Acoustic Keyboard Side Channel Attack Let Attackers Steal Data
Acoustic Side Channel Attack In this attack, threat actors utilize the device’s sound emissions to extract sensitive data. cybersecurity researchers, alireza taheritajar and reza rahaeimehr from augusta university recently discovered a new acoustic keyboard side channel attack that lets hackers steal sensitive data. Our results prove the practicality of these side channel attacks via off the shelf equipment and algorithms. we discuss a series of mitigation methods to protect users against these series of attacks.

Tag Side Channel Attack Ars Technica A team of researchers from british universities has trained a deep learning model that can steal data from keyboard keystrokes recorded using a microphone with an accuracy of 95%. This paper presents the findings of a pilot study investigating the feasibility of recognizing keyboard keystroke sounds using convolutional neural networks (cnns) as a means of simulating an acoustic side channel attack aimed at recovering typed text. This survey paper thoroughly reviews existing research, explaining why such attacks are feasible, the applicable threat models, and the methodologies employed to launch and enhance these attacks. The acoustic emanations from keyboards provide a side channel attack from which an attacker can recover sensitive user information, such as passwords and personally identifiable.

Tag Side Channel Attack Ars Technica This survey paper thoroughly reviews existing research, explaining why such attacks are feasible, the applicable threat models, and the methodologies employed to launch and enhance these attacks. The acoustic emanations from keyboards provide a side channel attack from which an attacker can recover sensitive user information, such as passwords and personally identifiable. Acoustic side channel attacks present a sophisticated threat that capitalizes on the sounds emitted by keyboards during typing. this method exploits the acoustic signatures of keystrokes to decipher user inputs, potentially exposing sensitive information such as passwords and personal messages. In this paper, we survey the literature available on acoustic side channel attacks on keyboards. we propose a novel deep learning based method to perform an effective attack on a keyboard. This study demonstrates the feasibility of using deep learning for acoustic keystroke detection, contributing significantly to cybersecurity measures against side channel attacks. Acoustic side channel attacks (ascas) exploit sound em anations from electronic devices, particularly keyboards, to infer sensitive information like passwords and pins.
Mitigating A Token Length Side Channel Attack In Our Ai Products Acoustic side channel attacks present a sophisticated threat that capitalizes on the sounds emitted by keyboards during typing. this method exploits the acoustic signatures of keystrokes to decipher user inputs, potentially exposing sensitive information such as passwords and personal messages. In this paper, we survey the literature available on acoustic side channel attacks on keyboards. we propose a novel deep learning based method to perform an effective attack on a keyboard. This study demonstrates the feasibility of using deep learning for acoustic keystroke detection, contributing significantly to cybersecurity measures against side channel attacks. Acoustic side channel attacks (ascas) exploit sound em anations from electronic devices, particularly keyboards, to infer sensitive information like passwords and pins.
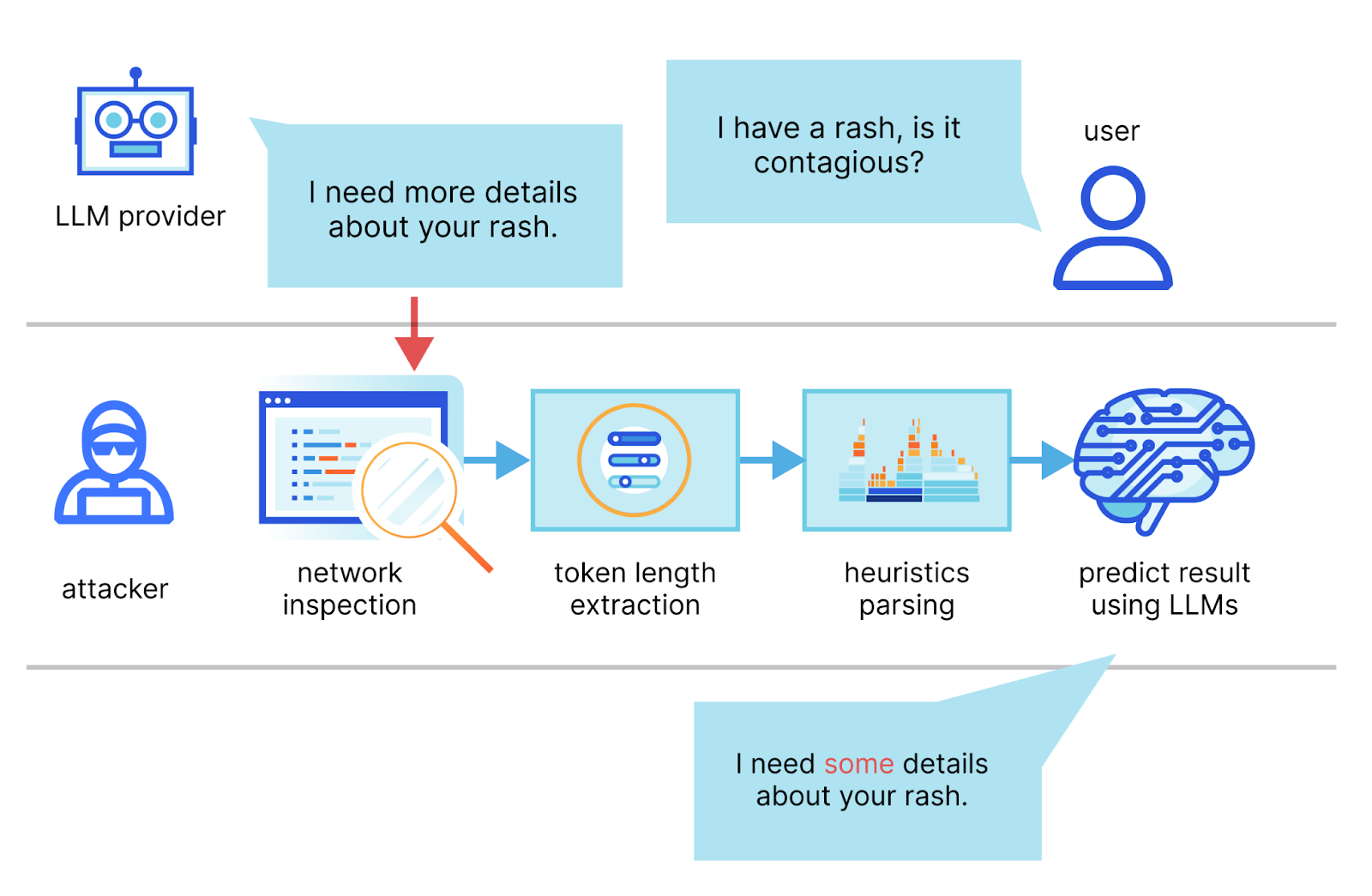
Mitigating A Token Length Side Channel Attack In Our Ai Products This study demonstrates the feasibility of using deep learning for acoustic keystroke detection, contributing significantly to cybersecurity measures against side channel attacks. Acoustic side channel attacks (ascas) exploit sound em anations from electronic devices, particularly keyboards, to infer sensitive information like passwords and pins.

Mitigating A Token Length Side Channel Attack In Our Ai Products
Comments are closed.