Chapter 2 Ias Pdf Cryptography Cryptanalysis

Cryptography And Cryptanalysis Pdf Cryptanalysis Cryptography It discusses cryptanalysis, cryptography, and cryptology. it also covers symmetric and asymmetric encryption methods, classical ciphers including substitution and transposition ciphers, and examples like the caesar cipher. Cryptanalysis is used to break up authentication schemes, to break cryptographic protocols, and to find and correct weaknesses in encryption algorithms (ethical use).

Unit 3 Cryptanalysis Pdf Cryptanalysis Cryptography Cryptography and network security chapter 2 fifth edition by william stallings lecture slides by lawrie brown chapter 2. Curriculum 2 focus on cryptographic algorithms and their mathematical back ground, e.g., as an applied cryptography course in computer science, electrical engi neering or in an (undergraduate) math program. Chapter 2 classical encryption techniques nt of public key encryption in the 1970s. it remains by far the most w dely used of the two types of encryption. part o e examines a number of symmetric ciphers. in this chapter, we begin with a look at a general model for the symmetric encryption process; this will enable us to understand the con. Chapter 2 – classical encryption techniques • "i am fairly familiar with all the forms of secret writings, and am myself the author of a trifling monograph upon the subject, in which i analyze one hundred and sixty separate ciphers," said holmes.

Chapter 1 4 Pdf Cryptography Cryptanalysis Cryptanalysis and cryptology cryptanalysis is the study of breaking encryption without knowing the original message (plaintext) or the key. it uses techniques like brute force (trying all possible keys) or frequency analysis (looking for patterns in ciphertext) to crack encrypted data. Encryption and decryption should be fast; cryptanalysis should be slow. to quantify these statements, we need to understand how fast certain cryptographic algorithms run. These files were converted from the original pdf format, using pdftops, which comes with xpdf. you can either get all the parts at once, gzipped and tarred, or piecewise: enjoy!. Cryptanalysis of a polyalphabetic substitution cipher is split into two different problems, the first problem is to determine the period of the cipher, the second to reconstruct the t different substitution alphabets that have been used.
Cryptography Basics And Commercial Security Pdf Cryptography These files were converted from the original pdf format, using pdftops, which comes with xpdf. you can either get all the parts at once, gzipped and tarred, or piecewise: enjoy!. Cryptanalysis of a polyalphabetic substitution cipher is split into two different problems, the first problem is to determine the period of the cipher, the second to reconstruct the t different substitution alphabets that have been used.

Pdf Overview Of Cryptanalysis Techniques In Multivariate Public Key
Chapter 2 Ias Pdf Cryptography Cryptanalysis
Chapter Two Fundamentals Of Cryptography Pdf Cryptography

Lecture 2 Applied Cryptography Pdf Information Security

Chapter 2 Part 2 Pdf Cryptography Encryption
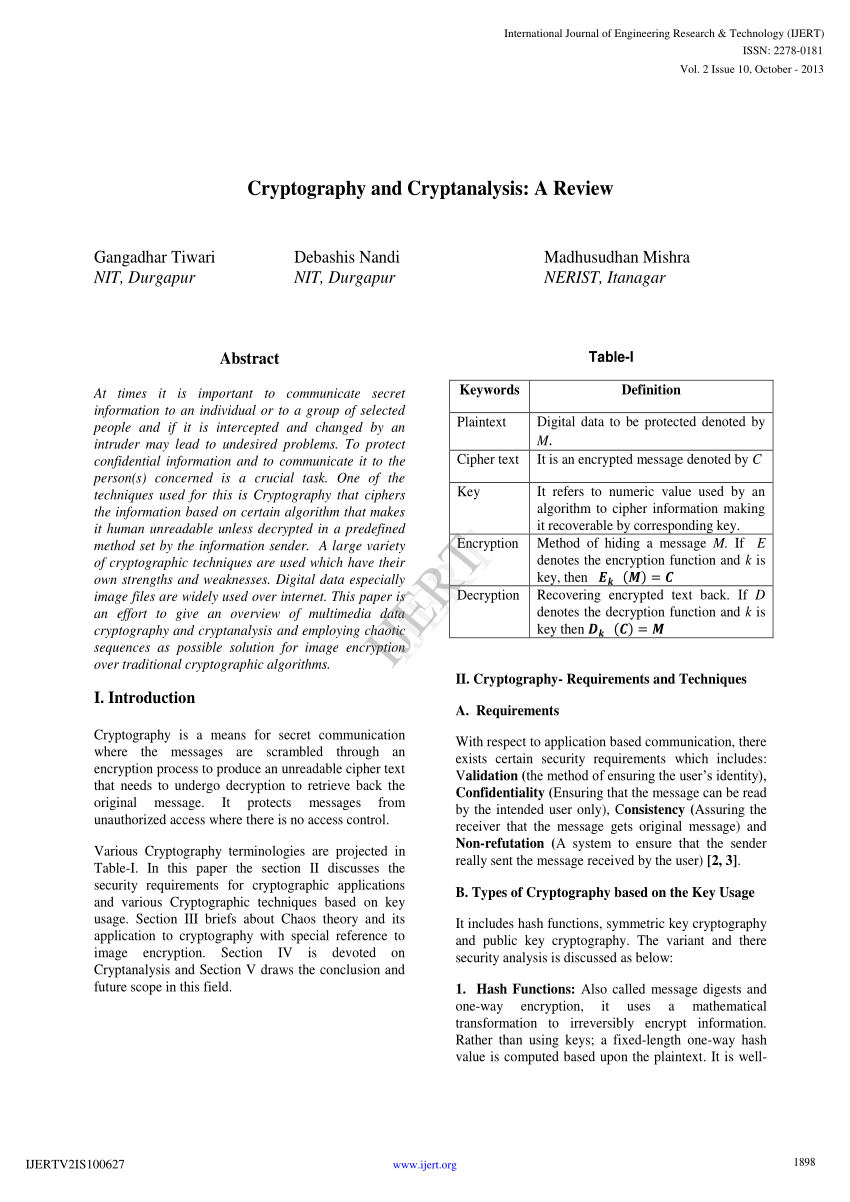
Pdf Cryptography And Cryptanalysis A Review

