Aes Key Expansion

Module 4 Aes Key Expansion Download Free Pdf Cryptography Learn how aes expands a short key into a number of separate round keys for encryption and decryption. see the key schedule algorithm, the round constants, and the s box for different aes variants. Learn how to expand a single initial key into a series of round keys for aes encryption and decryption. see the mathematical representation, the key expansion process, and an example of aes 128 key expansion.
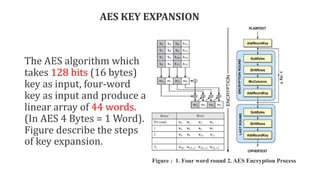
Github Cryptography Team Aes Key Expansion An Implementation Of The The aes key expansion algorithm takes as input a four word (16 byte) key and produces a linear array of 44 words (176 bytes). this is sufficient to provide a four word round key for the initial addroundkey stage and each of the 10 rounds of the cipher. Learn about the structure, features, and steps of aes, a block cipher with a block length of 128 bits and a variable key length. see python and perl implementations of the key expansion algorithm and the byte substitution step. Three members of the rijndael family are specifed in this standard: aes 128, aes 192, and aes 256. each of them transforms data in blocks of 128 bits, and the numerical suffx indicates the bit length of the associated cryptographic keys. Byte substitution, permutation, arithmetic operations over a finite field, and xor with a key are the main four functions in aes with key expansion to be focused on and discussed.

Aes 512 Key Expansion Download Scientific Diagram Three members of the rijndael family are specifed in this standard: aes 128, aes 192, and aes 256. each of them transforms data in blocks of 128 bits, and the numerical suffx indicates the bit length of the associated cryptographic keys. Byte substitution, permutation, arithmetic operations over a finite field, and xor with a key are the main four functions in aes with key expansion to be focused on and discussed. This document describes the key schedule and key expansion process in the aes implementation. the key schedule is responsible for transforming the initial cipher key (128, 192, or 256 bits) into an expanded key that provides a unique round key for each encryption round. The document describes the aes key expansion process. the aes algorithm takes a 128 bit key as input and expands it into a linear array of 44 words using a key schedule. Learn how aes key expansion generates round keys from the initial cipher key for each round of encryption. explore the algorithmic steps, technical aspects, and optimization techniques for aes key expansion. Learn how to perform key expansion for aes (rijndael) with different key sizes. see the common operations, the key schedule routine, and the c code examples.
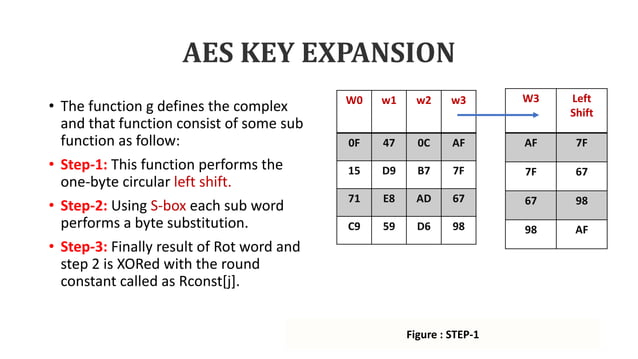
Aes Key Expansion Pptx This document describes the key schedule and key expansion process in the aes implementation. the key schedule is responsible for transforming the initial cipher key (128, 192, or 256 bits) into an expanded key that provides a unique round key for each encryption round. The document describes the aes key expansion process. the aes algorithm takes a 128 bit key as input and expands it into a linear array of 44 words using a key schedule. Learn how aes key expansion generates round keys from the initial cipher key for each round of encryption. explore the algorithmic steps, technical aspects, and optimization techniques for aes key expansion. Learn how to perform key expansion for aes (rijndael) with different key sizes. see the common operations, the key schedule routine, and the c code examples.
Aes Key Expansion Pptx Learn how aes key expansion generates round keys from the initial cipher key for each round of encryption. explore the algorithmic steps, technical aspects, and optimization techniques for aes key expansion. Learn how to perform key expansion for aes (rijndael) with different key sizes. see the common operations, the key schedule routine, and the c code examples.
Comments are closed.