Asymmetric Cryptography Bitcoin Blockchain And Cryptoassets

What Is Asymmetric Cryptography Cybernoz Cybersecurity News Asymmetric cryptography so far: symmetric cryptography di decryption is inverse algorithm of encryption e's idea (1975): asymmetric encryption key to encrypt and key to decrypt a message are not identical but how?. University of basel lecture bitcoin, blockchain and cryptoassets. prof. dr. fabian schär lecture: 3.3 asymmetric cryptography more.

What Is Asymmetric Cryptography Learn what asymmetric cryptography is in blockchain. understand how public and private keys work, their role in secure transactions, and why they are key to your financial autonomy. Ap cybersecurity · unit 5 · topic 5.4 asymmetric cryptography & pki: trust without pre shared secrets symmetric crypto needs a shared secret. asymmetric crypto creates trust between strangers. master the math without math intuition behind public private key pairs, understand how rsa and ecc differ, trace a tls handshake end to end, and see how certificate authorities make the web's trust. Asymmetric or public private key cryptography was developed in the 1970s. prior to then, the only cryptography available was symmetric. let’s take a look at how symmetric cryptography works to gain some insight into why asymmetric cryptography was developed and the advantages it has. Asymmetric encryption, also called public key encryption, is an essential factor in sending and receiving transactions in bitcoin and other cryptocurrencies. it uses two key pairs for the sender and recipient: a public key they both know and a private key for each.
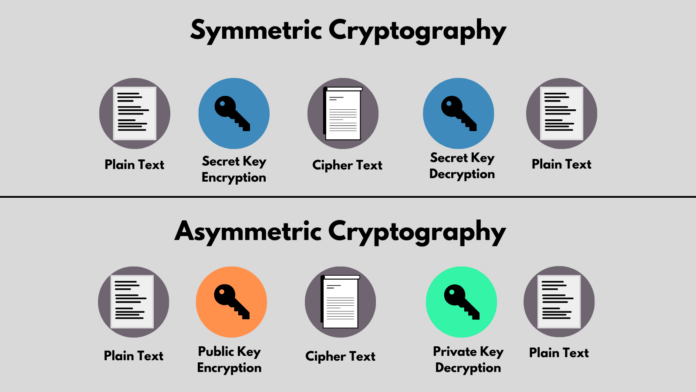
What Is Asymmetric Cryptography Asymmetric or public private key cryptography was developed in the 1970s. prior to then, the only cryptography available was symmetric. let’s take a look at how symmetric cryptography works to gain some insight into why asymmetric cryptography was developed and the advantages it has. Asymmetric encryption, also called public key encryption, is an essential factor in sending and receiving transactions in bitcoin and other cryptocurrencies. it uses two key pairs for the sender and recipient: a public key they both know and a private key for each. Asymmetric cryptographic algorithm uses public and private key pairs for encryption and digital signatures. learn how it secures blockchain wallets, transactions, smart contracts, and cross chain communication in web3. Blockchain and cryptocurrencies: blockchain technologies, including bitcoin and ethereum, use asymmetric key cryptography. for example, the ownership of bitcoin is established through digital signatures using asymmetric key cryptography. In this paper, the authors proposed a system framework that combined blockchain and supply chain, and analyzed and explained each process in the supply chain in detail. At the heart of these innovations lie asymmetric algorithms, a fundamental component of modern cryptography. in this article, we delve into the world of asymmetric algorithms, focusing on their applications in today’s dynamic landscape of cryptocurrency and blockchain technologies.
