What Is An Eavesdropping Attack

Eavesdropping Attack Finance Reference Eavesdropping attacks, also called sniffing or snooping attacks, are a major concern regarding cyber security. attackers exploit vulnerabilities in communication channels to access confidential information, which can include personal details, financial data, and proprietary business information. An eavesdropping attack gives criminals or spies access to personal data and business networks, helping them extract data, steal money, and potentially commit fraud.

Eavesdropping Attack Everything You Should Know An eavesdropping attack occurs when a hacker intercepts, deletes, or modifies data that is transmitted between two devices. eavesdropping, also known as sniffing or snooping, relies on unsecured network communications to access data in transit between devices. Eavesdropping attacks operate by exploiting vulnerabilities in network communications. attackers often begin by identifying unsecured network connections, such as public wi fi, where data is transmitted without encryption. What exactly is an eavesdropping attack? an eavesdropping attack occurs when unauthorized actors secretly capture data as it travels between two communicating devices. What is an eavesdropping attack? an eavesdropping attack is a cyberattack in which an unauthorized party secretly intercepts, monitors, or captures data while it is being transmitted between systems or users. in some cases, the attacker only listens.
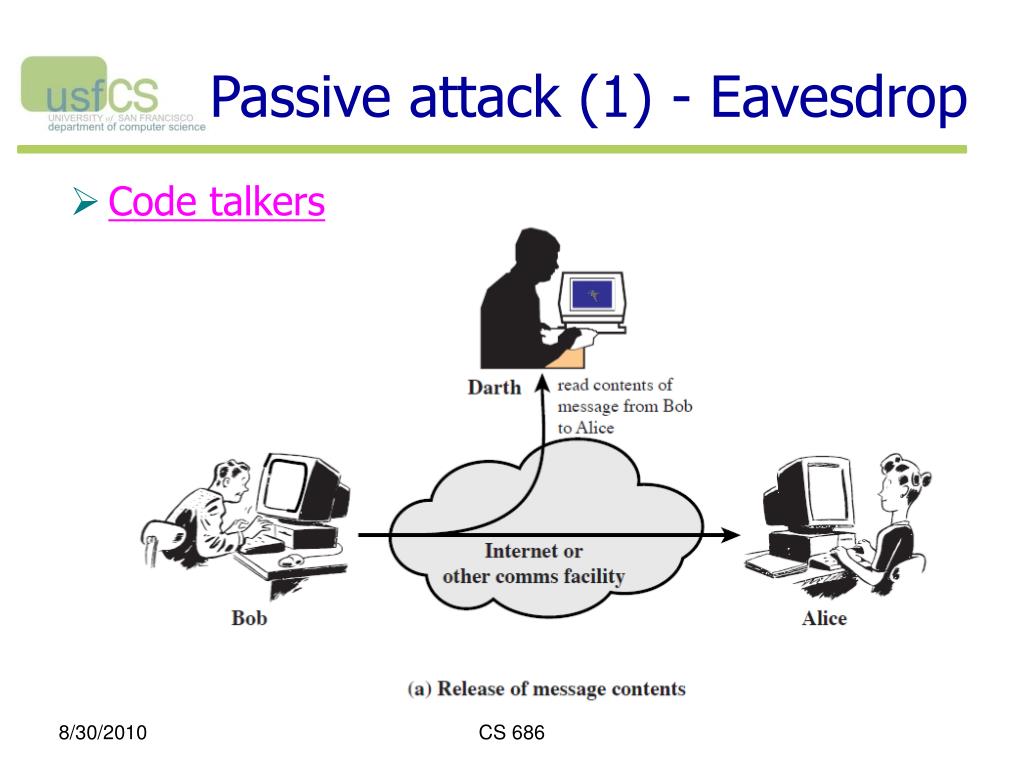
Eavesdropping Attack What exactly is an eavesdropping attack? an eavesdropping attack occurs when unauthorized actors secretly capture data as it travels between two communicating devices. What is an eavesdropping attack? an eavesdropping attack is a cyberattack in which an unauthorized party secretly intercepts, monitors, or captures data while it is being transmitted between systems or users. in some cases, the attacker only listens. What is an eavesdropping attack? an eavesdropping attack is a malicious attempt to intercept, delete, or alter data sent between devices. this cyberattack is also called sniffing or a snooping attack. launching these attacks often requires technical skills and social engineering. What is an eavesdropping attack? in cybersecurity, an eavesdropping attack is a malicious attempt to intercept and access data transmitted over a network without authorization. Attackers use eavesdropping techniques to secretly capture sensitive information such as passwords, messages, financial details, and private data—often without the victim ever realizing it. understanding how eavesdropping works is essential for protecting your online privacy. An eavesdropping attack is the unauthorized interception and monitoring of private communications over a network. attackers use this technique to capture sensitive information, including credentials and financial details, without altering the data.

Eavesdropping Attack What is an eavesdropping attack? an eavesdropping attack is a malicious attempt to intercept, delete, or alter data sent between devices. this cyberattack is also called sniffing or a snooping attack. launching these attacks often requires technical skills and social engineering. What is an eavesdropping attack? in cybersecurity, an eavesdropping attack is a malicious attempt to intercept and access data transmitted over a network without authorization. Attackers use eavesdropping techniques to secretly capture sensitive information such as passwords, messages, financial details, and private data—often without the victim ever realizing it. understanding how eavesdropping works is essential for protecting your online privacy. An eavesdropping attack is the unauthorized interception and monitoring of private communications over a network. attackers use this technique to capture sensitive information, including credentials and financial details, without altering the data.
Comments are closed.