What Are Acoustic Side Channel Attacks In Cybersecurity
Improving Acoustic Side Channel Attacks On Keyboards Using Transformers An acoustic side channel attack occurs when an attacker captures and analyzes sound emissions from a device to extract sensitive information. every keystroke on a keyboard produces a unique acoustic signature, shaped by the key’s position, the device’s materials, and the typing style. Acoustic side channel attacks (ascas) exploit the sound produced by keyboards and other devices to infer sensitive information without breaching software or network defenses.
Acoustic Side Channel Attack On Keyboards Based On Typing Patterns Acoustic side channel attacks present a sophisticated threat that capitalizes on the sounds emitted by keyboards during typing. this method exploits the acoustic signatures of keystrokes to decipher user inputs, potentially exposing sensitive information such as passwords and personal messages. Acoustic cryptanalysis is a type of side channel attack that exploits sounds emitted by computers or other devices. most of the modern acoustic cryptanalysis focuses on the sounds produced by computer keyboards and internal computer components, but historically it has also been applied to impact printers, and electromechanical deciphering machines. Scas are sophisticated hacking methods that crack cryptographic algorithms by analyzing auxiliary systems used in encryption. these attacks use signals emitted by devices, such as electromagnetic waves, power consumption, and even the sounds from keyboards and printers. Researchers have demonstrated that attackers can analyze the unique acoustic signatures of disk operations to determine exactly which files are being accessed. this article explores the mechanics of these attacks, detection methods, and mitigation strategies.

What Are Acoustic Side Channel Attacks In Cybersecurity Scas are sophisticated hacking methods that crack cryptographic algorithms by analyzing auxiliary systems used in encryption. these attacks use signals emitted by devices, such as electromagnetic waves, power consumption, and even the sounds from keyboards and printers. Researchers have demonstrated that attackers can analyze the unique acoustic signatures of disk operations to determine exactly which files are being accessed. this article explores the mechanics of these attacks, detection methods, and mitigation strategies. Learn how acoustic side channel attacks steal sensitive data by analyzing computer fan and hdd sounds—and what cybersecurity teams can do to stop them. Acoustic side channel attacks on keyboards can bypass security measures in many systems that use keyboards as one of the input devices. these attacks aim to reveal users’ sensitive information by targeting the sounds made by their keyboards as they type. The acoustic emanations from keyboards provide a side channel attack from which an attacker can recover sensitive user information, such as passwords and personally identifiable information. Most electronic devices utilize keyboards to receive inputs, including sensitive information such as authentication credentials, personal and private data, emails, plans, etc. however, these systems are susceptible to acoustic side channel attacks. researchers have.
Acoustic Side Channel Attacks Ascas Current Affairs Editorial Learn how acoustic side channel attacks steal sensitive data by analyzing computer fan and hdd sounds—and what cybersecurity teams can do to stop them. Acoustic side channel attacks on keyboards can bypass security measures in many systems that use keyboards as one of the input devices. these attacks aim to reveal users’ sensitive information by targeting the sounds made by their keyboards as they type. The acoustic emanations from keyboards provide a side channel attack from which an attacker can recover sensitive user information, such as passwords and personally identifiable information. Most electronic devices utilize keyboards to receive inputs, including sensitive information such as authentication credentials, personal and private data, emails, plans, etc. however, these systems are susceptible to acoustic side channel attacks. researchers have.
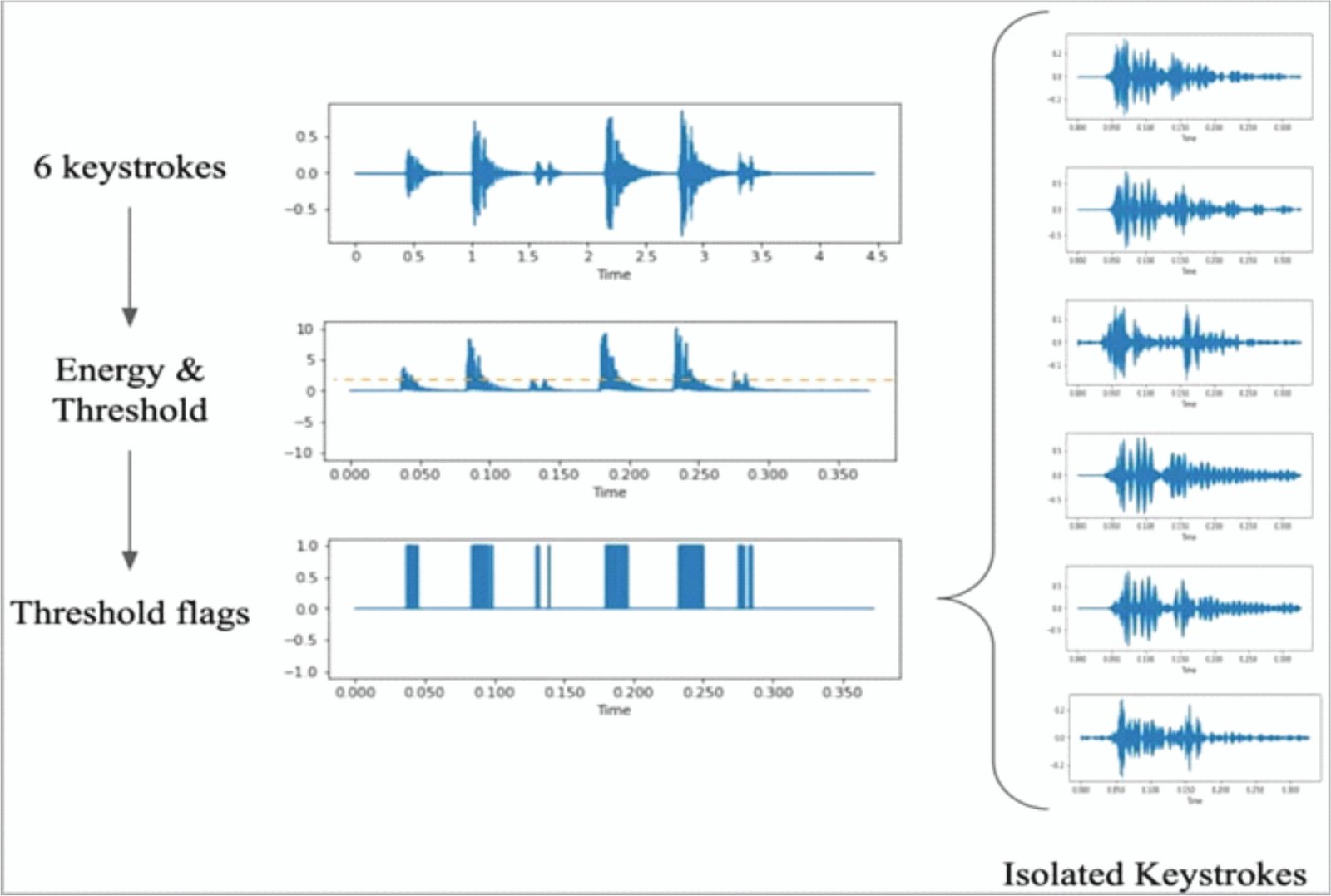
Acoustic Side Channel Attacks Ascas Current Affairs Editorial The acoustic emanations from keyboards provide a side channel attack from which an attacker can recover sensitive user information, such as passwords and personally identifiable information. Most electronic devices utilize keyboards to receive inputs, including sensitive information such as authentication credentials, personal and private data, emails, plans, etc. however, these systems are susceptible to acoustic side channel attacks. researchers have.
Comments are closed.