Application Dependency Mapping For Microsegmentation

Cloud Application Dependency Mapping Device42 Nutanix flow delivers a robust, software defined approach to segmentation and microsegmentation, using policy driven controls mapped directly to your applications. this article provides a practical deep dive for architects, network engineers, and infrastructure engineers. Implement akamai guardicore microsegmentation with claude code. map application dependencies, enforce zero trust policies, and prevent lateral movement.

Cloud Application Dependency Mapping Device42 Dependency mapping is the process of gathering information about all your underly ing application dependencies and presenting it in a way you can easily understand it. Agentless application dependency mapping tool that automatically builds and provides end to end visibility for all virtual, physical and cloud components to troubleshoot performance issues, plan dr and microsegmentation and cloud migration assessments. Find out what is dependency mapping, how and why businesses use it, and how to use dependency mapping on aws. It should provide a live application dependency map that shows how your applications connect and communicate. this is the first step to using micro segmentation — it enables you to understand application dependencies and model security policies so you can effectively control communications.
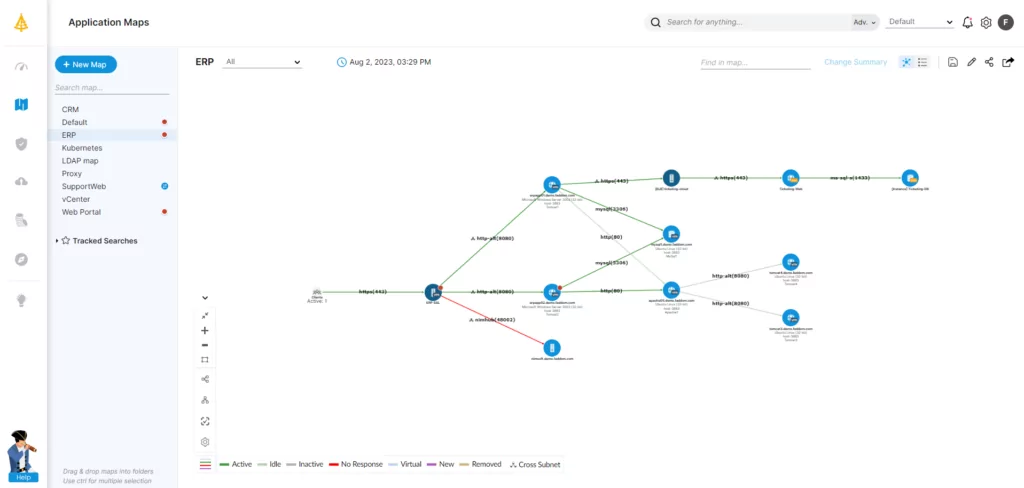
Application Dependency Mapping The Complete Guide Find out what is dependency mapping, how and why businesses use it, and how to use dependency mapping on aws. It should provide a live application dependency map that shows how your applications connect and communicate. this is the first step to using micro segmentation — it enables you to understand application dependencies and model security policies so you can effectively control communications. What is microsegmentation? microsegmentation is a security architecture and operational practice that restricts lateral movement by controlling which services, workloads, and processes can communicate. it is not just vlans or coarse acls; it ties policies to identities, service intent, and observed behavior. In this article, we will explore how application aware segmentation works, its benefits, common challenges, and best practices for implementation using leading tools and technologies. Get a visual application dependency map of all your business assets, identify your most valuable assets, develop security policies to proactively defend them, and identify compromised assets for quick remediation. Planning a security strategy to protect critical assets starts with seeing and understanding application dependencies. learn how application dependency mapping works and why it’s critical to protecting key business assets within your data center and cloud environments.

Application Dependency Mapping The Complete Guide Faddom What is microsegmentation? microsegmentation is a security architecture and operational practice that restricts lateral movement by controlling which services, workloads, and processes can communicate. it is not just vlans or coarse acls; it ties policies to identities, service intent, and observed behavior. In this article, we will explore how application aware segmentation works, its benefits, common challenges, and best practices for implementation using leading tools and technologies. Get a visual application dependency map of all your business assets, identify your most valuable assets, develop security policies to proactively defend them, and identify compromised assets for quick remediation. Planning a security strategy to protect critical assets starts with seeing and understanding application dependencies. learn how application dependency mapping works and why it’s critical to protecting key business assets within your data center and cloud environments.
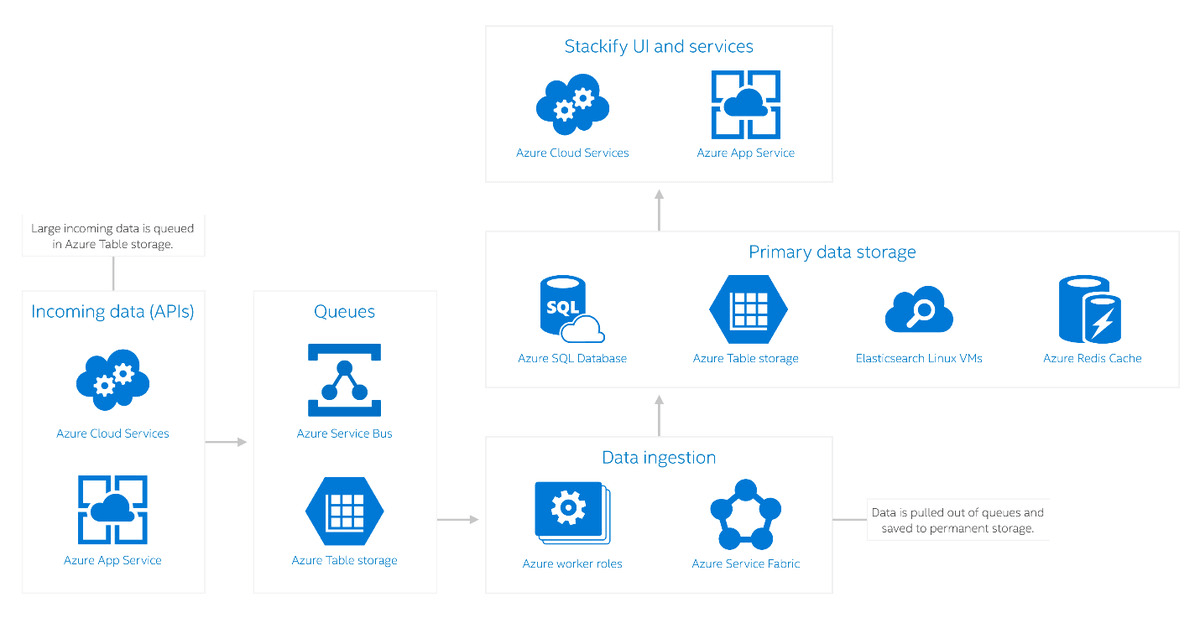
Application Dependency Mapping Types Tools And Tips Get a visual application dependency map of all your business assets, identify your most valuable assets, develop security policies to proactively defend them, and identify compromised assets for quick remediation. Planning a security strategy to protect critical assets starts with seeing and understanding application dependencies. learn how application dependency mapping works and why it’s critical to protecting key business assets within your data center and cloud environments.

Application Dependency Mapping Methods Benefits Tips Cortex
Comments are closed.