Aes Key Extraction Method

Aes Key Generation Pdf Encryption Key Cryptography It demonstrates how a side channel attack can be used to extract the key used by the mainstream aes algorithm when it is naively implemented. lastly, some countermeasures are implemented so that such attacks are less effective. Its ability to recover aes keys from memory dumps makes it invaluable in both forensic investigations and security research. understanding how to effectively use aeskeyfind, including its capabilities and limitations, is crucial for forensic practitioners.
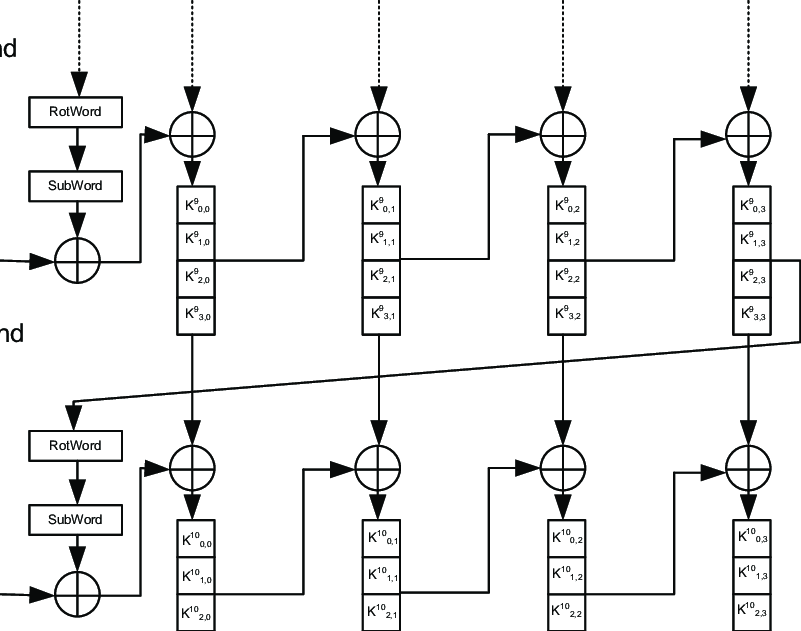
File Aes Key Schedule 128 Bit Wikipedia 60 Off This paper is a short summary of a real world aes key extraction performed on a military grade fpga marketed as 'virtually unbreakable' and 'highly secure'. This program illustrates automatic techniques for locating 128 bit and 256 bit aes keys in a captured memory image. the program uses various algorithms and also performs a simple entropy test to filter out blocks that are not keys. This study investigates the effectiveness of correlation power analysis (cpa) using the hamming weight model to extract aes encryption keys in a fully software simulated environment. This innovative approach enables the extraction of aes keys from an atmega328p microcontroller by analyzing its power consumption traces during encryption operations.

Aes Key Extraction Setup Download Scientific Diagram This study investigates the effectiveness of correlation power analysis (cpa) using the hamming weight model to extract aes encryption keys in a fully software simulated environment. This innovative approach enables the extraction of aes keys from an atmega328p microcontroller by analyzing its power consumption traces during encryption operations. We demonstrate the extraction of an aes secret key from flash memory on the atmega328 microcontroller (the microcontroller used on the popular arduino genuino uno board). The file in the video expired so here are the two files you need: mega.nz file pb9gds5a#lb3fil6ead2ebtpbqwpu8 vncjfrxzgxmvuuzl0s uq mega.nz fil. The purpose of this article is to look at approaches for extracting aes encryption keys from ram. next time you run a tool like bulk extractor or aes keyfind, you will have a better. We demonstrated that it is possible to extract the aes key from the actel microsemi proasic3 chip in a time of 0.01 seconds using a new side channel analysis technique called pipeline emission analysis (pea).
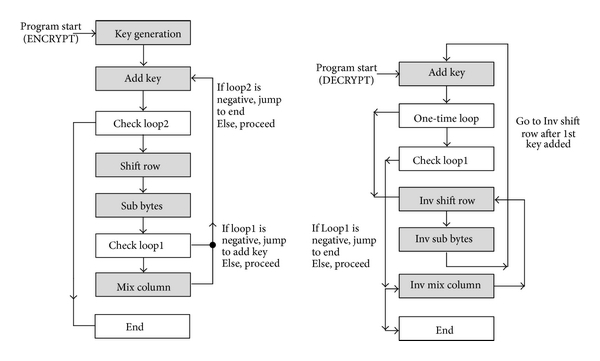
Encryption Method Aes We demonstrate the extraction of an aes secret key from flash memory on the atmega328 microcontroller (the microcontroller used on the popular arduino genuino uno board). The file in the video expired so here are the two files you need: mega.nz file pb9gds5a#lb3fil6ead2ebtpbqwpu8 vncjfrxzgxmvuuzl0s uq mega.nz fil. The purpose of this article is to look at approaches for extracting aes encryption keys from ram. next time you run a tool like bulk extractor or aes keyfind, you will have a better. We demonstrated that it is possible to extract the aes key from the actel microsemi proasic3 chip in a time of 0.01 seconds using a new side channel analysis technique called pipeline emission analysis (pea).
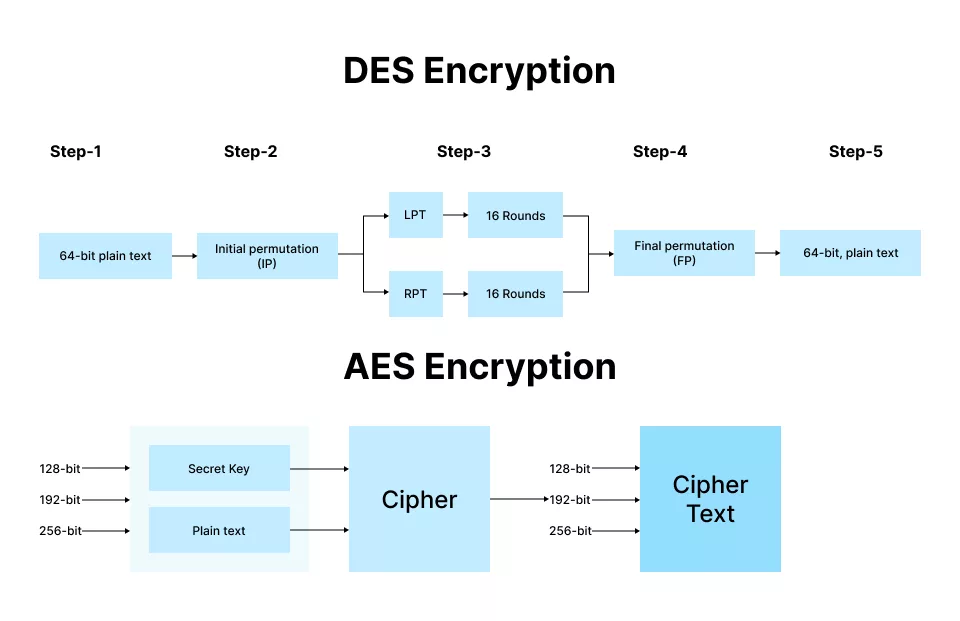
Rsa Aes Encryption Key Differences Explained 54 Off The purpose of this article is to look at approaches for extracting aes encryption keys from ram. next time you run a tool like bulk extractor or aes keyfind, you will have a better. We demonstrated that it is possible to extract the aes key from the actel microsemi proasic3 chip in a time of 0.01 seconds using a new side channel analysis technique called pipeline emission analysis (pea).
Comments are closed.