Common Authentication Methods Used For Network Security

Common Authentication Methods Used For Network Security Based on their associated factors, there are three primary types of authentication: knowledge, possession, and inherence. each has its pros and cons, but when used in conjunction, these types of authentication provide powerful protection from unauthorized access. Explore different types of authentication in network security, including passwords, biometrics, and multi factor authentication, to safeguard sensitive data and systems.
Types Of Authentication Methods Used For Network Security There are many different network authentication methods, each with their own security and complexities. these techniques range from password based to two factor, biometric, certificate based, and token based authentication. Network access control: restricts access to private and enterprise networks to authorized users and devices only. email and cloud services: protects sensitive user data using password based and multi factor authentication mechanisms. This article explores popular network authentication methods such as passwords, certificates, and more, providing examples of their real life applications and discussing their pros and cons. One layer of security that all networks and applications need is authentication. read up on six authentication types, from 2fa to biometrics to certificates.

Types Of Authentication Methods Used For Network Security This article explores popular network authentication methods such as passwords, certificates, and more, providing examples of their real life applications and discussing their pros and cons. One layer of security that all networks and applications need is authentication. read up on six authentication types, from 2fa to biometrics to certificates. The most commonly used authentication methods in cybersecurity include password based authentication, multi factor authentication (mfa), biometric authentication, and token based authentication. Most enterprise networks use a mix of tools to handle authentication and support strong network security. they might check passwords, look at device certificates, or talk to a directory like active directory. Authentication methods are diverse, ranging from traditional passwords to cutting edge biometric systems. this article dives deep into the various authentication methods used in network security, their mechanisms, strengths, weaknesses, and the evolving landscape of threats. Learn about the different types of authentication methods, techniques, and systems in cybersecurity to verify identities and secure digital assets.

Types Of Authentication Methods Used For Network Security The most commonly used authentication methods in cybersecurity include password based authentication, multi factor authentication (mfa), biometric authentication, and token based authentication. Most enterprise networks use a mix of tools to handle authentication and support strong network security. they might check passwords, look at device certificates, or talk to a directory like active directory. Authentication methods are diverse, ranging from traditional passwords to cutting edge biometric systems. this article dives deep into the various authentication methods used in network security, their mechanisms, strengths, weaknesses, and the evolving landscape of threats. Learn about the different types of authentication methods, techniques, and systems in cybersecurity to verify identities and secure digital assets.
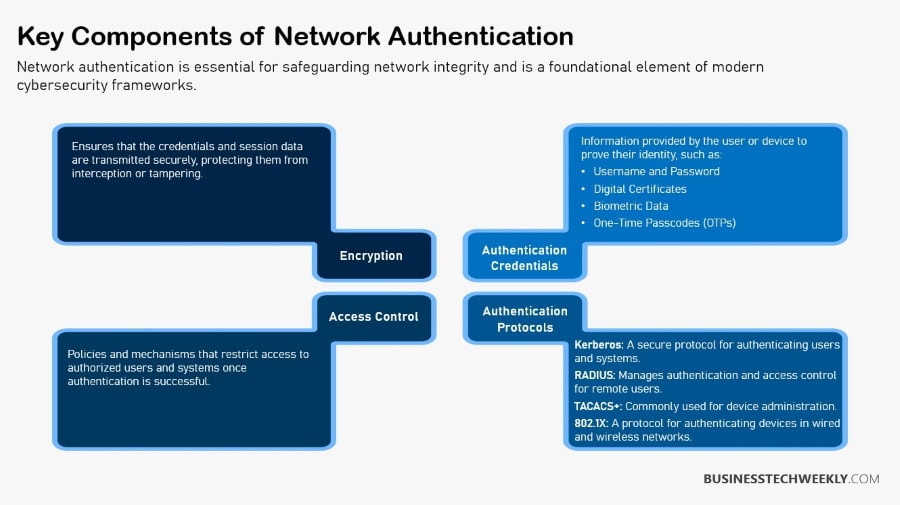
Network Authentication Methods You Should Know Businesstechweekly Authentication methods are diverse, ranging from traditional passwords to cutting edge biometric systems. this article dives deep into the various authentication methods used in network security, their mechanisms, strengths, weaknesses, and the evolving landscape of threats. Learn about the different types of authentication methods, techniques, and systems in cybersecurity to verify identities and secure digital assets.

Network Authentication Methods You Should Know Businesstechweekly
Comments are closed.