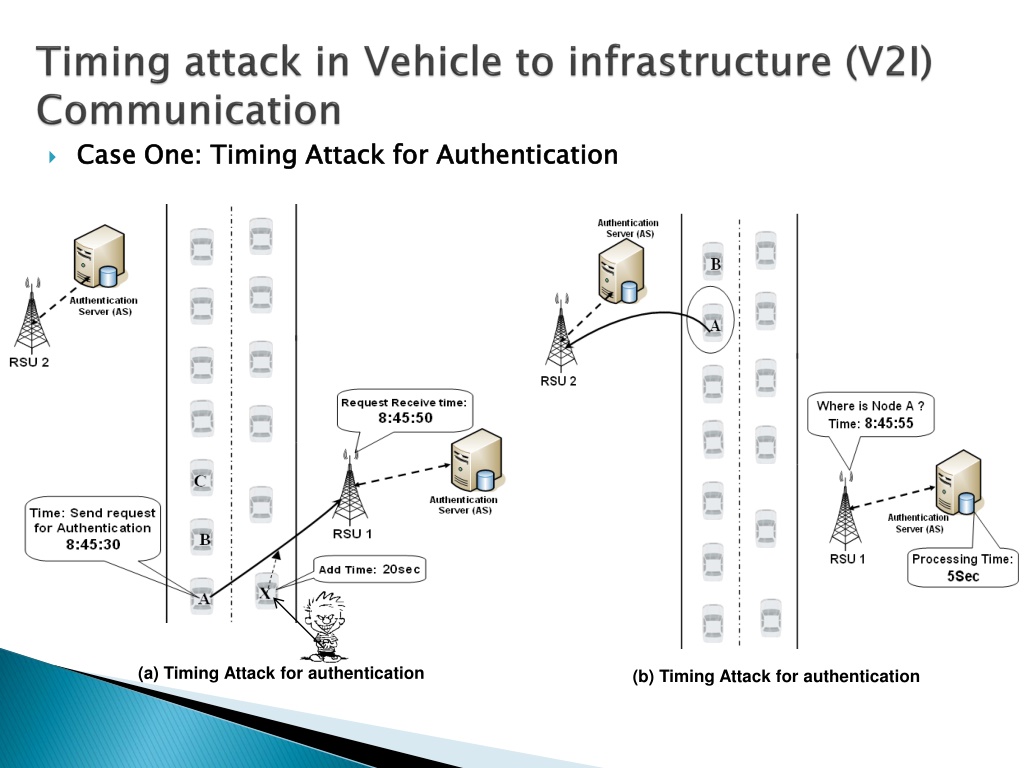
Ppt Timing Attack In Vehicular Network Powerpoint Presentation Free Defending against timing attacks requires a multi layered approach combining constant time programming, architectural defenses, and monitoring systems. the fundamental principle is ensuring that execution time remains independent of secret data. What are timing attacks? timing attacks are a form of side channel attack where an adversary gains information from the time it takes for a system to respond to various inputs.
Ppt Implementing Differential Privacy Side Channel Attacks
Comments are closed.