Computer And Information Security Chapter 6 Advanced Cryptanalysis
Computer And Information Security Chapter 6 Advanced Cryptanalysis Computer and information security chapter 6 advanced cryptanalysis 1. chapter 6: advanced cryptanalysis for there is nothing covered, that shall not be revealed; neither hid, that shall not be known. In previous chapters, we’ve seen a few simple cryptanalytic attacks. in this chapter, we kick it up a few notches and examine some relatively involved attacks. specifically, we’ll discuss the following cryptanalytic attacks.

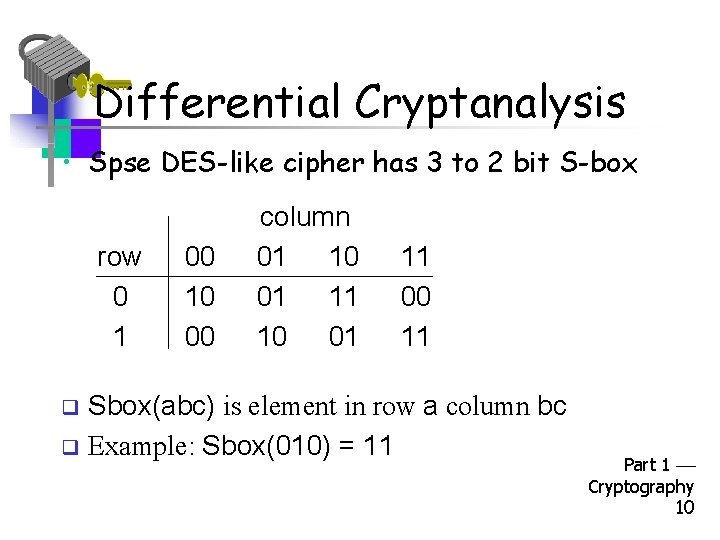
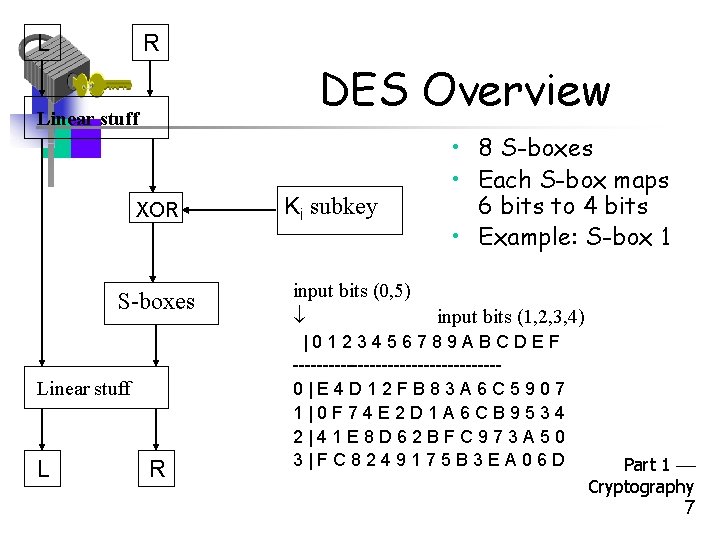
Computer And Information Security Chapter 6 Advanced Cryptanalysis In previous chapters, we’ve seen a few simple cryptanalytic attacks. in this chapter, we kick it up a few notches and examine some relatively involved attacks. specifically, we’ll discuss the following cryptanalytic attacks. Summary chapter includes a discussion of several advanced cryptanalytic techniques, each of which is illustrated by a concrete example. first, we discuss differential and linear cryptanalysis. Cryptanalysis is used to break cryptographic security systems and gain access to the contents of the encrypted messages, even if the cryptographic key is unknown. This chapter goes into assessing and mitigating vulnerabilities of systems related to cryptography, cryptographic lifecycle and methods, nonrepudiation, and data integrity.
Computer And Information Security Chapter 6 Advanced Cryptanalysis Cryptanalysis is used to break cryptographic security systems and gain access to the contents of the encrypted messages, even if the cryptographic key is unknown. This chapter goes into assessing and mitigating vulnerabilities of systems related to cryptography, cryptographic lifecycle and methods, nonrepudiation, and data integrity. This course reviews some failure cases in public key cryptography. it introduces some cryptanalysis techniques. it also presents fundamentals in cryptography such as interactive proofs. finally, it presents some techniques to validate the security of cryptographic primitives. Many users and even security administrators view strong security as an impediment to efficient and user friendly operation of an information system or use of information. Identify some key issues relating to the management of these services. this course provides an in depth understanding of modern cryptography, with emphasis on practical applications. Ece 646 – lecture 6 advanced encryption standard aes required reading • w. stallings, cryptography and network security, encryption standar.
Computer And Information Security Chapter 6 Advanced Cryptanalysis This course reviews some failure cases in public key cryptography. it introduces some cryptanalysis techniques. it also presents fundamentals in cryptography such as interactive proofs. finally, it presents some techniques to validate the security of cryptographic primitives. Many users and even security administrators view strong security as an impediment to efficient and user friendly operation of an information system or use of information. Identify some key issues relating to the management of these services. this course provides an in depth understanding of modern cryptography, with emphasis on practical applications. Ece 646 – lecture 6 advanced encryption standard aes required reading • w. stallings, cryptography and network security, encryption standar.
Computer And Information Security Chapter 6 Advanced Cryptanalysis Identify some key issues relating to the management of these services. this course provides an in depth understanding of modern cryptography, with emphasis on practical applications. Ece 646 – lecture 6 advanced encryption standard aes required reading • w. stallings, cryptography and network security, encryption standar.
Comments are closed.