Cisco Secure Workload Application Dependency Mapping Discovery

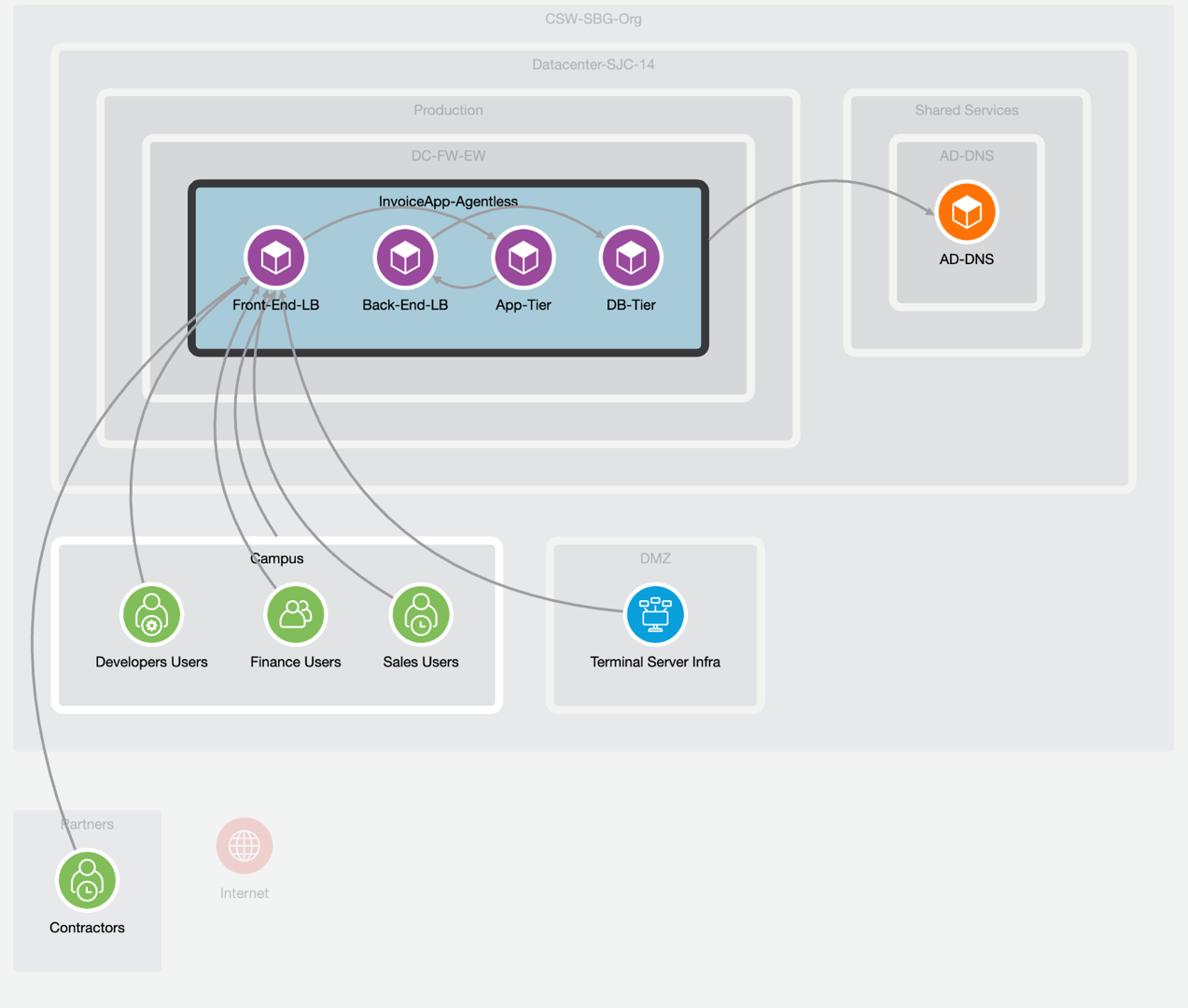
Application Discovery Dependency Mapping Explained Faqs Algosec On secure workload, the user can define policy manually or perform automatic policy discovery with adm (application dependency mapping). once the policies are validated and enforced, they are pushed to firewall management center (fmc). Solving the segmentation puzzle with secure workload! in a world of application workloads deployed anywhere, at any time, and with multi cloud solutions, applying network security controls is no longer a trivial task.