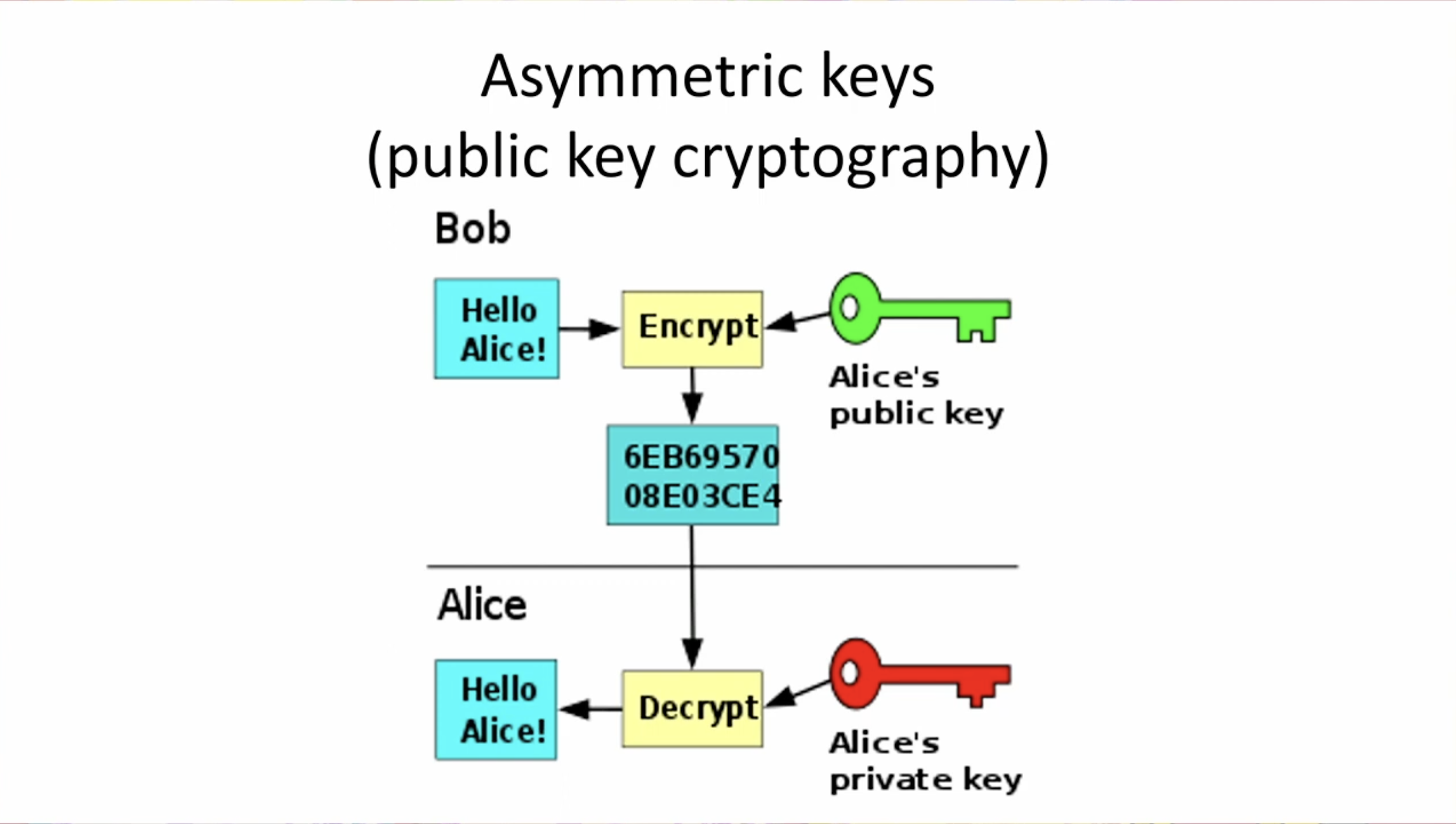
Asymmetric Cryptography Fundamentals Asymmetric cryptographic algorithm uses public and private key pairs for encryption and digital signatures. learn how it secures blockchain wallets, transactions, smart contracts, and cross chain communication in web3. Blockchain and cryptocurrencies: blockchain technologies, including bitcoin and ethereum, use asymmetric key cryptography. for example, the ownership of bitcoin is established through digital signatures using asymmetric key cryptography. In this paper, the authors proposed a system framework that combined blockchain and supply chain, and analyzed and explained each process in the supply chain in detail. At the heart of these innovations lie asymmetric algorithms, a fundamental component of modern cryptography. in this article, we delve into the world of asymmetric algorithms, focusing on their applications in today’s dynamic landscape of cryptocurrency and blockchain technologies.
Difference Between Symmetric And Asymmetric Cryptography In this paper, the authors proposed a system framework that combined blockchain and supply chain, and analyzed and explained each process in the supply chain in detail. At the heart of these innovations lie asymmetric algorithms, a fundamental component of modern cryptography. in this article, we delve into the world of asymmetric algorithms, focusing on their applications in today’s dynamic landscape of cryptocurrency and blockchain technologies.
Comments are closed.