Acoustic Side Channel Attack
Acoustic Side Channel Attack On Keyboards Based On Typing Patterns Acoustic side channel attacks (ascas) exploit the sound produced by keyboards and other devices to infer sensitive information without breaching software or network defenses. In his book spycatcher, former mi5 operative peter wright discusses use of an acoustic attack against egyptian hagelin cipher machines in 1956. the attack was codenamed "engulf".

Pitti Article A Practical Deep Learning Based Acoustic Side Channel In this article, we will break down what ai acoustic side channel attacks are, how they work, and why they are uniquely dangerous in today’s environment. we will examine verified real world cases, from zoom based keystroke recovery to ultrasonic command injection into voice assistants. Acoustic side channel attacks on keyboards can bypass security measures in many systems that use keyboards as one of the input devices. these attacks aim to reveal users’ sensitive information by targeting the sounds made by their keyboards as they type. This paper focuses on acoustic side channel attack and surveys the methods and techniques employed in the attack; we will also see some of the different devices which can be under the threat of such attack and finally countermeasures against this attack, which helps in reducing the risk. Acoustic side channel attacks (asca) have emerged as a significant threat, exploiting sound emissions from devices to infer sensitive information such as keystrokes or conversations.
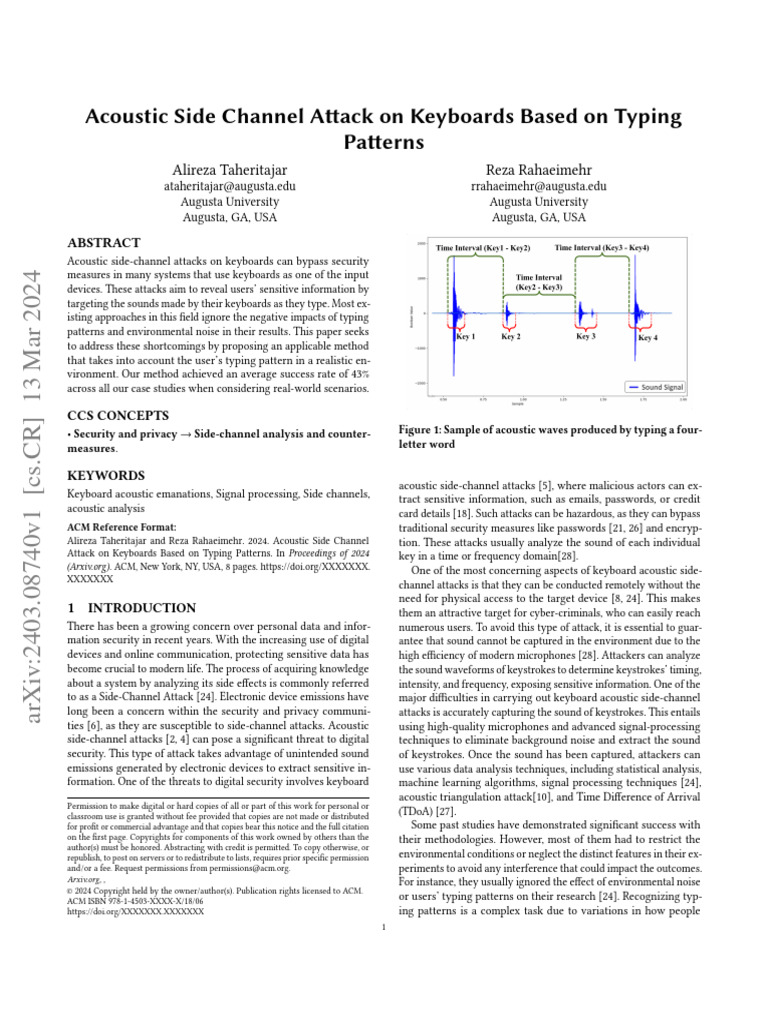
Acoustic Side Channel Attack This paper focuses on acoustic side channel attack and surveys the methods and techniques employed in the attack; we will also see some of the different devices which can be under the threat of such attack and finally countermeasures against this attack, which helps in reducing the risk. Acoustic side channel attacks (asca) have emerged as a significant threat, exploiting sound emissions from devices to infer sensitive information such as keystrokes or conversations. Discover how acoustic side channel attacks utilize keyboard typing patterns to breach security. this article delves into the mechanisms, implications, and prevention strategies essential for cybersecurity. Most electronic devices utilize keyboards to receive inputs, including sensitive information such as authentication credentials, personal and private data, emails, plans, etc. however, these systems are susceptible to acoustic side channel attacks. researchers have. We report the first active acoustic side channel attack. speakers are used to emit human inaudible acoustic signals, and the echo is recorded via microphones, turning the acoustic system of. Researchers from british universities have developed a deep learning model that can eavesdrop on keyboard keystrokes using a microphone or zoom with high accuracy. the attack exploits the sound differences between different keys and can leak sensitive information such as passwords or messages.

Eavesdropping On Keyboard Keystrokes Kaspersky Official Blog Discover how acoustic side channel attacks utilize keyboard typing patterns to breach security. this article delves into the mechanisms, implications, and prevention strategies essential for cybersecurity. Most electronic devices utilize keyboards to receive inputs, including sensitive information such as authentication credentials, personal and private data, emails, plans, etc. however, these systems are susceptible to acoustic side channel attacks. researchers have. We report the first active acoustic side channel attack. speakers are used to emit human inaudible acoustic signals, and the echo is recorded via microphones, turning the acoustic system of. Researchers from british universities have developed a deep learning model that can eavesdrop on keyboard keystrokes using a microphone or zoom with high accuracy. the attack exploits the sound differences between different keys and can leak sensitive information such as passwords or messages.
Comments are closed.