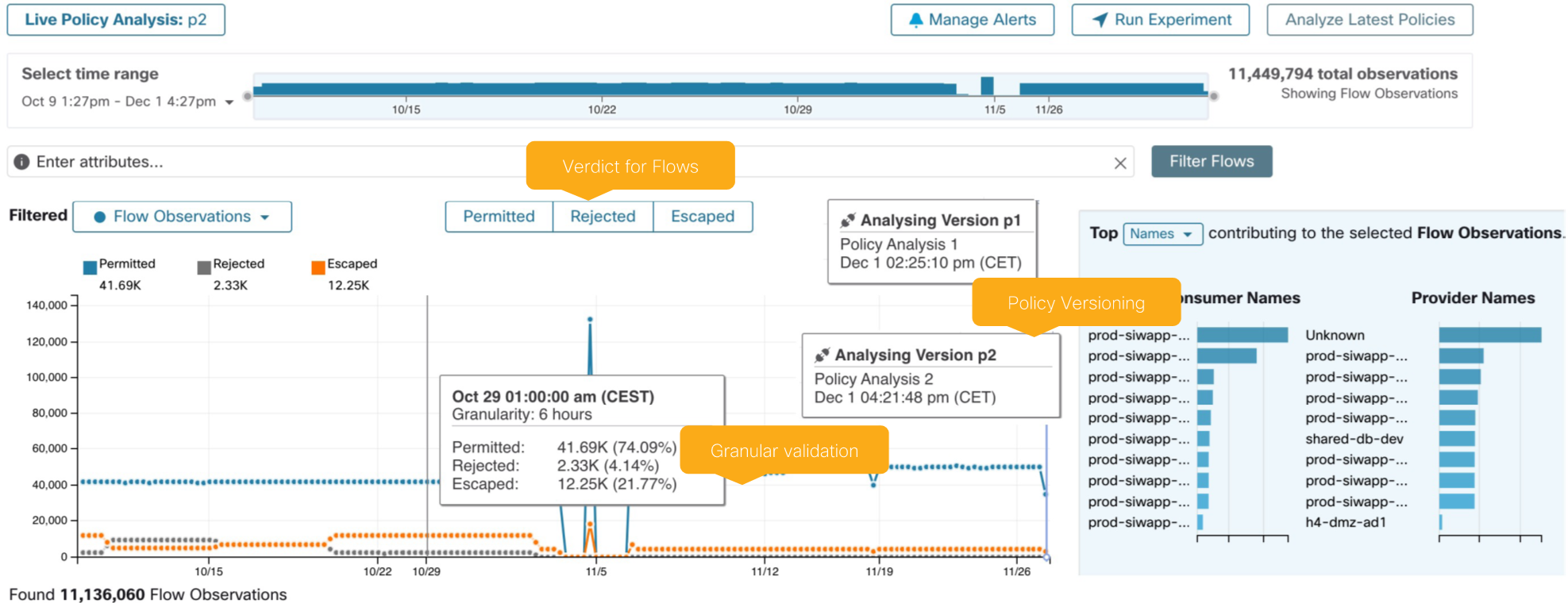
Application Discovery Dependency Mapping Explained Faqs Algosec In this video we will leverage application dependency mapping (adm) to identify what systems communicate on what ports. Dependency mapping: turning data into insight one of the most powerful features in cisco secure workload is dependency mapping. this turns raw flow data into a visual map of. The training emphasizes the operationalization of cisco secure workload as a core component of a modern security stack—empowering engineers to detect and refine escaped flows, map application dependencies, and enforce dynamic, risk informed policy across their enterprise. Review administrative and management tasks necessary to operate, support and manage cisco secure workload describe how cisco secure workload telemetry data is utilized in the flows corpus construct effective policies based on discovered flows and application dependency mapping (adm).

Application Discovery Dependency Mapping Explained Faqs Algosec The training emphasizes the operationalization of cisco secure workload as a core component of a modern security stack—empowering engineers to detect and refine escaped flows, map application dependencies, and enforce dynamic, risk informed policy across their enterprise. Review administrative and management tasks necessary to operate, support and manage cisco secure workload describe how cisco secure workload telemetry data is utilized in the flows corpus construct effective policies based on discovered flows and application dependency mapping (adm). Cisco secure workload firewall enforcement agents, data flow mapping, and advanced policy deployment, cswadv, is a 5 day course exploring telemetry data, the flows corpus, and how cisco secure workload firewall agent provides enforcement. Ai policy discovery (adm) inclusion filters are used to whitelist the flows used in adm runs. you can create inclusion filters that matches only the required subset of flows after the adm is enabled. a combination of inclusion and exclusion filters can be used for adm runs. This course will provide the details and hands on activities necessary to successfully deploy, manage, and troubleshoot policies in cisco secure workload. the course qualifies for 40 cisco continuing education credits (ce). This course will provide the details and hands on activities necessary to successfully deploy, manage, and troubleshoot policies in cisco secure workload.

Application Discovery Dependency Mapping Explained Faqs Algosec Cisco secure workload firewall enforcement agents, data flow mapping, and advanced policy deployment, cswadv, is a 5 day course exploring telemetry data, the flows corpus, and how cisco secure workload firewall agent provides enforcement. Ai policy discovery (adm) inclusion filters are used to whitelist the flows used in adm runs. you can create inclusion filters that matches only the required subset of flows after the adm is enabled. a combination of inclusion and exclusion filters can be used for adm runs. This course will provide the details and hands on activities necessary to successfully deploy, manage, and troubleshoot policies in cisco secure workload. the course qualifies for 40 cisco continuing education credits (ce). This course will provide the details and hands on activities necessary to successfully deploy, manage, and troubleshoot policies in cisco secure workload.
Secure Workload Deep Dive Of Secure Workload Firewall Integration This course will provide the details and hands on activities necessary to successfully deploy, manage, and troubleshoot policies in cisco secure workload. the course qualifies for 40 cisco continuing education credits (ce). This course will provide the details and hands on activities necessary to successfully deploy, manage, and troubleshoot policies in cisco secure workload.
Secure Workload Deep Dive Of Secure Workload Firewall Integration
Comments are closed.