Asymmetric Encryption Blockchain 101
Understanding Asymmetric Encryption What Is It This tutorial introduces the principles of asymmetric encryption and demonstrates its practical applications in blockchain systems, providing users with a hands on understanding of how it protects and authenticates digital data. Learn what asymmetric cryptography is in blockchain. understand how public and private keys work, their role in secure transactions, and why they are key to your financial autonomy.
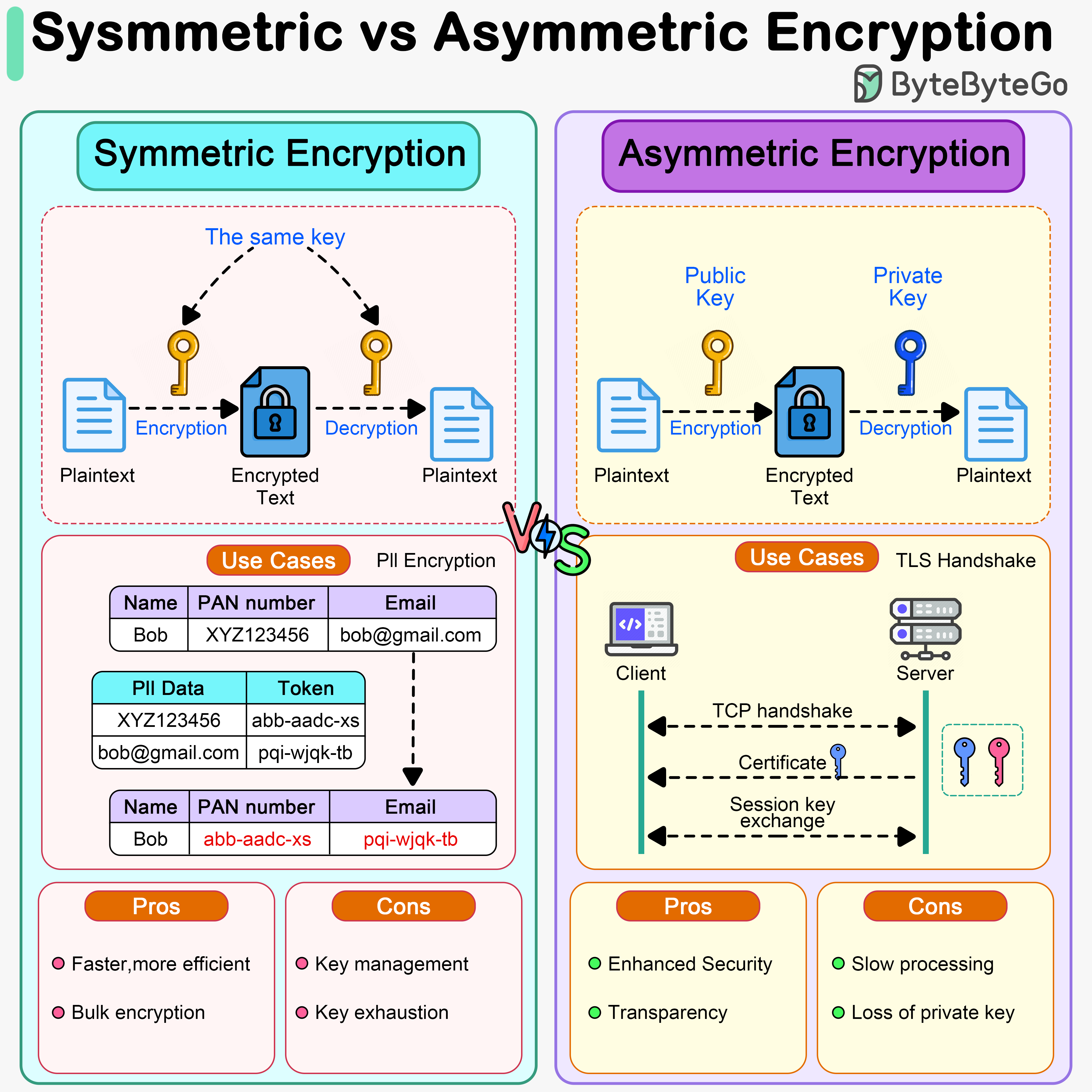
Bytebytego Symmetric Vs Asymmetric Encryption In asymmetric key cryptography, there are two keys, also known as key pairs: a public key and a private key. the public key is publicly distributed. anyone can use this public key to encrypt messages, but only the recipient, who holds the corresponding private key, can decrypt those messages. Asymmetric encryption is a cryptographic system that uses both public keys and private keys. public key encryption is when a message is encrypted with a recipient’s public key. the message can only be decrypted with the corresponding private key. Explore how asymmetric encryption secures data through public and private keys. learn its role in digital signatures, blockchain, and web3 security. Using public and private key pairings, asymmetric cryptography algorithms secure blockchain networks. rsa, ecc, and elgamal are examples.

Diagram Of Asymmetric Encryption Quizlet Explore how asymmetric encryption secures data through public and private keys. learn its role in digital signatures, blockchain, and web3 security. Using public and private key pairings, asymmetric cryptography algorithms secure blockchain networks. rsa, ecc, and elgamal are examples. Asymmetric cryptographic algorithm uses public and private key pairs for encryption and digital signatures. learn how it secures blockchain wallets, transactions, smart contracts, and cross chain communication in web3. Asymmetric cryptography is useful because it uses two different keys: a private key and a public key. the private key is used for signing messages and decrypting data, while the public key is used for validating signatures and encrypting data. Asymmetric cryptography, also known as public key cryptography, is one of the key components of blockchain technology. this form of cryptography allows everyone to verify the integrity of transactions, protect funds from hackers and much more. Learn the principles of asymmetric cryptography, including public and private keys, essential for encrypting data securely in blockchain technology.
10 Examples Of Asymmetric Encryption Vivid Examples Asymmetric cryptographic algorithm uses public and private key pairs for encryption and digital signatures. learn how it secures blockchain wallets, transactions, smart contracts, and cross chain communication in web3. Asymmetric cryptography is useful because it uses two different keys: a private key and a public key. the private key is used for signing messages and decrypting data, while the public key is used for validating signatures and encrypting data. Asymmetric cryptography, also known as public key cryptography, is one of the key components of blockchain technology. this form of cryptography allows everyone to verify the integrity of transactions, protect funds from hackers and much more. Learn the principles of asymmetric cryptography, including public and private keys, essential for encrypting data securely in blockchain technology.
Comments are closed.