2 Mathematics Of Cryptographyy Chapter 2 Pptx

Perform Cryptanalysis Using Various Cryptanalysis Tools 1 Pdf
Chapter 2 Cryptography Pdf Cryptography Key Cryptography
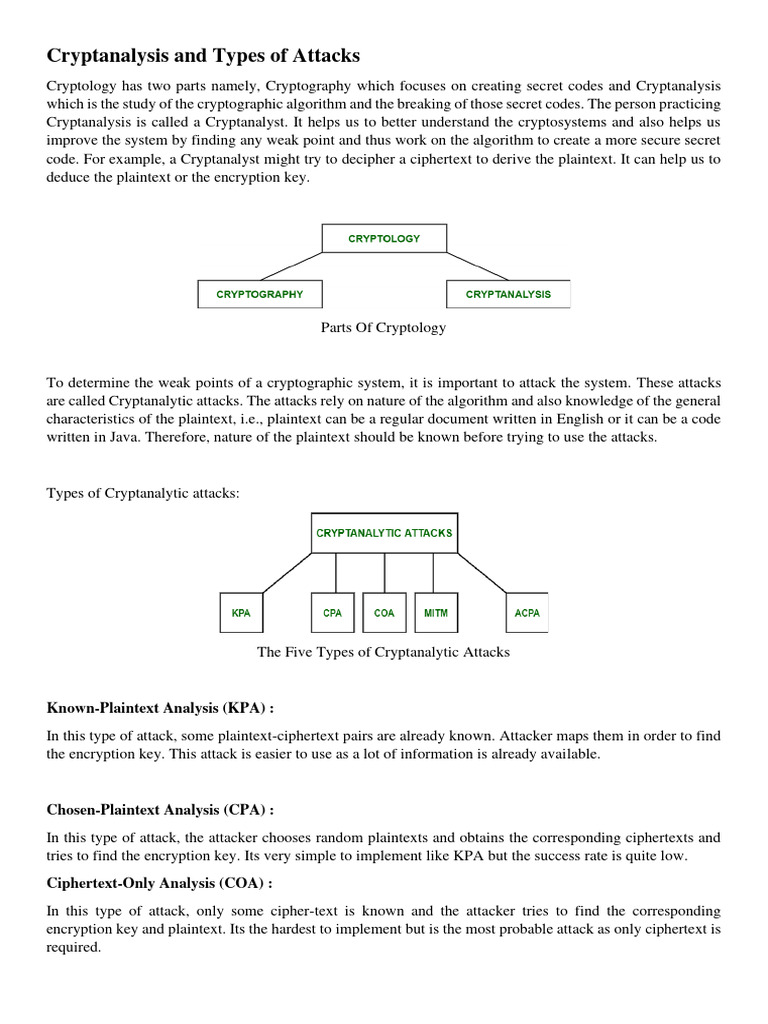
Cryptanalysis And Types Of Attacks Pdf Cryptography Cryptanalysis

Cryptography Module 1 Pdf Cryptography Cryptanalysis
Unit 2 Chapter 2 3 Pdf Cryptography Public Key Cryptography

Pdf Chapter 4 Cryptanalysis Using Shodhganga Inflibnet Ac In
Chapter 3 Cryptography Part 2 Pdf Public Key Cryptography

Ias Assignment Pdf Cipher Cryptography

Module 2 Note Cryptography Pdf

Chapter4 Pdf Cryptography Encryption

Cryptography Basics And Attacks Pdf Cryptography Cryptanalysis
Cryptanalysis Pptx
Cryptanalysis Notes Pdf Public Key Cryptography Cryptanalysis

Ias Report Pdf Encryption Key Cryptography

Chapter 2 Pdf Cryptography Encryption

Chapter Two Part One Pdf Cryptography Key Cryptography

Cryptography 2 Pdf

Cryptanalysis Pdf Cryptanalysis Military Communications
Ch 2 Cryptography Pdf Cryptography Cryptanalysis

Ch2 Cryptography Concepts 1 1 Pdf Cryptography Encryption

Chapter 02 Pdf Cryptography Key Cryptography

Chapter 2 Cryptography Pdf Cryptography Key Cryptography

Chapter 8 Cryptography Lanjutan Pdf

Cryptanalysis On Aes Pdf Secure Communication Applied Mathematics
Comments are closed.