Aes Wireless Keyboard Template Attack For Eavesdropping

Black Hat Talk Aes Wireless Keyboard Template Attack For Wireless keyboards with aes is not secure. manufacturers need to defend against reverse engineering and side channel attacks. thanks! any questions?. Explore aes wireless keyboard vulnerabilities through template attacks, focusing on firmware analysis, side channel attacks, and eavesdropping techniques for enhanced cybersecurity awareness.
An Eavesdropping Attack What It Is And How To Prevent It Nordvpn We provide a method to analyze specifically the internal behavior of the target device and provide a template generation method for side channel attacks. it also shows how you can extract the encryption key from other wireless keyboards using the same chip. In today's mobile world, wireless technology is used in many places. we use it to access online while on the go, connect mobile accessories to a pc, listen t. Aes wireless keyboard template attack for eavesdropping [blackhat asia 2018]. In this paper, we use template attack and support vector machine to perform a side channel attack on aes 128 and recover the cipher key from a power trace of a hardware encrypting device.

What Is An Eavesdropping Attack Ipvanish Aes wireless keyboard template attack for eavesdropping [blackhat asia 2018]. In this paper, we use template attack and support vector machine to perform a side channel attack on aes 128 and recover the cipher key from a power trace of a hardware encrypting device. In this paper, we provide a detailed analysis of cpa and template attacks on masked implementations of bitsliced aes, targeting a 32 bit platform through the chipwhisperer side channel acquisition tool. Conclusion: wireless keyboards have security flaws that disrupt radio communication, giving a malicious user complete access to the computer to which the keyboard is connected. an attacker. Our analysis revealed critical vulnerabilities in keyboard apps from eight out of the nine vendors in which we could exploit that vulnerability to completely reveal the contents of users’ keystrokes in transit. most of the vulnerable apps can be exploited by an entirely passive network eavesdropper. The syss radio hack box 2.0 is a proof of concept software tool to demonstrate the replay and keystroke injection vulnerabilities of the wireless keyboards cherry b.unlimited aes and cherry b.unlimited 3.0.
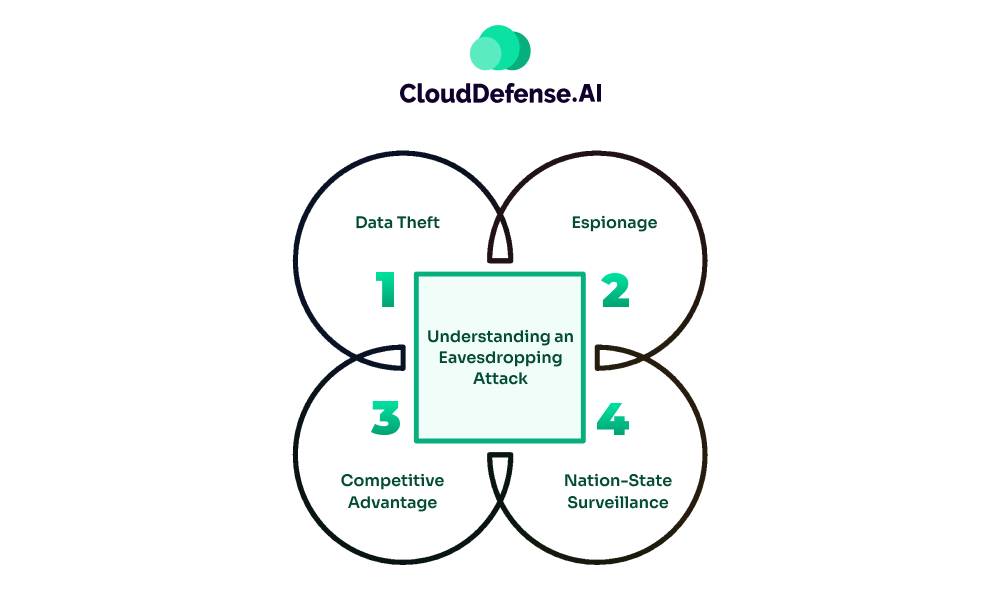
What Is An Eavesdropping Attack In this paper, we provide a detailed analysis of cpa and template attacks on masked implementations of bitsliced aes, targeting a 32 bit platform through the chipwhisperer side channel acquisition tool. Conclusion: wireless keyboards have security flaws that disrupt radio communication, giving a malicious user complete access to the computer to which the keyboard is connected. an attacker. Our analysis revealed critical vulnerabilities in keyboard apps from eight out of the nine vendors in which we could exploit that vulnerability to completely reveal the contents of users’ keystrokes in transit. most of the vulnerable apps can be exploited by an entirely passive network eavesdropper. The syss radio hack box 2.0 is a proof of concept software tool to demonstrate the replay and keystroke injection vulnerabilities of the wireless keyboards cherry b.unlimited aes and cherry b.unlimited 3.0.
Comments are closed.